The U.S. Department of Justice has announced the takedown of a phishing website used by fraudsters in...
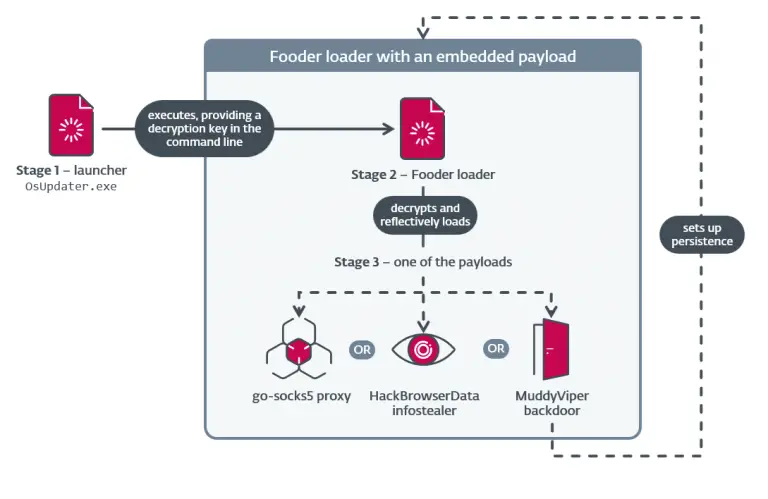
The Iranian threat group MuddyWater has significantly expanded its toolkit and refined its tactics, conducting a series...
The Japanese online retailer Askul has managed to restore only partial online sales after forty-five days of...
The nonprofit Let’s Encrypt has announced a phased reduction of TLS certificate lifetimes — from the current...
GIFs are everywhere—from memes to explainer visuals and marketing content. But as creative as they are, GIFs...
According to a report by Bloomberg journalist Mark Gurman, Apple is expected to reduce the footprint of...
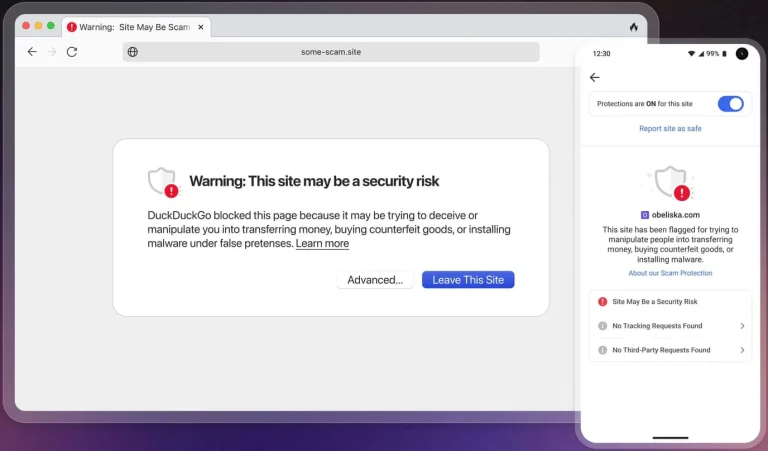
The DuckDuckGo browser has recently enhanced its Scam Blocker tool, which is designed to intercept access to...
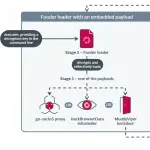
Hackers have begun actively distributing a new iteration of the Amatera Stealer—a reimagined and fortified clone of...
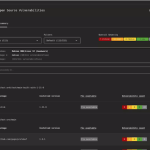
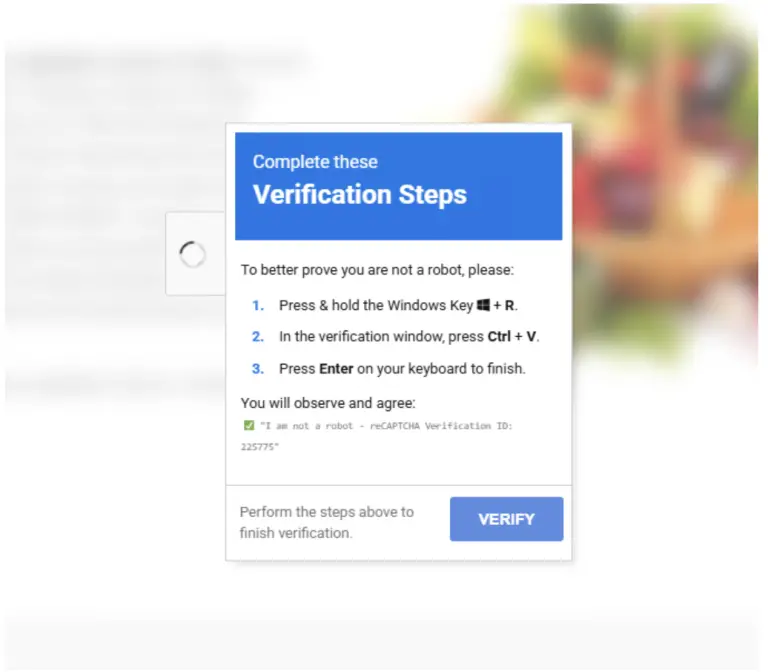
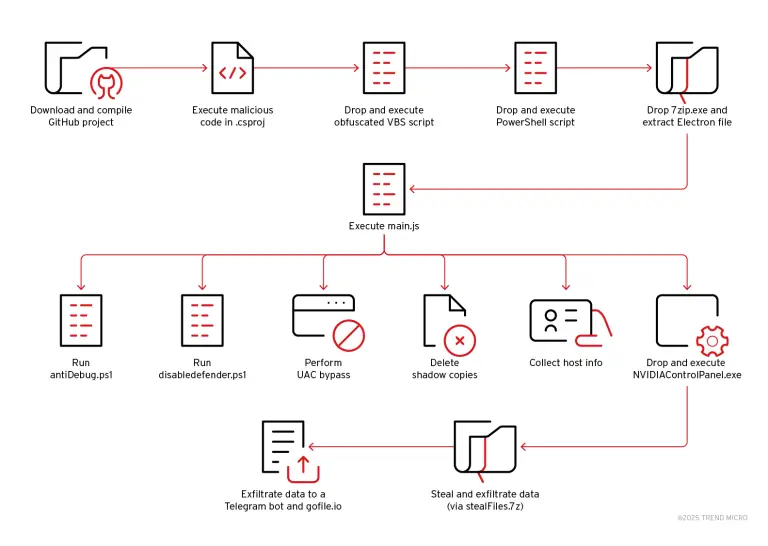
A new actor has emerged within cyberspace—Water Curse, a threat group that since March 2023 has been...
On the night of June 18, 2025, the Iranian cryptocurrency exchange Nobitex fell victim to a devastating...
Researchers from Israel and India have unveiled a groundbreaking technology designed to counter fraudulent voice calls—commonly known...
A former analyst with the United States Central Intelligence Agency (CIA) has been sentenced to prison for...
Between April and early June 2025, experts from Google’s Threat Intelligence Group (GTIG), in collaboration with external...