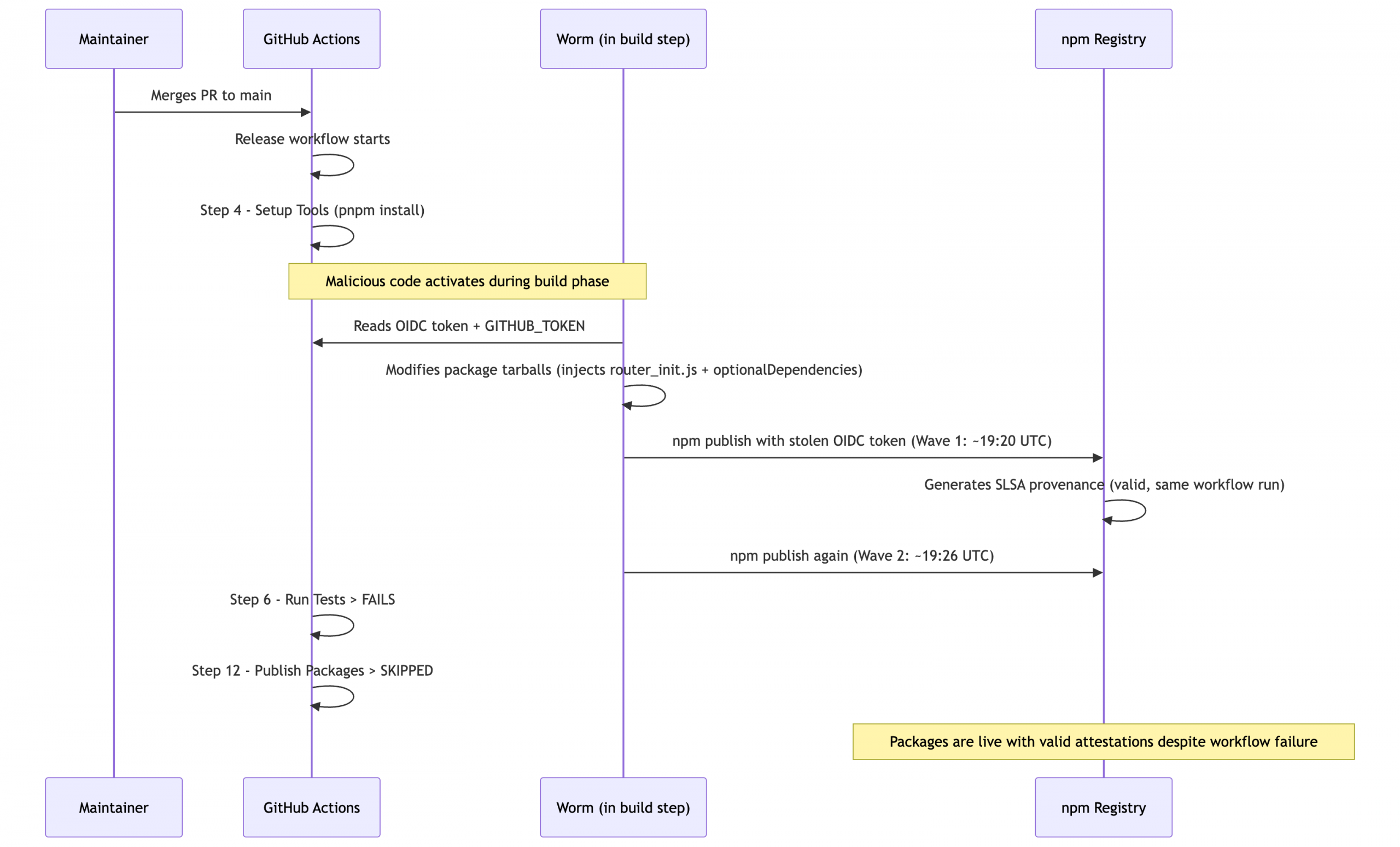
This week, the TanStack ecosystem—a cornerstone of modern web development—suffered a sophisticated security breach. Exploiting a procedural vulnerability, adversaries disseminated eighty-seven deleterious packages directly into the NPM registry. Although this supply chain offensive was detected with commendable celerity, resulting in the revocation of the compromised installers within two hours, a significant number of development environments were undoubtedly infected.
The malicious payloads were primarily engineered to exfiltrate sensitive credentials, including GitHub, AWS, and various environment tokens. However, as forensic analysis deepened, developers uncovered an exceptionally malevolent contingency: a “dead man’s switch.” If the malware detects that a stolen credential has been revoked, it attempts to execute a catastrophic rm -rf ~/ command to expunge all user files.
The attack vector facilitates the persistence of a clandestine script, gh-token-monitor.sh, nestled within the ~/.local/bin/ directory. Operating as a systemd user service or a LaunchAgent under the moniker com.user.gh-token-monitor, the script polls the GitHub API every sixty seconds to verify the continued validity of the stolen tokens. Should the API return a 4xx HTTP error code indicating revocation, the script triggers the high-risk command, potentially annihilating the entire development environment and destabilizing the underlying operating system.
Preliminary investigations suggest this script may possess advanced persistence mechanisms, allowing it to “resurrect” after manual deletion to continue its sentinel duties. This represents a pioneering and particularly sinister evolution in NPM supply chain attacks. If a developer, upon learning of a potential infection, precipitously revokes their GitHub tokens, they risk activating the switch and suffering total data loss.
Consequently, it is imperative that developers meticulously back up all critical data and intellectual property prior to neutralizing compromised credentials. Given that adversaries may leverage stolen tokens to infect cloud-based assets or move laterally within other infrastructures, merely revoking access is insufficient; a comprehensive audit of all environmental access logs is mandatory to ensure systemic integrity.
Support Our Threat Intelligence
If you find our technology report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee