Adversaries increasingly find that compromising a smartphone is no longer a prerequisite for intercepting messages containing one-time passcodes; instead, they need only exploit a vulnerability within the nexus between a mobile device and a personal computer. Cisco Talos has elucidated an offensive maneuver in which the CloudZ RAT malware leveraged the Microsoft Phone Link application alongside a novel module designated as Pheno to potentially intercept SMS transmissions, notifications, and ephemeral authentication codes.
According to Talos experts, this malicious campaign commenced no later than January of the current year. While the inaugural vector of infiltration remains undetermined, infected systems were observed executing a fraudulent ScreenConnect update installer. Upon execution, the malicious file retrieved an intermediate .NET loader, which subsequently deployed the modular CloudZ RAT.
Integrated into Windows 10 and Windows 11, Phone Link facilitates the synchronization of a computer with a smartphone, rendering notifications, SMS threads, and call histories accessible on the PC. This synchronized data is archived locally within SQLite databases, specifically files adhering to the PhoneExperiences-.db nomenclature. It was precisely this architecture that the assailants sought to subvert.
The Pheno module scrutinized the host machine for an active Phone Link configuration by identifying processes such as YourPhone, PhoneExperienceHost, and Link to Windows, subsequently recording discovered identifiers and file paths within administrative directories. A supplementary audit sought proxy indicators associated with the local channel through which Phone Link facilitates data transmission between the PC and the mobile device. Upon identifying a match, the module designated the session as potentially active.
CloudZ RAT was capable of harvesting the outputs generated by Pheno from a temporary directory and exfiltrating the data to a command-and-control server. Cisco Talos correlates this activity with concerted efforts to purloin credentials and, plausibly, one-time passcodes derived from SMS or authenticator app notifications. Notably, the malware achieved this without necessitating the installation of any supplementary application on the smartphone itself.
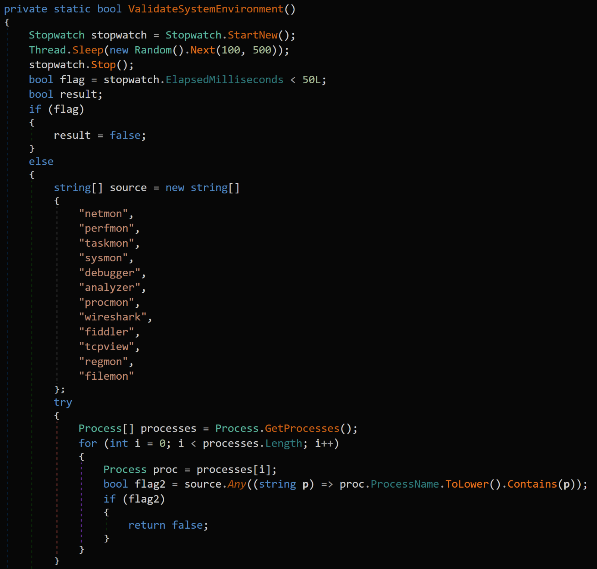
The loader identified by Cisco Talos was authored in Rust and masqueraded as systemupdates.exe or Windows-interactive-update.exe. To ensure persistence, it orchestrated a Windows task titled SystemWindowsApis, executed a .NET component via regasm.exe, and maintained its presence across system reboots. Prior to initialization, CloudZ conducted environmental reconnaissance for artifacts of forensic analysis, seeking out Wireshark, Fiddler, Procmon, Sysmon, virtual machines, and sandboxes.
CloudZ safeguards its configuration through encryption, decrypting it solely within volatile memory before establishing a TCP connection to its command-and-control infrastructure. The malware supports a suite of mandates for system reconnaissance, shell command execution, browser data exfiltration, screen recording, module retrieval, and file management. It utilizes curl, PowerShell, or bitsadmin to acquire additional components, ensuring operational continuity even in the absence of specific utilities.
Cisco Talos has integrated threat detection for this menace into ClamAV and Snort, while disseminating indicators of compromise via its GitHub repository. Such information stealers, meticulously engineered to harvest browser data and user accounts, are becoming progressively more sophisticated.
Support Our Threat Intelligence
If you find our technology report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee