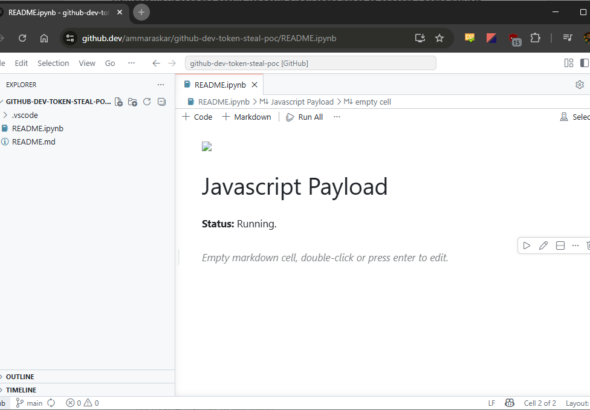
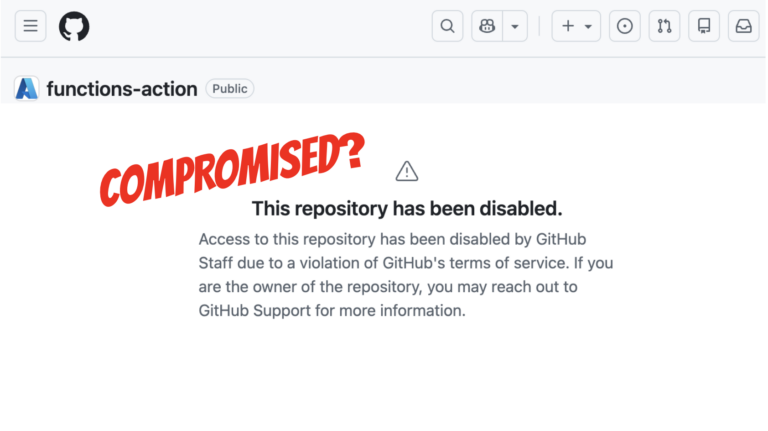
GitHub abruptly deactivated seventy-three institutional Microsoft repositories. This sudden intervention followed an aggressive resurgence of the self-propagating...
Retro Radiance: Microsoft Unveils 25th Anniversary Translucent Green Hardware at Xbox Games Showcase


Retro Radiance: Microsoft Unveils 25th Anniversary Translucent Green Hardware at Xbox Games Showcase
Following the spectacular Summer Game Fest 2026, Microsoft delivered a nostalgic tribute during its recent Xbox Games...
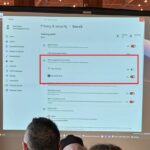
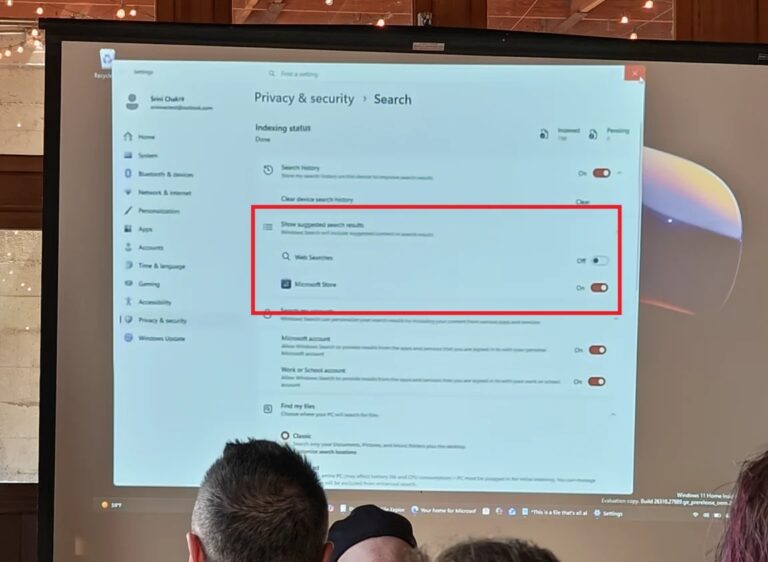
Microsoft’s promised quality improvements for Windows 11 remain underway. Notably, an enhancement highly anticipated by frequent searchers...
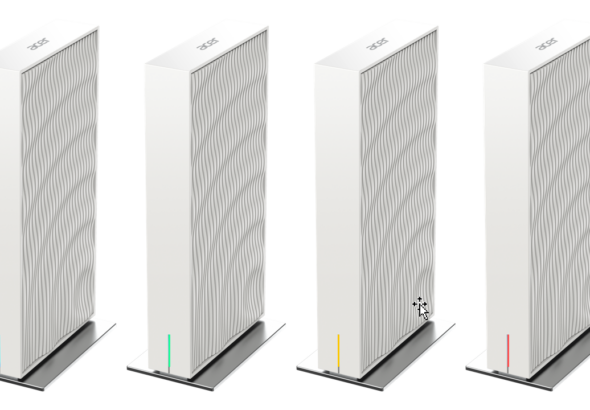
Proprietors of Acer Wave 7 routing hardware must diligently monitor forthcoming system updates. Recently, security researchers identified...
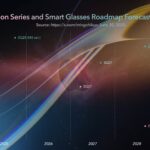
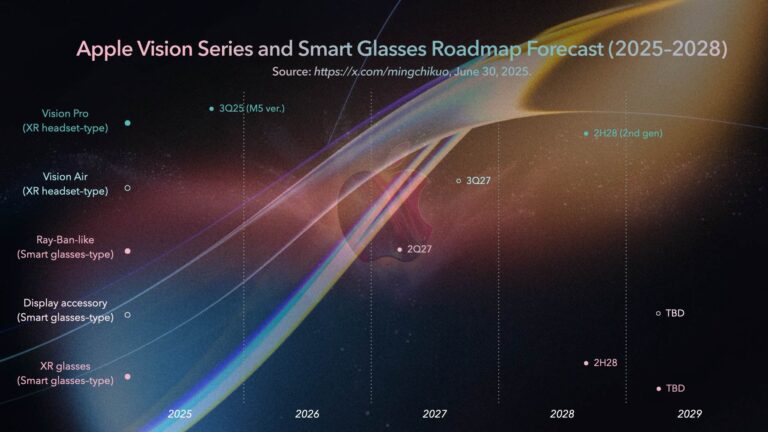
On the eve of the WWDC 2026 conference, a sudden tremor disrupted Apple’s spatial computing supply chain....
Apple’s annual Worldwide Developers Conference (WWDC 2026) will officially commence on June 8 at 10:00 AM Pacific...
Previously, we discussed an internal system anomaly that triggered an unprecedented global account lockout yesterday. Consequently, numerous...
Recently, an enigmatic system malfunction instigated a massive, worldwide purge of OpenAI accounts. Consequently, ChatGPT operators spanning...
Artificial intelligence increasingly serves as a potent instrument for malicious cyber coalitions. According to the Financial Times,...
Cloudflare has meticulously monitored the ratio between automated bot traffic and human internet activity since 2025. Initially,...
Corporate Perseverance Amid Delays Whispers recently emerged suggesting Intel might abandon its Arc discrete graphics division. This...
The Demise of Intel Hardware Support During the WWDC 2025 conference, Apple finalized the operational lifecycle for...
AI data centers require powerful network chips. These chips smoothly link custom hardware, graphics processors, and core...
The co-founder of Notion recently disclosed a significant milestone regarding the platform’s digital infrastructure. For years, the...
A Monumental Financial Milestone Apple preemptively released a comprehensive economic evaluation of its App Store ecosystem. This...