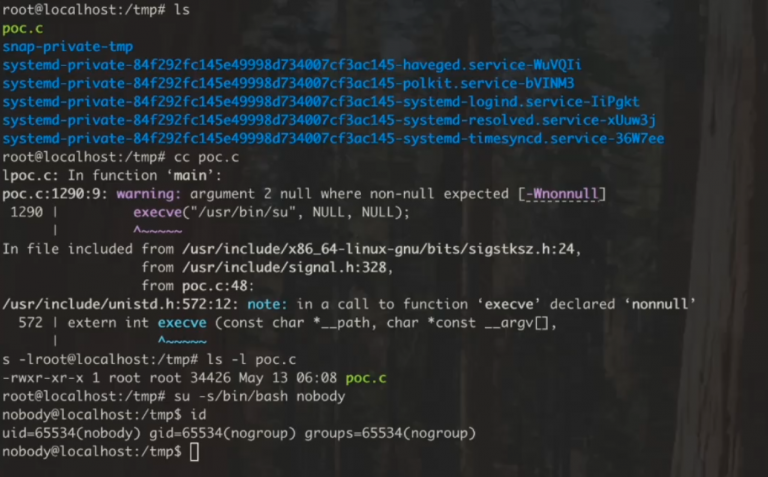
A formidable vulnerability christened Fragnasia has been identified within the Linux ecosystem, permitting a standard user to...
Cybersecurity 2026
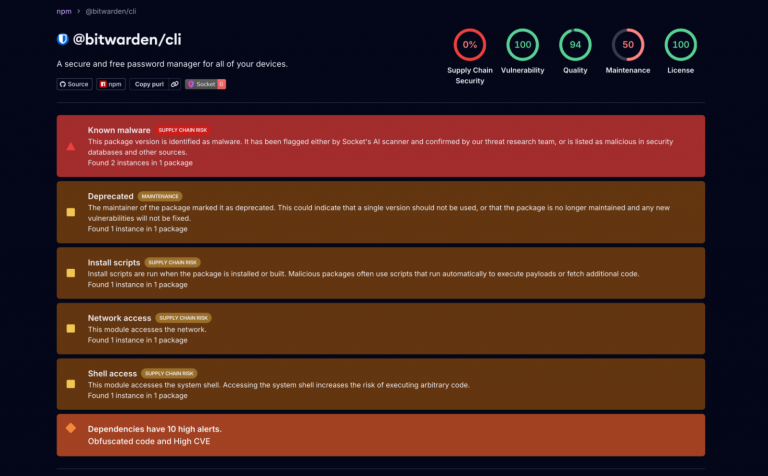
Yesterday, the TeamPCP collective—a threat actor specializing in supply chain incursions—released the source code for Shai-Hulud, an...
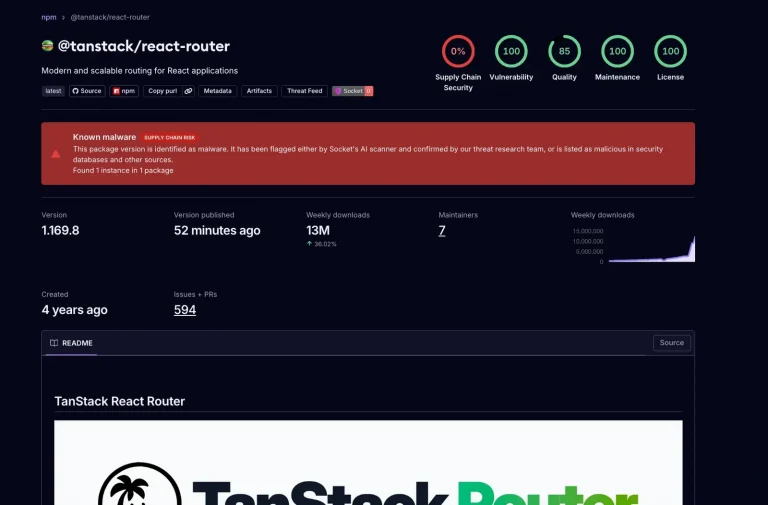
The TanStack suite, a cornerstone of modern web development boasting over 50 million monthly downloads, has fallen...
A robotic lawnmower weighing nearly a hundred kilograms sounds like a quintessential convenience for effortless yard maintenance—until...
Let’s Encrypt suspended the issuance of all TLS certificates for several hours due to a technical anomaly...
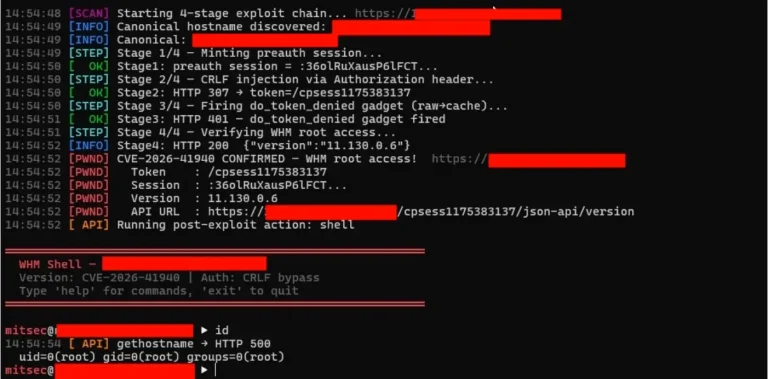
A critical vulnerability within cPanel, of which server proprietors were apprised only in late April, has proven...
A critical vulnerability within the Linux kernel, christened CopyFail, has begun to precipitate significant disruptions for server...
Palo Alto Networks has issued a critical warning regarding a formidable vulnerability within the PAN-OS operating system...
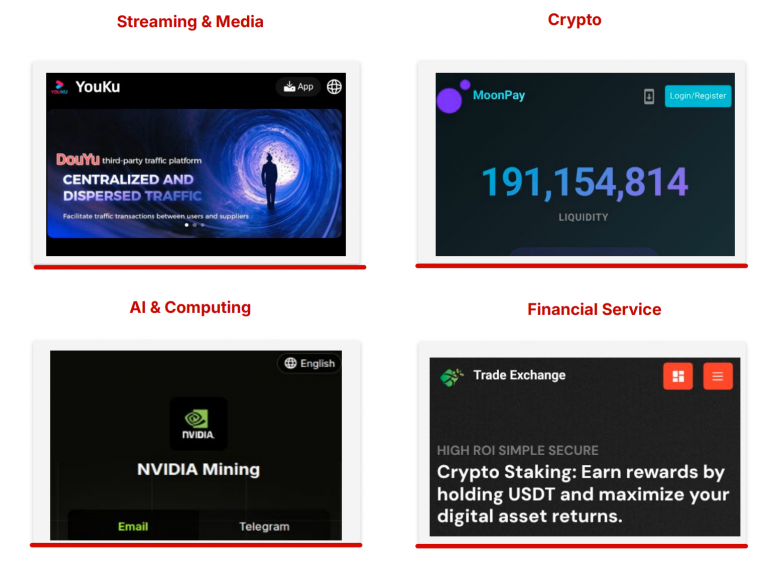
Criminal syndicates are increasingly leveraging the inherent trust associated with ubiquitous platforms as a fundamental component of...
A hacker, indicted for orchestrating assaults on oil and gas infrastructure across several nations, has formally entered...
Beacons of Risk: How Axon’s “Untrackable” Police Gear is Broadcasting Officer Locations to Criminals


Beacons of Risk: How Axon’s “Untrackable” Police Gear is Broadcasting Officer Locations to Criminals
A law enforcement officer has not yet crossed the threshold of the precinct, yet an alien mobile...
Victims of The Gentlemen ransomware have been granted a fortuitous opportunity to reclaim their data without succumbing...
Recently, reports surfaced regarding a sophisticated subversion of Infrastructure as Code (IaC) security scanning utilities, specifically Checkmarx...