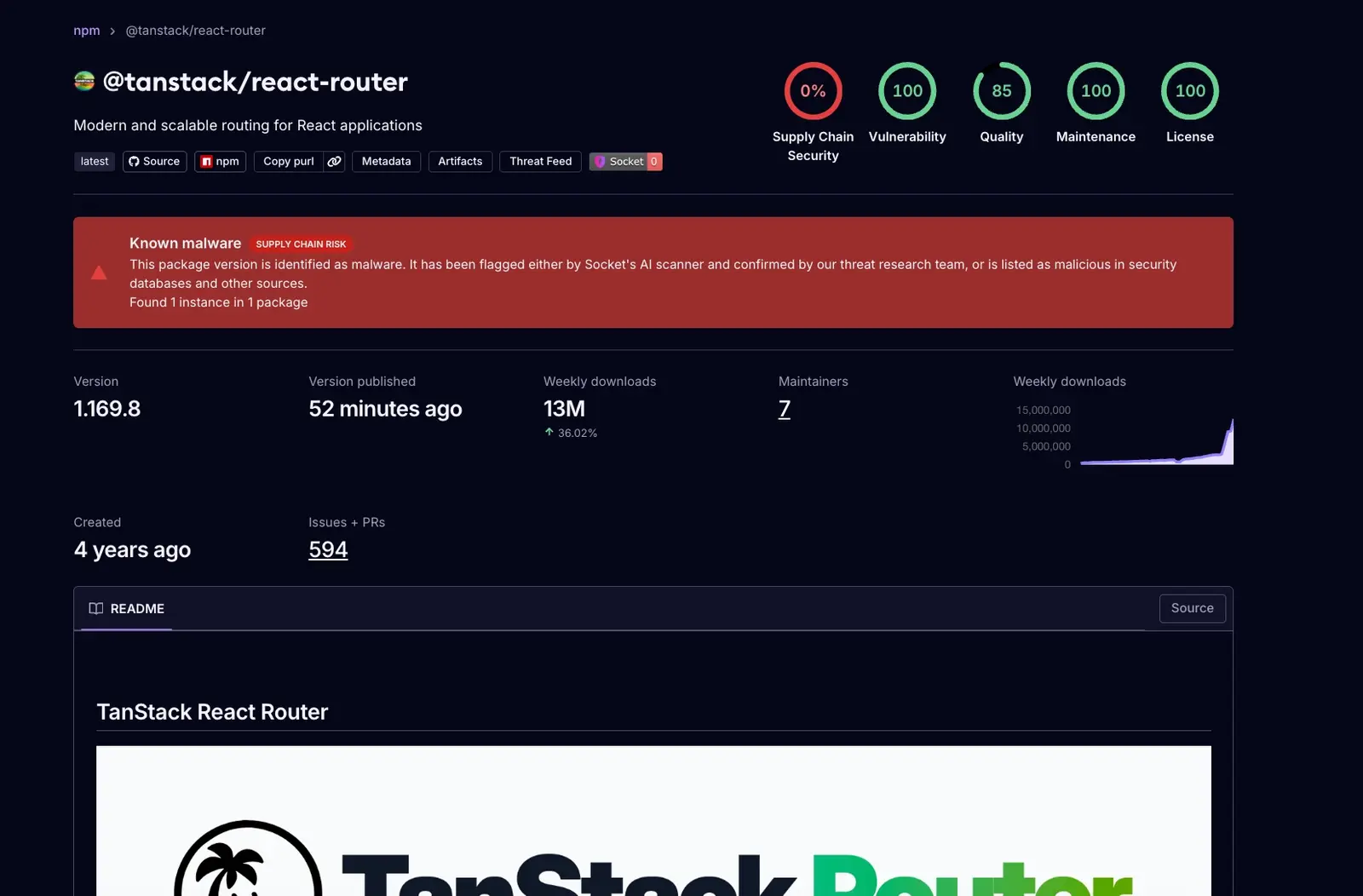
The TanStack suite, a cornerstone of modern web development boasting over 50 million monthly downloads, has fallen victim to a sophisticated software supply chain attack. Approximately 84 NPM packages under the TanStack umbrella were subverted and replaced with malicious iterations by adversaries. This anomaly was swiftly detected by the cybersecurity firm Socket, prompting an immediate alert; subsequently, the TanStack team corroborated the breach and initiated the purge of the compromised versions.
The magnitude of this incursion is illustrated by the @tanstack/react-router package, which alone commands 12 million weekly downloads. Given that these utilities are woven deeply into the NPM ecosystem through both direct and transitive dependencies, this assault possesses the potential for widespread systemic disruption.
Forensic analysis reveals that the malicious distributions introduced a clandestine package.json and a tanstack_runner.js script. These files are engineered to execute automatically during the installation of Git-based dependencies, thereby facilitating the execution of arbitrary code. Such capabilities allow attackers to exfiltrate sensitive credentials and other privileged information.
The TanStack team attributed the compromise to a series of GitHub Actions exploits. Notably, NPM credentials remained secure, and the publication workflow itself was not breached; instead, the malicious releases were orchestrated during the testing and cleanup phases of the workflow. By executing attacker-controlled code, the adversaries leveraged the project’s OIDC (OpenID Connect) trusted publisher status to authenticate and broadcast the compromised packages directly to the NPM registry.
In an urgent remedial effort, the TanStack team has deprecated the affected versions and is collaborating with the NPM security team for comprehensive resolution. Current GitHub Actions cache entries have been expunged, and the team is implementing structural fortifications—including the reconstruction of impacted workflows, the enforcement of repository owner protections, and the mandatory pinning of third-party action references to specific commit hashes. Socket has published an exhaustive list of the compromised packages, and developers who utilized these tools for builds over the previous twenty-four hours are urged to perform an immediate security audit.
Support Our Threat Intelligence
If you find our technology report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee