The prominent Python asynchronous framework Starlette, which serves as the foundational cornerstone for FastAPI, has been compromised...
The formal deployment of OpenBSD 7.9 materializes closely on the heels of an unprecedented cryptographic anomaly. Specifically,...
The enduring legal friction between Google and the European Commission over the Digital Markets Act (DMA) continues...
The AlmaLinux OS Foundation recently unveiled version 10.2 of its free, open-source enterprise operating system. This downstream...
Europe currently confronts the aggressive ascendancy of Chinese innovation alongside the historic hegemony of American technology giants....
In 2025, NVIDIA introduced the unified NVIDIA App as a comprehensive companion application. This modern software encapsulates...
The popular Laravel-Lang package ecosystem has suffered a massive supply-chain intrusion. Interestingly, the adversary eschewed traditional codebase...
Per reports from Reuters, recent military engagements have exposed a glaring vulnerability. Specifically, conflicts involving Iraq and...
Recently, cybersecurity practitioners exposed several high-risk vulnerabilities within the NGINX web server framework. Threat actors can trigger...
Recently, numerous Motorola smartphone users witnessed a subtle anomaly. Opening the Amazon application briefly triggers the web...
Anonymous cryptocurrency exchanges operating within the Tor network and eschewing identity verification protocols have long been conceptualized...
Google’s inaugural screenless wellness wearable, the Fitbit Air, debuted earlier this month with a definitive commercial release...
While developers and gamers are still adjusting to the breathtaking lighting and geometric fidelity of Unreal Engine...
Elon Musk, in a recent public response to user inquiries, definitively articulated his intent to open-source xAI’s...
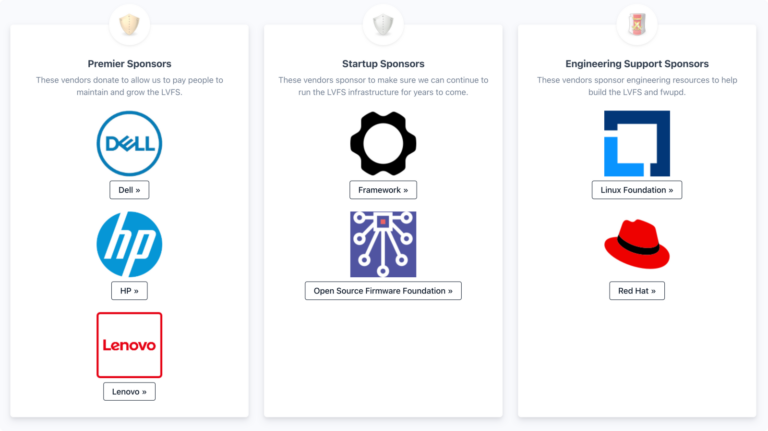
The Linux Vendor Firmware Service (LVFS) functions principally as a secure administrative portal engineered for original equipment...