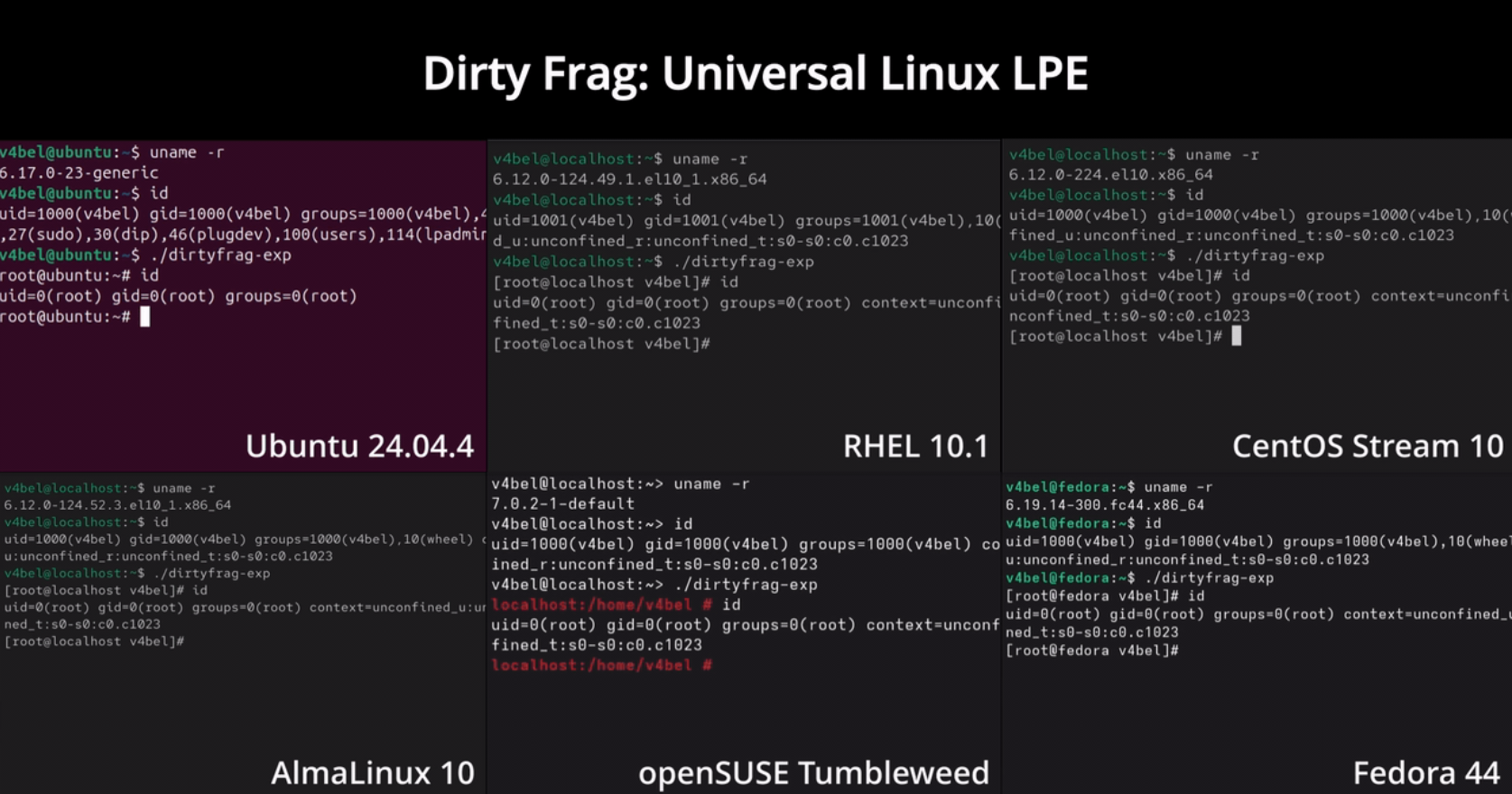
A formidable new vulnerability has been unearthed within the Linux ecosystem, facilitating the acquisition of administrative privileges via a singular command. Dubbed “Dirty Frag,” this flaw imperils a vast array of prominent distributions, including Ubuntu, Red Hat Enterprise Linux, Fedora, AlmaLinux, and openSUSE.
Security researcher Hyunwoo Kim discovered that the defect originated within the Linux kernel approximately nine years ago, sequestered within the algif_aead cryptographic algorithm interface. To execute an offensive, Dirty Frag amalgamates two distinct kernel errors associated with the memory page caching mechanism.
By leveraging these vulnerabilities, an adversary can manipulate protected system files directly within volatile memory and escalate privileges to the root level. According to Kim, Dirty Frag belongs to the same classification as the notorious Dirty Pipe and Copy Fail vulnerabilities, yet it targets a different element of the kernel’s data structure. Unlike many analogous exploits, its success does not hinge upon precise temporal synchronicity, nor does a failed attempt induce a kernel panic. Due to its predictable operational mechanics, the probability of a successful incursion remains exceptionally high.
The vulnerability can obtain root privileges on major Linux distributions by chaining the xfrm-ESP Page-Cache Write (CVE-2026-43284) vulnerability and the RxRPC Page-Cache Write (CVE-2026-43500) vulnerability. Kim disseminated a comprehensive technical analysis and functional exploit code prematurely after a third party independently published a working exploit on May 7, 2026, thereby collapsing the non-disclosure period.
xfrm-ESP Page-Cache Write (CVE-2026-43284)was patched in mainline f4c50a4034e6.RxRPC Page-Cache Write (CVE-2026-43500)was patched in mainline aa54b1d27fe0.
To implement temporary mitigation, the researcher suggests disabling the susceptible kernel modules: esp4, esp6, and rxrpc. This procedure effectively blocks the loading of these modules and purges them from memory; however, its application will render IPsec-based VPN connections and the AFS distributed file system inoperable.
This revelation emerges amidst a sustained wave of attacks exploiting another Linux vulnerability, Copy Fail. Last week, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) integrated Copy Fail into its Known Exploited Vulnerabilities (KEV) catalog, mandating that federal agencies fortify their systems by May 15. Furthermore, in April, Linux developers remediated the “Pack2TheRoot” vulnerability within the PackageKit service, a flaw that had lingered undetected for over a decade and similarly facilitated root-level access.
Support Our Threat Intelligence
If you find our technology report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee