Microsoft BitLocker, the proprietary encryption suite engineered to safeguard disk-bound data, has been compromised by a critical security flaw recently disclosed by independent researchers. This vulnerability permits an adversary with physical access to a device to effortlessly unlock encrypted volumes and obtain unrestricted read permissions using nothing more than a conventional USB drive.
The perceived rudimentary nature of this oversight has incited speculative discourse among observers, with some facetiously suggesting the presence of an intentional “backdoor.” While such conjectures remain largely apocryphal, the evident breakdown in communication between Microsoft and the research community is a matter of profound concern, as it directly precipitated the public release of the exploit.
Prerequisites for Analytical Research
- Storage Media: A USB flash drive formatted to NTFS, FAT32, or exFAT.
- Required Assets: The
FsTxdirectory, obtainable via the YellowKey repository. - Deployment: The
FsTxfolder must be situated within the hiddenSystem Volume Informationdirectory at the root of the USB drive. - Stealth Alternative: For a more surreptitious approach, the folder may be integrated into the target device’s EFI partition, obviating the need for external media—though this requires prior access to the machine.
- Target Environments: Windows 11, Windows Server 2022, and Windows Server 2025 (Windows 10 remains unaffected).
Operational Methodology
- Affix the prepared USB drive to a target system protected by BitLocker.
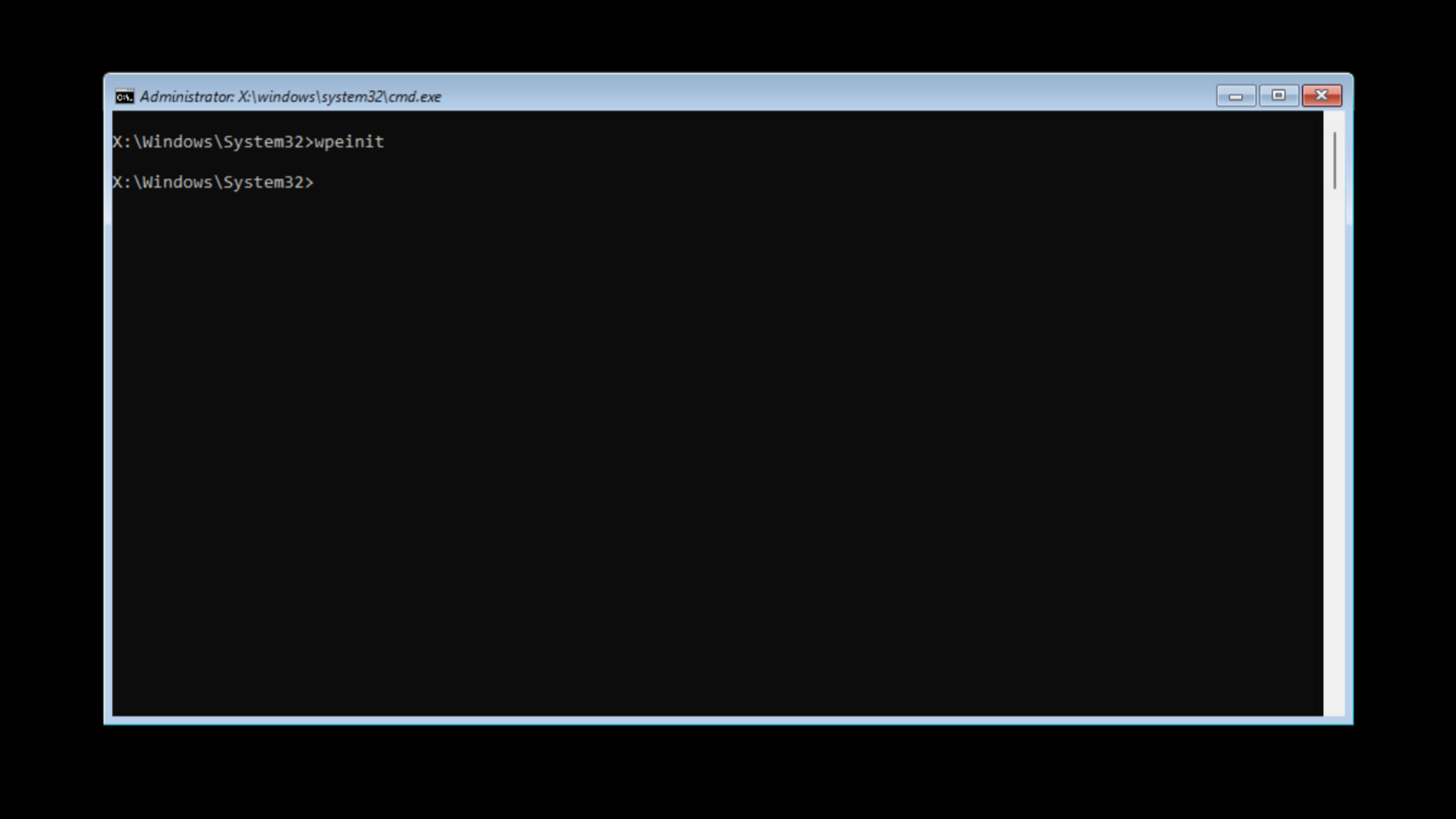
- Initiate a transition into the Windows Recovery Environment (WinRE) by holding the
Shiftkey while selecting “Restart.” - Immediately upon the system’s reboot, release
Shiftand maintain a continuous depression of theCtrlkey. - If executed successfully, the system will summon an unconstrained shell interface, granting comprehensive access to BitLocker-protected volumes and all constituent files.
The vulnerability was unearthed by the researcher Chaotic Eclipse, who intimated that prior attempts to report the flaw to Microsoft were met with either neglect or bureaucratic inertia. Consequently, the researcher opted for full public disclosure to compel an expedited remediation.
Chaotic Eclipse posits that the flaw’s existence is nearly inexplicable, noting that the compromised component is only exploitable within the WinRE recovery image; in a standard system installation, the identical component does not permit such a bypass. Compounding the urgency, security firms have already observed active exploitation of this flaw in the wild. As of this moment, Microsoft has yet to issue a formal communique or a definitive timeline for a corrective patch.
Support Our Threat Intelligence
If you find our technology report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee