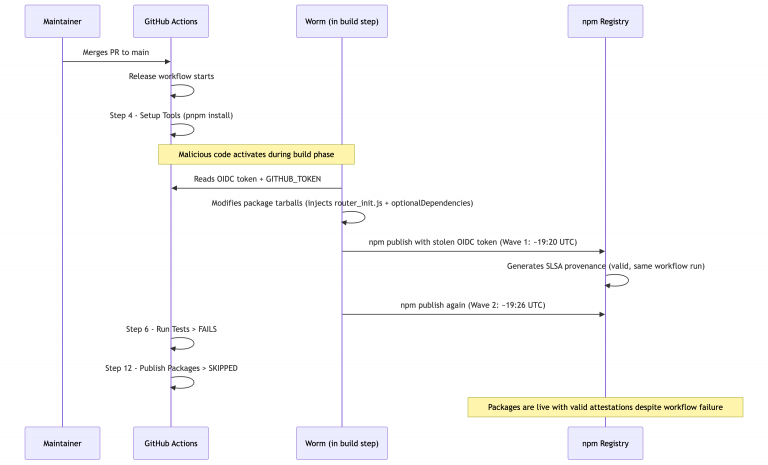
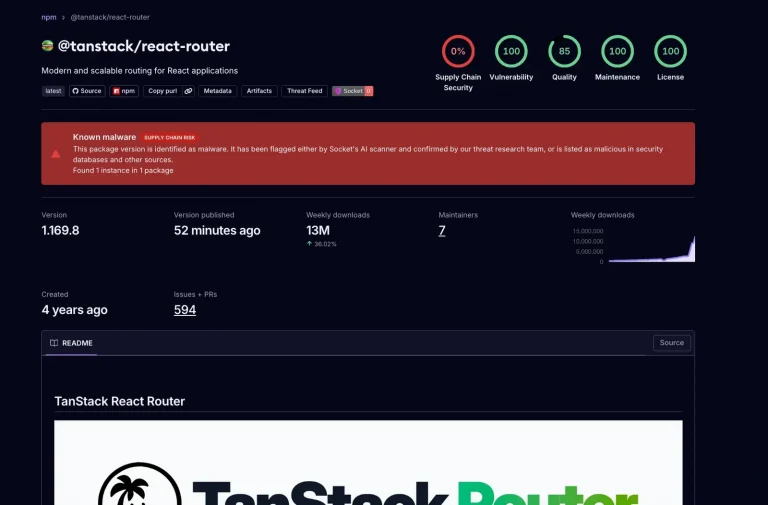
This week, the TanStack ecosystem—a cornerstone of modern web development—suffered a sophisticated security breach. Exploiting a procedural...
Do Son
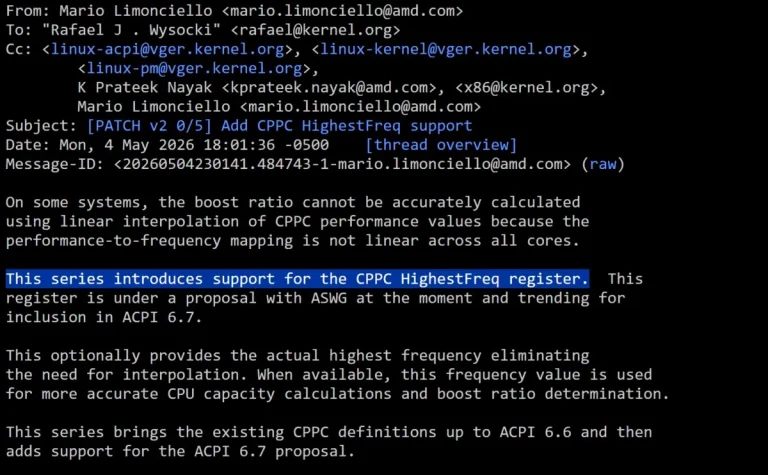
AMD is orchestrating a subtle yet consequential refinement for its Ryzen processors: a mechanism enabling Windows and...
Apple has recently promulgated a comprehensive suite of software updates across all supported hardware, primarily focusing on...
The TanStack suite, a cornerstone of modern web development boasting over 50 million monthly downloads, has fallen...
According to reports circulating on NEOWIN, Windows 11 users operating Dell hardware have recently encountered a surge...
Since the cessation of S Pen support in the Galaxy Z Fold7, persistent rumors have suggested that...
In an era characterized by intensifying smartphone rivalry and the inexorable surge of component costs, even Samsung—despite...
Vision Pro Stalled: Why Apple is Shifting its “Spatial” Future to AI Smart Glasses and Wearable Pins


Vision Pro Stalled: Why Apple is Shifting its “Spatial” Future to AI Smart Glasses and Wearable Pins
Notwithstanding persistent conjecture that Apple has surreptitiously abandoned its Vision Pro endeavor, recent insights from Bloomberg correspondent...
A robotic lawnmower weighing nearly a hundred kilograms sounds like a quintessential convenience for effortless yard maintenance—until...
The European Parliamentary Research Service has cautioned that VPN technology is increasingly being subverted to bypass online...
Cloudflare has resolved to excise approximately one-fifth of its workforce amidst a precipitous surge in the internal...
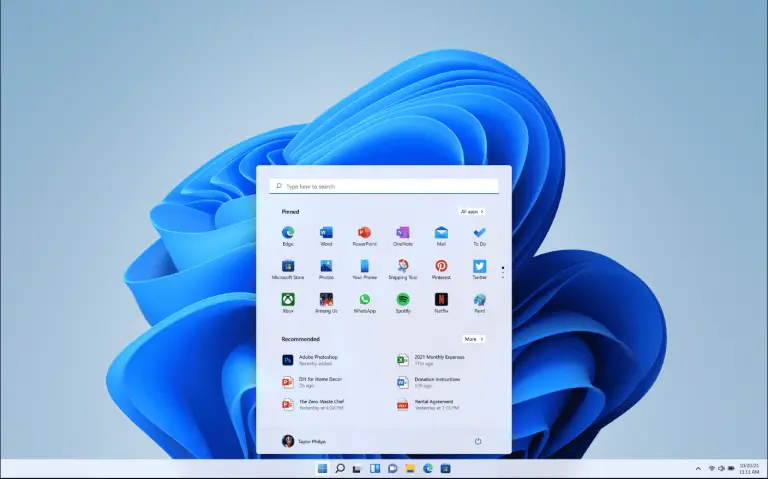
While Windows 11 may project the image of a cutting-edge operating system—replete with Artificial Intelligence, a revitalized...
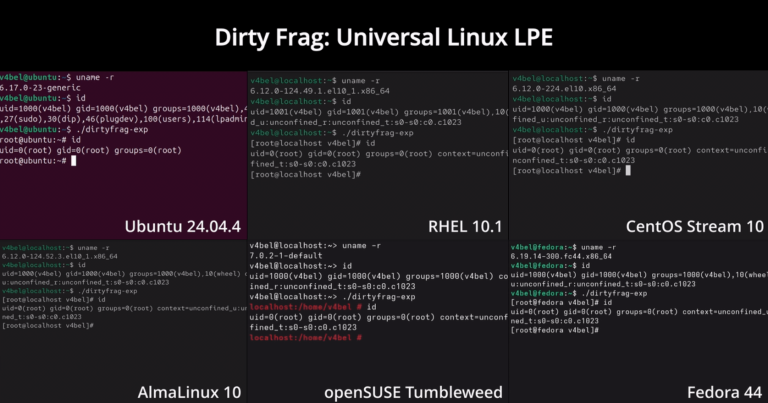
A formidable new vulnerability has been unearthed within the Linux ecosystem, facilitating the acquisition of administrative privileges...
Let’s Encrypt suspended the issuance of all TLS certificates for several hours due to a technical anomaly...
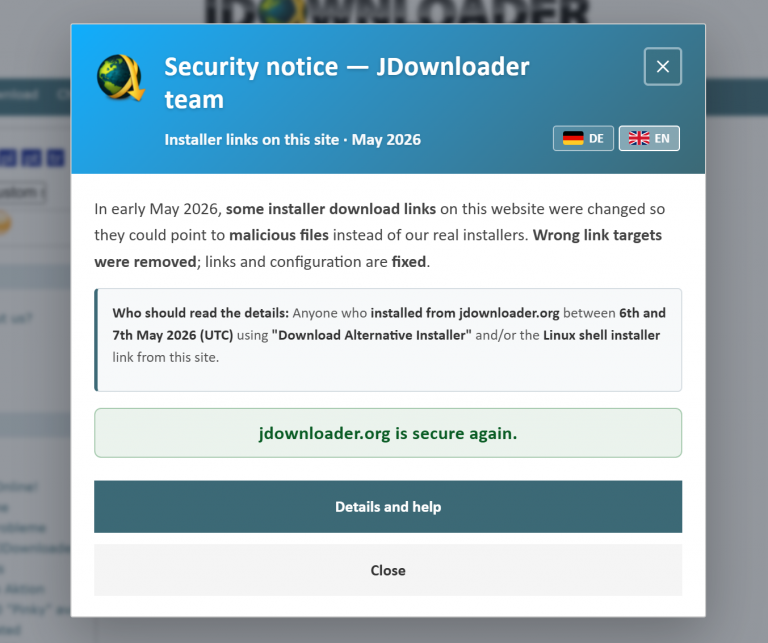
The official portal of the venerable free download utility JDownloader was compromised by adversaries between May 6...