Criminal syndicates are increasingly leveraging the inherent trust associated with ubiquitous platforms as a fundamental component of their fraudulent stratagems. A recent disclosure by CTM360 elucidates how Telegram Mini Apps have metamorphosed into a convenient storefront for adversaries: victims invoke a mini-application via a bot, encounter a familiar brand, and remain entirely oblivious to their migration into a malicious infrastructure.
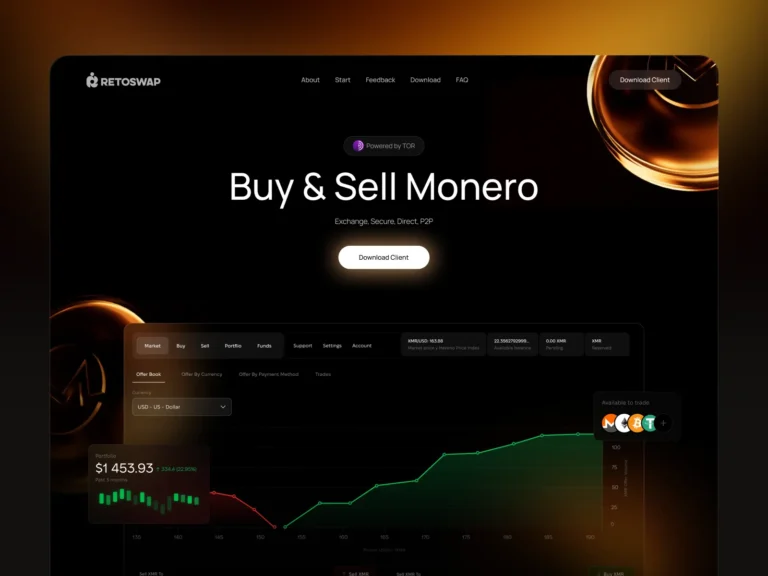
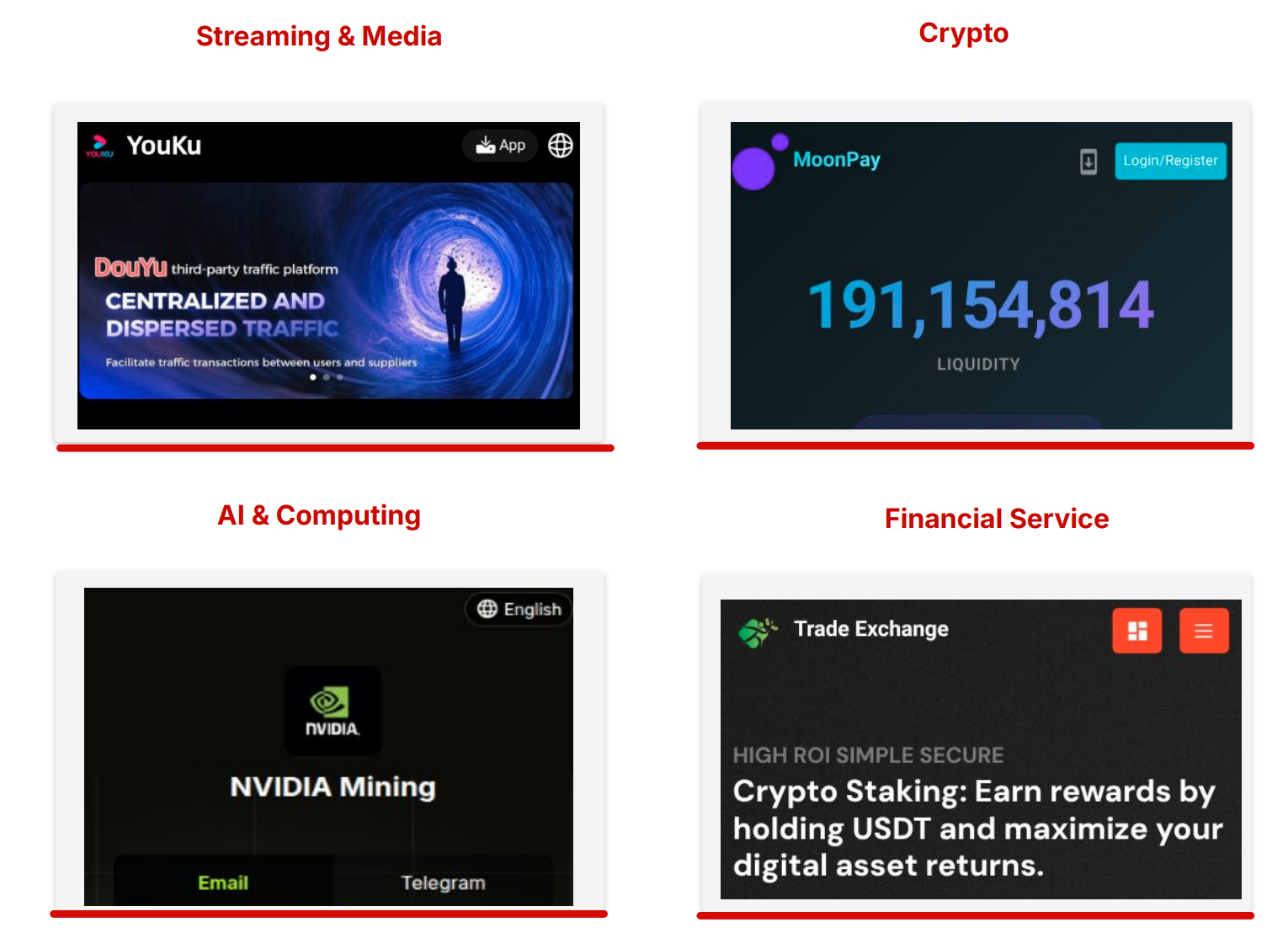
The researchers at CTM360 detailed the FEMITBOT toolkit, which facilitates the execution of large-scale fraudulent campaigns through Telegram. These deceptive mini-apps impersonate cryptocurrency exchanges, financial institutions, AI initiatives, streaming services, and mining pools. Among the entities targeted for impersonation are BBC, Netflix, Binance, Youku, Bitget, OKX, MoonPay, NVIDIA, CoreWeave, and Circle.
A recurring API response featuring a “FEMITBOT platform” greeting enabled investigators to interlink disparate malicious campaigns. CTM360 also identified a persistent correlation between Telegram bots and phishing domains. The bot serves as the primary ingress point, while the backend website manages authentication, renders the interface, processes payments, and harvests data. This architecture allows the operators to expeditiously rebrand the interface without reconfiguring the underlying system.
According to the report, the infrastructure comprises over 60 active domains, more than 146 Telegram bots, at least 15 templates, and 25 JavaScript builds, supplemented by over 100 tracking pixels across 30 rebranded identities. The frontend is predicated on Vue.js and the Telegram WebApp SDK, featuring a diverse array of visual “skins,” support for over 22 languages, and various aesthetic themes.
The offensive narrative is constructed around the themes of credibility and incremental engagement. Potential victims are lured through Meta advertisements or Telegram invitations promising passive income. Upon bot activation, the mini-app retrieves Telegram WebApp metadata, automatically generates a session, and presents a personalized dashboard replete with fabricated earnings, countdown timers, bonuses, and ephemeral offers. To “withdraw” these illusory accumulations, the user is coerced into making an initial deposit or recruiting additional participants.
Furthermore, CTM360 highlighted the sophisticated marketing discipline employed by FEMITBOT operators. The campaigns utilize Meta and TikTok pixels to monitor registrations, inaugural deposits, and subsequent transactions. Such granular analytics empower the criminals to refine their lures and reallocate traffic between high-performing sources.
In certain instances, the fraudulent sites offered APK files for manual installation. The configuration permitted direct file distribution, rendering pages within embedded browsers, or presenting PWA (Progressive Web App) prompts to encourage placement on the home screen. File nomenclature was meticulously selected to mimic legitimate applications or minimize suspicion.
In such sophisticated schemes, the peril resides not merely in the counterfeit website, but in the familiar environment that envelopes it. As the friction between a user and a promised reward diminishes, the imperative to rigorously scrutinize the source, the domain, and any solicitation for funds or manual software installation becomes paramount.
Support Our Threat Intelligence
If you find our technology report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee