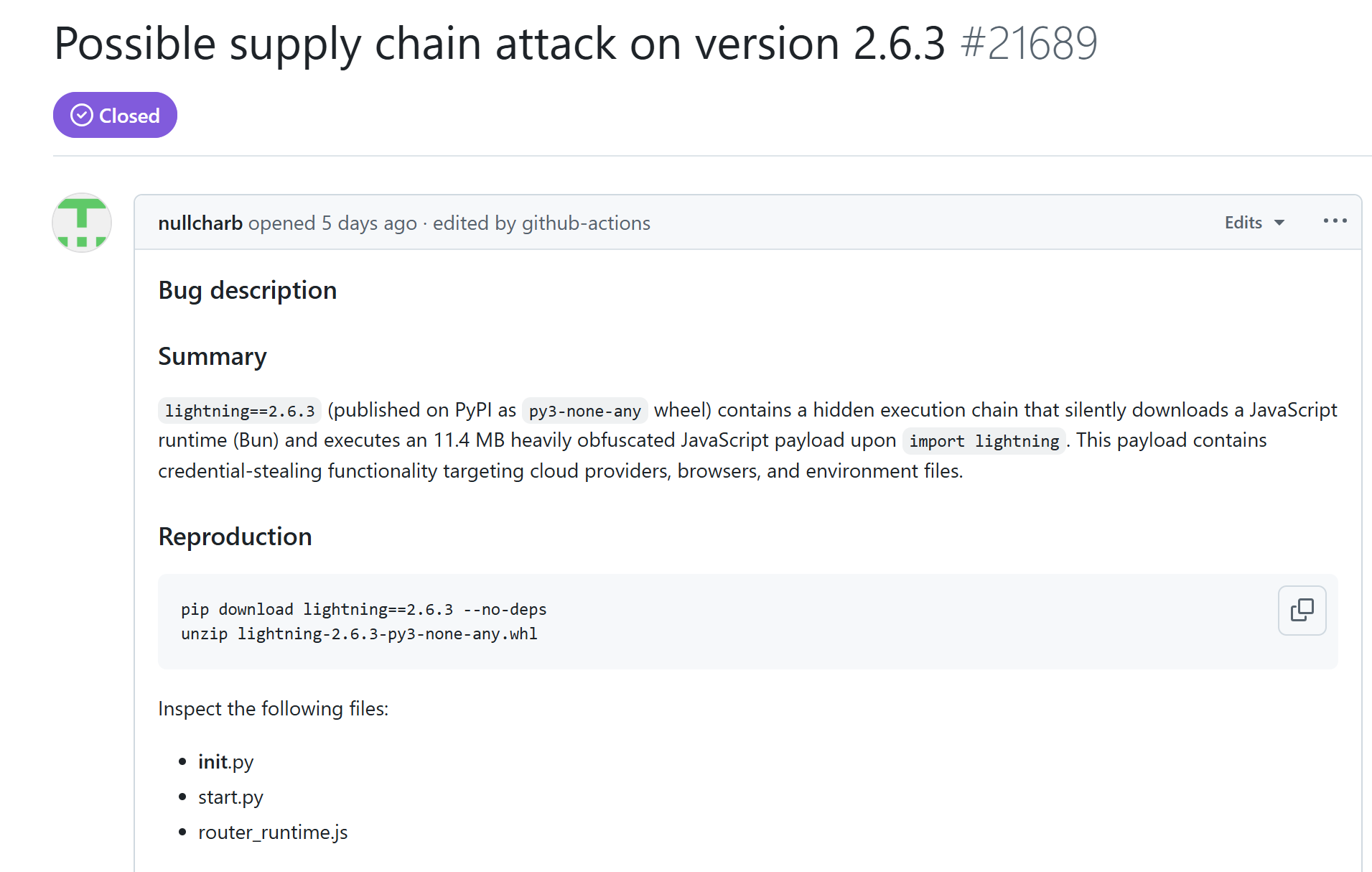
A compromised iteration of a widely utilized AI development tool has been identified, harboring the capability to surreptitiously exfiltrate access keys, authentication tokens, and browser data. The breach specifically targeted the PyTorch Lightning package on the Python Package Index (PyPI), where the hazardous build was disseminated under version 2.6.3.
Lightning AI disclosed this supply chain attack on April 30. According to the developers, version 2.6.3 contained a concealed execution sequence triggered upon the importation of the lightning package. Once activated, the malicious code initiated a background process to retrieve the Bun v1.3.13 JavaScript runtime from GitHub, subsequently executing an 11.4 MB obfuscated file designated router_runtime.js.
PyTorch Lightning is indispensable for the pre-training and fine-tuning of artificial intelligence models; its ubiquity is evidenced by over 11 million downloads in the preceding month alone. Given this immense popularity, even the transient presence of a tainted version within PyPI posed a profound risk to developers, research institutions, and enterprises dependent on cloud infrastructure.
The Microsoft Threat Intelligence team reported that Microsoft Defender identified and neutralized the malicious activity within client environments, prompting an immediate notification to the package maintainers. According to Microsoft’s telemetry, the incursion impacted a limited number of devices and, based on current evidence, remained confined to a narrow subset of environments.
The payload, categorized by Defender as ShaiWorm, was engineered to harvest API keys, secrets, GitHub tokens, and sensitive data from .env files, as well as credentials from the Chrome, Firefox, and Brave browsers. This sophisticated infostealer also queried the APIs of AWS, Azure, and GCP cloud services in an attempt to hijack credentials, while maintaining the capacity to execute arbitrary system commands.
Lightning AI has issued a mandate that any users who installed version 2.6.3 and executed import lightning must deem all secrets, keys, and tokens as potentially compromised. The developers strongly advise the immediate rotation of all such credentials and a thorough audit of environments for vestiges of suspicious activity.
Currently, the PyTorch Lightning entry on PyPI has been reverted to the secure version 2.6.1. The definitive cause of the compromise remains under investigation. The project team is diligently scrutinizing how the adversaries gained ingress into the build or release pipeline, while concurrently auditing other recent releases for analogous malicious components.
Support Our Threat Intelligence
If you find our CVE report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee