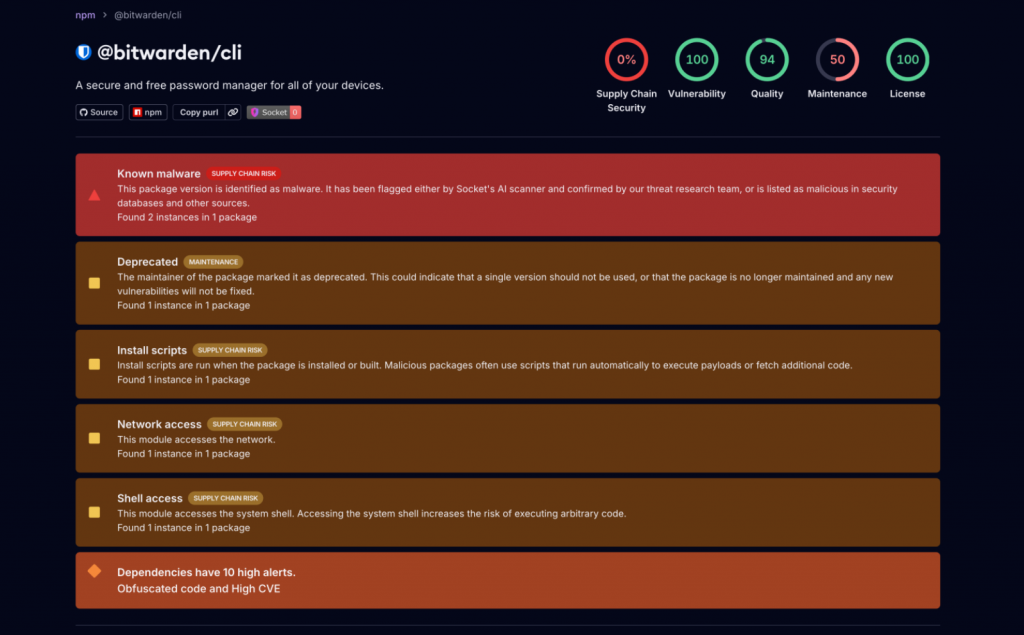
Recently, reports surfaced regarding a sophisticated subversion of Infrastructure as Code (IaC) security scanning utilities, specifically Checkmarx and KICS. Adversaries successfully surreptitiously integrated malicious code into various extensions and container images to exfiltrate sensitive telemetry from development environments. It has now been confirmed that the command-line interface (CLI) of the renowned password manager Bitwarden has been ensnared in this “poisoning” campaign to facilitate the theft of further sensitive data.
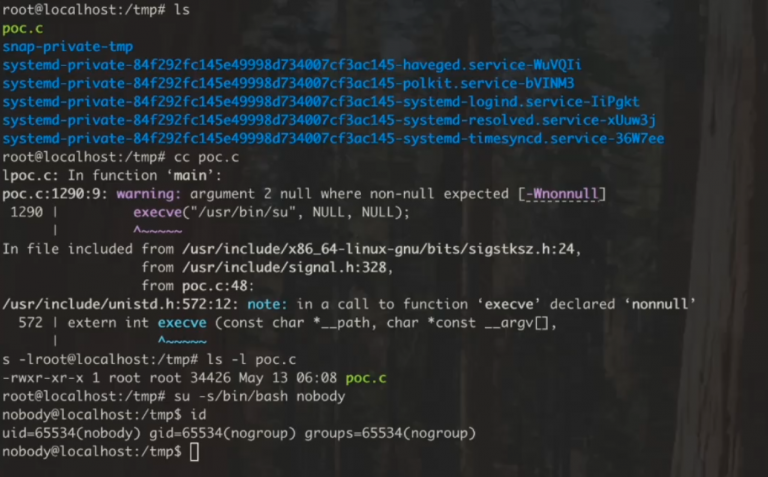
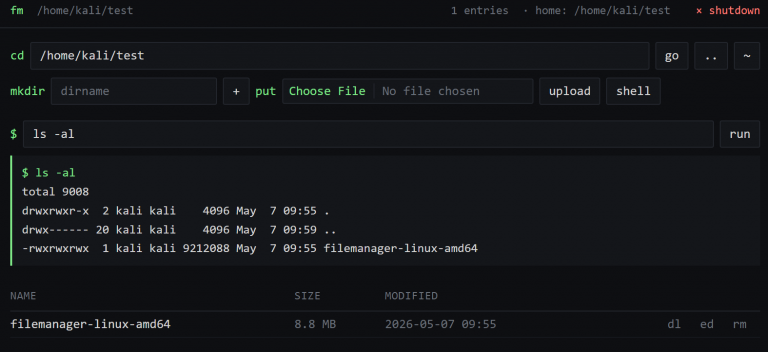
Security researchers identified that Bitwarden/cli v2026.4.0 harbors malicious payloads. This incursion appears to have exploited compromised GitHub Actions within Bitwarden’s CI/CD pipeline, mirroring the tactical patterns observed in the KICS security breaches.
While a comprehensive technical forensic analysis is currently underway—with detailed findings regarding affected versions, indicators of compromise (IoCs), and remediation protocols expected shortly—it is imperative to adhere to the principle of proactive security. Users of the Bitwarden CLI are urged to immediately scrutinize their CI logs and rotate any credentials that may have been exposed within infected workflows.
It is critical to specify that current evidence suggests the compromise is localized to the Bitwarden CLI NPM package; other distributions, including the desktop client, browser extensions, MCP servers, and other legitimate releases, remain unaffected.
Notably, the malicious code exhibits a distinct lack of obfuscation regarding its geopolitical affiliations. The payload performs a systemic check of the target device’s locale; should it detect a Russian (RU) setting, it immediately executes a silent termination. Consequently, the malware abstains from initiating assaults within Russian-speaking environments.
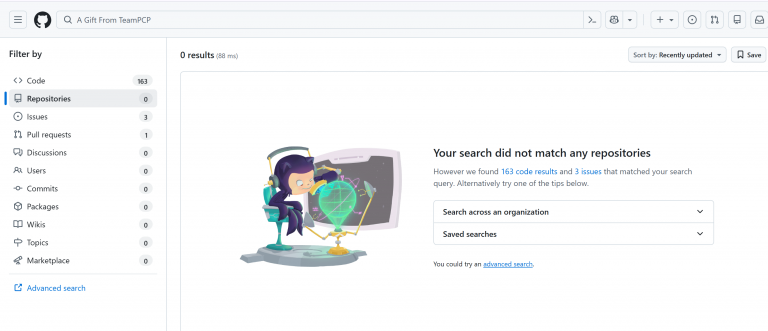
The threat collective TeamPCP was previously characterized as a non-state-aligned entity, potentially comprised of a decentralized cohort of adolescent hackers, with early intelligence tracing their origin to Kenya. Prior to this incident, no definitive evidence linked them to Russian interests. However, the selective exclusion of Russian targets strongly suggests an alliance or a significant convergence of interests between TeamPCP and Russian cyber-operatives. It is highly improbable that a financially motivated syndicate would voluntarily bypass Russian enterprises without such an underlying affiliation.