Analysts from QiAnXin XLab have illuminated the clandestine operations of the Mr_Rot13 collective, an adversarial group that maintained obscurity for years and is currently weaponizing a critical vulnerability in cPanel & WHM to seize control of servers. This narrative portrays not a singular strike for transient gain, but the meticulous work of an enduring team that has architected its own infrastructure and sophisticated conduits for data exfiltration.
The exploit in question is CVE-2026-41940, an authentication bypass vulnerability boasting a staggering CVSS score of 9.8. Following its public disclosure on April 28, 2026, myriad criminal syndicates began its aggressive exploitation. XLab has detected over 2,000 unique IP addresses worldwide participating in these assaults—predominantly originating from Germany, the United States, Brazil, and the Netherlands. This breach permits adversaries to obtain administrative dominion over control panels without the necessity of credentials.
On May 4, specialists intercepted a malicious loader authored in Go, disseminated via the aforementioned vulnerability. This program systematically altered root passwords, embedded unauthorized SSH keys, and injected both a PHP backdoor and JavaScript instrumentation into the cPanel login interface. These scripts were designed to intercept usernames, passwords, User-Agent strings, and active URLs, subsequently transmitting the purloined telemetry to an external command server. A supplementary exfiltration channel was established through a Telegram group associated with the log_FatherBot.
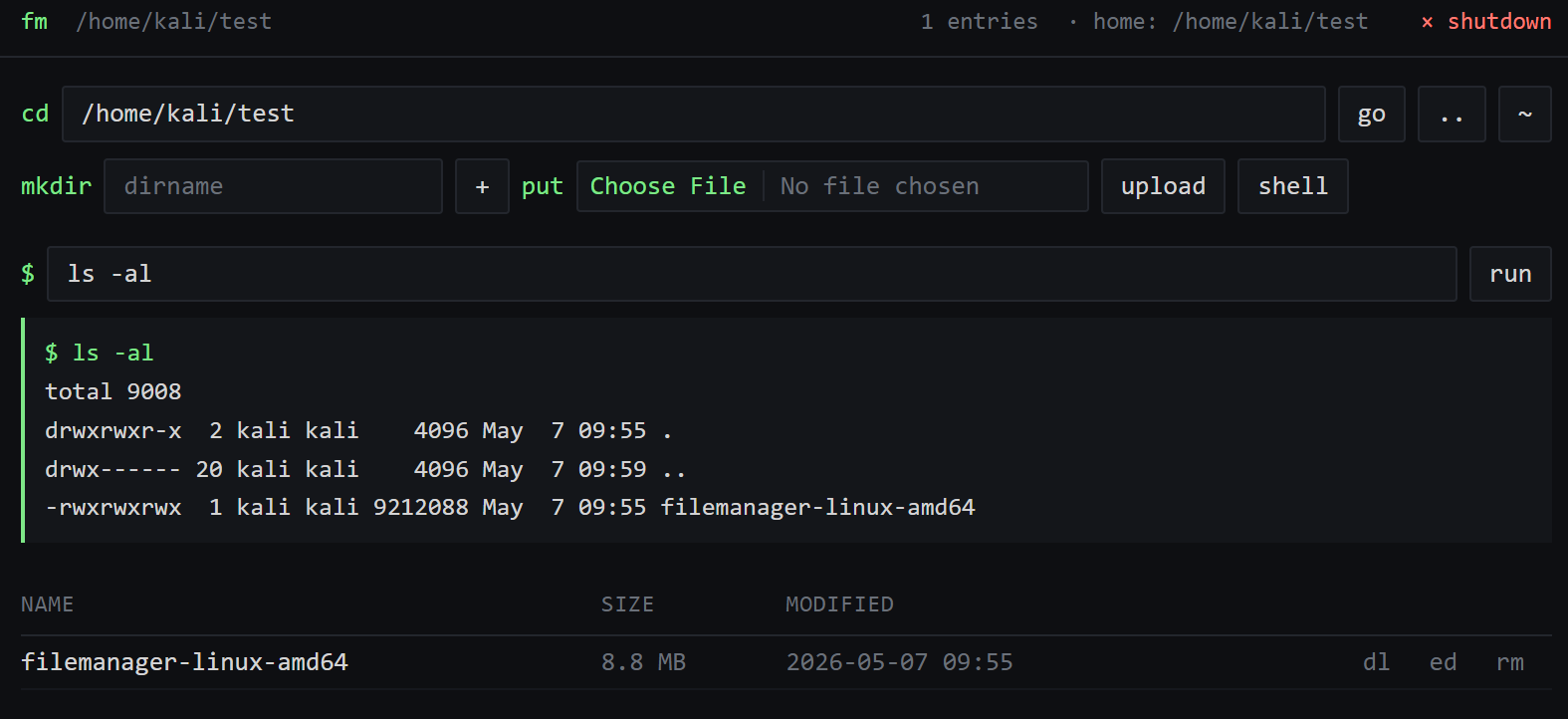
Following the initial compromise, a cross-platform remote access trojan (RAT) dubbed Filemanager—compatible with Linux, Windows, and macOS—was deployed. Through a web-based interface, operators could traverse file systems, execute arbitrary commands, and effectively govern the hijacked environment. Such maneuvers mirror previous campaigns where backdoors were institutionalized to ensure protracted dominion over victim infrastructure.
During the forensic reconstruction of the group’s infrastructure, XLab identified a nexus between the current campaign and the domain wrned.com, which appeared in a PHP backdoor uploaded to VirusTotal as early as 2022. Investigators posit that Mr_Rot13’s activities likely trace back to 2020, yet their samples and domains remained largely undetected by conventional security products for a significant duration.
The collective was christened Mr_Rot13 due to their utilization of the ROT13 cipher to obscure command-and-control addresses and the moniker 0xWR found within their Telegram data. While the identities of the participants remain unverified, the swift rotation of bot tokens following suspicious activity suggests a vigilant and disciplined operational posture. This incident underscores the enduring reality that authentication bypass vulnerabilities remain among the most exploited and perilous threat vectors in the digital landscape.
Support Our Threat Intelligence
If you find our technology report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee