A critical vulnerability within cPanel, of which server proprietors were apprised only in late April, has proven significantly more deleterious than initial assessments suggested. It has recently emerged that adversaries were actively exploiting this breach to seize control of hosting environments for a full two months prior to the dissemination of an official warning, leaving administrators blissfully unaware of the impending peril. The magnitude of this crisis encompasses millions of digital properties, including WordPress projects, corporate services, and essential email infrastructures.
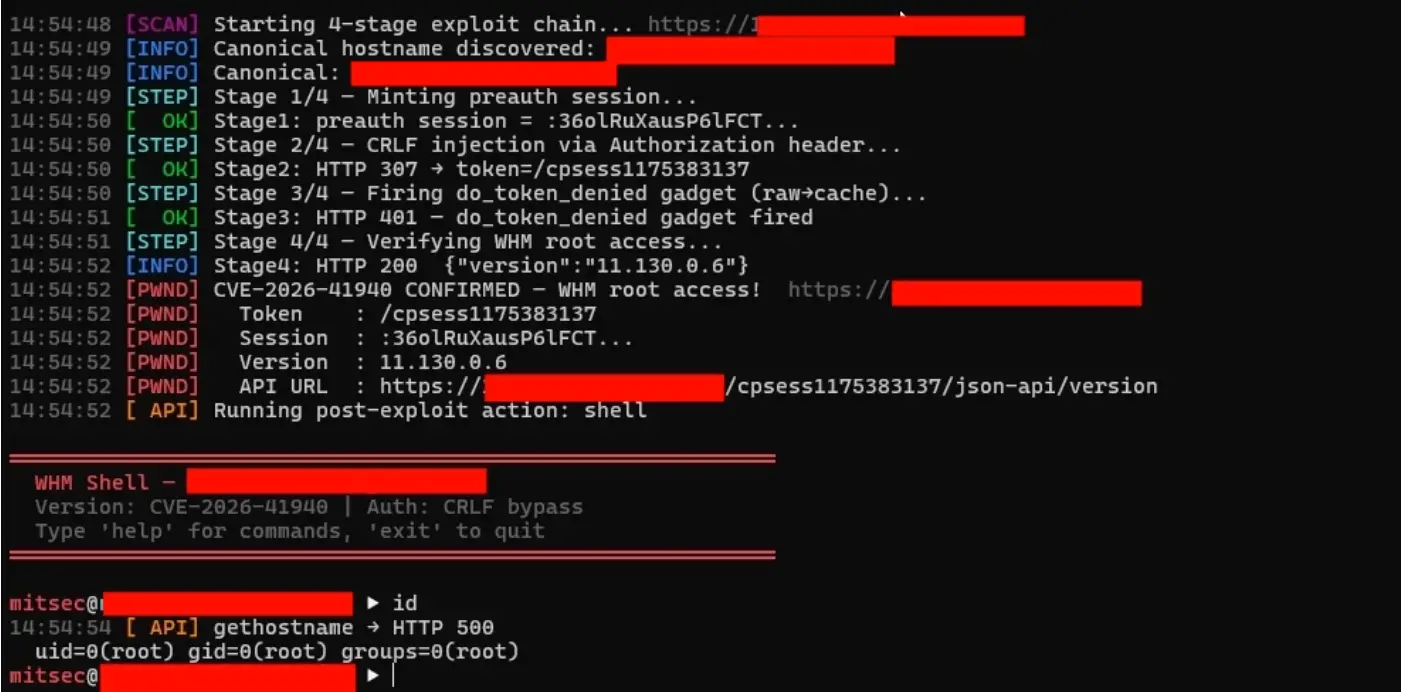
Daniel Pearson, CEO of KnownHost, reported that the nascent attempts at exploitation were documented as early as February 23, 2026. However, a public advisory did not manifest until April 28. Throughout those sixty-four days, server owners were furnished with neither security patches, a CVE identifier, nor defensive recommendations.
The vulnerability, subsequently designated as CVE-2026-41940, was assigned a near-maximal CVSS score of 9.8. The defect resides in an authentication bypass flaw within cPanel and WHM, enabling a remote assailant to secure root privileges without the necessity of credentials. Such an incursion grants unfettered access to all user accounts, domains, databases, and server configurations. Within shared hosting environments, the subversion of a single node effectively compromises hundreds of tenant websites simultaneously.
Susceptible versions include cPanel and WHM from 11.86.0 through 11.136.0, as well as WP Squared iterations prior to 136.1.7. Experts emphasize that the compromised code had persisted within the product architecture for several years.
Following the public disclosure, malicious actors swiftly orchestrated expansive offensives. According to Censys telemetry, over 15,000 infected cPanel and WHM servers were identified participating in deleterious activity by May 1 alone. Certain syndicates deployed the Sorry Ransomware, which appends the .sorry extension to encrypted files and predominantly targets WordPress installations. Simultaneously, other actors integrated a Mirai botnet variant, identified as nuclear.x86, into the compromised hosts.
Rapid7 estimated the population of potentially vulnerable servers at approximately 1.5 million, while Censys identified over a million publicly accessible instances of cPanel and WHM. Prominent providers exhibiting the highest concentrations of infected nodes include DigitalOcean, OVH, Hetzner, Vultr, and GoDaddy.
On April 30, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) incorporated CVE-2026-41940 into its Known Exploited Vulnerabilities (KEV) catalog, mandating that federal agencies remediate the flaw by May 3.
Security specialists caution that a mere software update is insufficient for comprehensive remediation. Any server exposed to the internet between February and April should be regarded as potentially compromised; administrators are urged to conduct rigorous forensic audits for latent malware, unauthorized SSH keys, and suspicious cron scheduled tasks.
Support Our Threat Intelligence
If you find our technology report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee