A formidable vulnerability christened Fragnasia has been identified within the Linux ecosystem, permitting a standard user to attain comprehensive administrative dominion over the system. This defect, designated CVE-2026-46300, afflicts the Linux kernel, prompting distribution maintainers to expedite the release of critical security patches.
The vulnerability stems from a structural flaw within the XFRM ESP-in-TCP subsystem. This malfunction enables an unprivileged local actor to write arbitrary data into the kernel’s memory cache for files that are ostensibly read-only. Such a mechanism paves a direct path for the execution of malicious code with root authority.
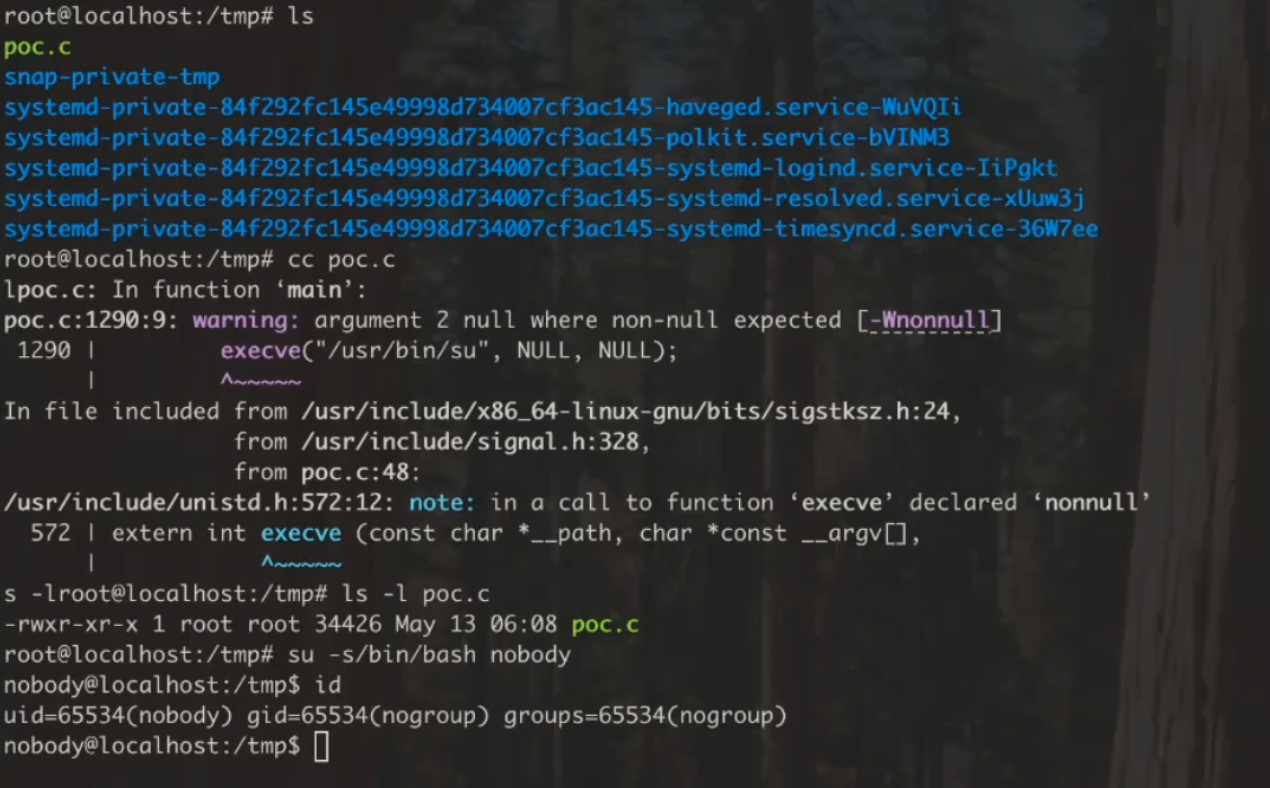
William Bowling, Head of Security at Zellic, unearthed the flaw and subsequently published a proof-of-concept demonstrating how the contents of the /usr/bin/su system file can be manipulated in memory to summon an administrative shell. Bowling characterizes Fragnasia as a member of the “Dirty Frag” class of vulnerabilities, which gained notoriety merely last week. This nascent threat impacts all iterations of the Linux kernel released prior to May 13, 2026, and a functional public exploit for the broader Dirty Frag class is already in circulation.
The Dirty Frag exploit leverages a dual-flaw synergy—CVE-2026-43284 and CVE-2026-43500—to modify protected system files within memory and escalate privileges. While Fragnasia operates on a similar principle, it utilizes a distinct error in the ESP/XFRM architecture and does not necessitate a race condition, thereby streamlining the exploitation process.
Linux users are strongly urged to apply kernel updates with the utmost celerity. If immediate patching is unfeasible, developers suggest the temporary deactivation of the susceptible kernel modules via the following commands:
rmmod esp4 esp6 rxrpc
printf ‘install esp4 /bin/false\ninstall esp6 /bin/false\ninstall rxrpc /bin/false\n’ > /etc/modprobe.d/dirtyfrag.conf
While this mitigation effectively stymies the exploit, it concurrently disables IPsec VPN connections and the AFS distributed file system.
The revelation of Fragnasia coincides with the active exploitation of another Linux vulnerability known as Copy Fail. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has incorporated this issue into its catalog of known exploited vulnerabilities, mandating that federal agencies remediate the breach by May 15. The agency warned that such flaws are routinely weaponized by state-sponsored actors to infiltrate governmental infrastructures.
Support Our Threat Intelligence
If you find our technology report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee