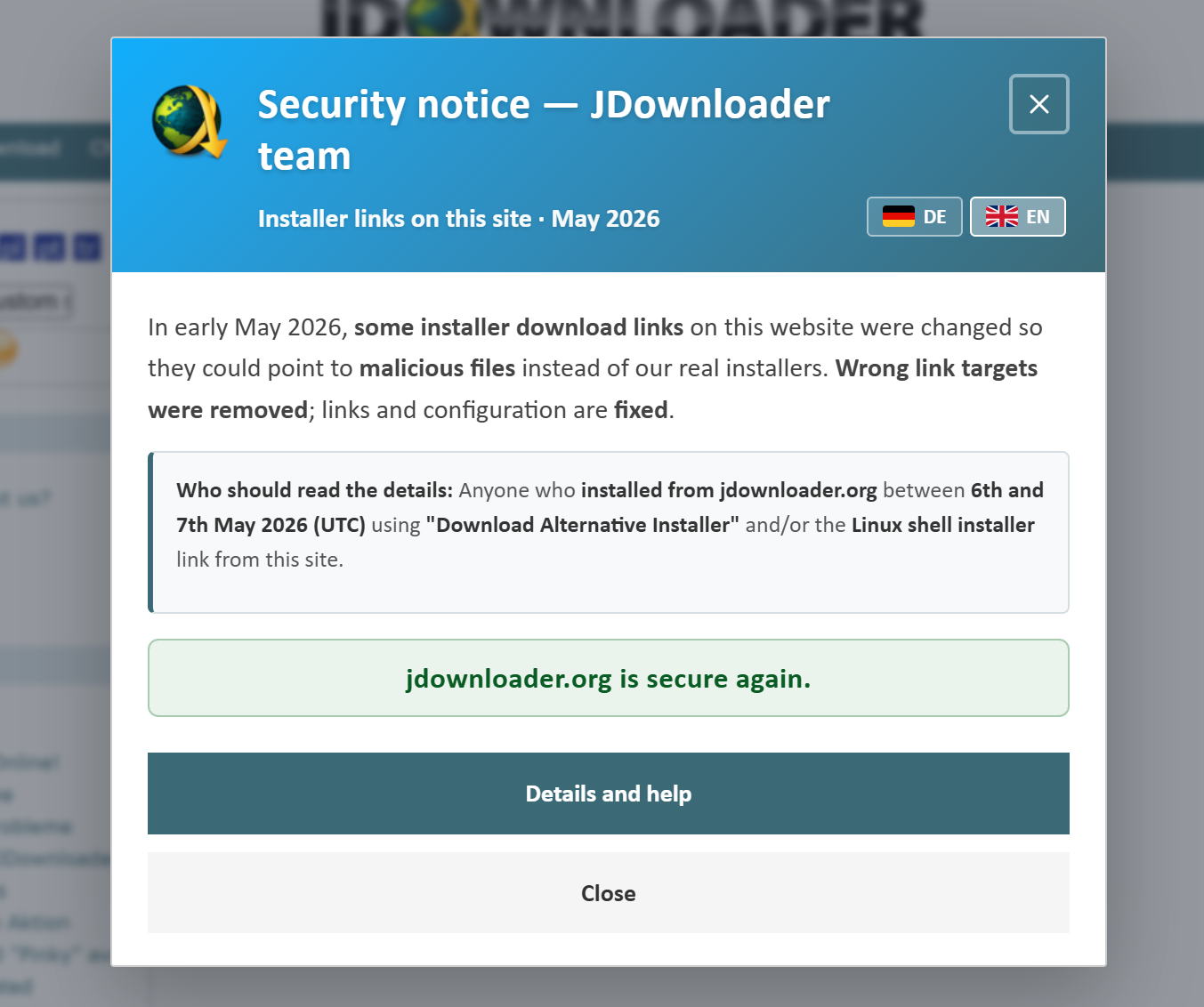
The official portal of the venerable free download utility JDownloader was compromised by adversaries between May 6 and May 7, 2026 (UTC). During this breach, the assailants subverted the platform’s download links, replacing them with malicious iterations embedded with a Remote Access Trojan (RAT); consequently, individuals who acquired the software within this timeframe are urged to perform an exhaustive scan using anti-virus solutions immediately.
JDownloader, which facilitates automated file retrieval from hosting servers, video platforms, and premium link generators, commands a global user base of millions across Windows, Linux, and macOS. This particular intrusion successfully tampered with the installers for both the Windows and Linux distributions.
Fortuitously, Microsoft Defender demonstrated efficacy in detecting and identifying the Trojan deployed by the hackers. During the period of compromise, Microsoft’s defensive suite automatically intercepted the software for several users, flagging the installers as malicious and obstructing their execution, although users retained the option to manually bypass these warnings.
The compromised versions were digitally signed using an array of stolen code-signing certificates—variously identifying the developer as Zipline LLC or The Water Team—in a calculated attempt to diminish user suspicion. However, the authentic digital signature for JDownloader should exclusively be attributed to AppWork GmbH.
Upon receiving user grievances, the JDownloader team initiated an investigation which revealed that the hackers had infiltrated the website’s content management system to alter the download links. The affected files included the Windows “alternative installer” and the Linux shell installation script.
The Trojan deployed by the adversaries was developed in Python, featuring a modular bot and RAT framework capable of receiving mandates from an attacker’s Command and Control (C2) server. By design, this malware empowers the hackers to execute arbitrary commands on infected devices, which likely encompasses keystroke monitoring and the exfiltration of sensitive user files.
Merely uninstalling the backdoored version of JDownloader may prove insufficient to resolve the infection. It is recommended that users who downloaded the software via the official site between May 6 and May 7, 2026 (UTC), back up their essential data and perform a complete system reinstallation before downloading a pristine, untainted version of the utility.
The adversaries utilized the following compromised, yet ostensibly legitimate, domains for their C2 operations:
parkspringshotel[.]com/m/Lu6aeloo.phpauraguest[.]lk/m/douV2quu.phpcheckinnhotels[.]com
Support Our Threat Intelligence
If you find our technology report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee