Cerberus has once again become the focal point of a controversy where a mobile security application metamorphoses into an instrument of surreptitious surveillance. According to findings by Mark Esher, author of the technical blog hexproof, the program—currently available on Google Play—possesses the capability to clandestinely photograph the user, record audio, track geographic coordinates, and execute commands via a remote administrative dashboard.
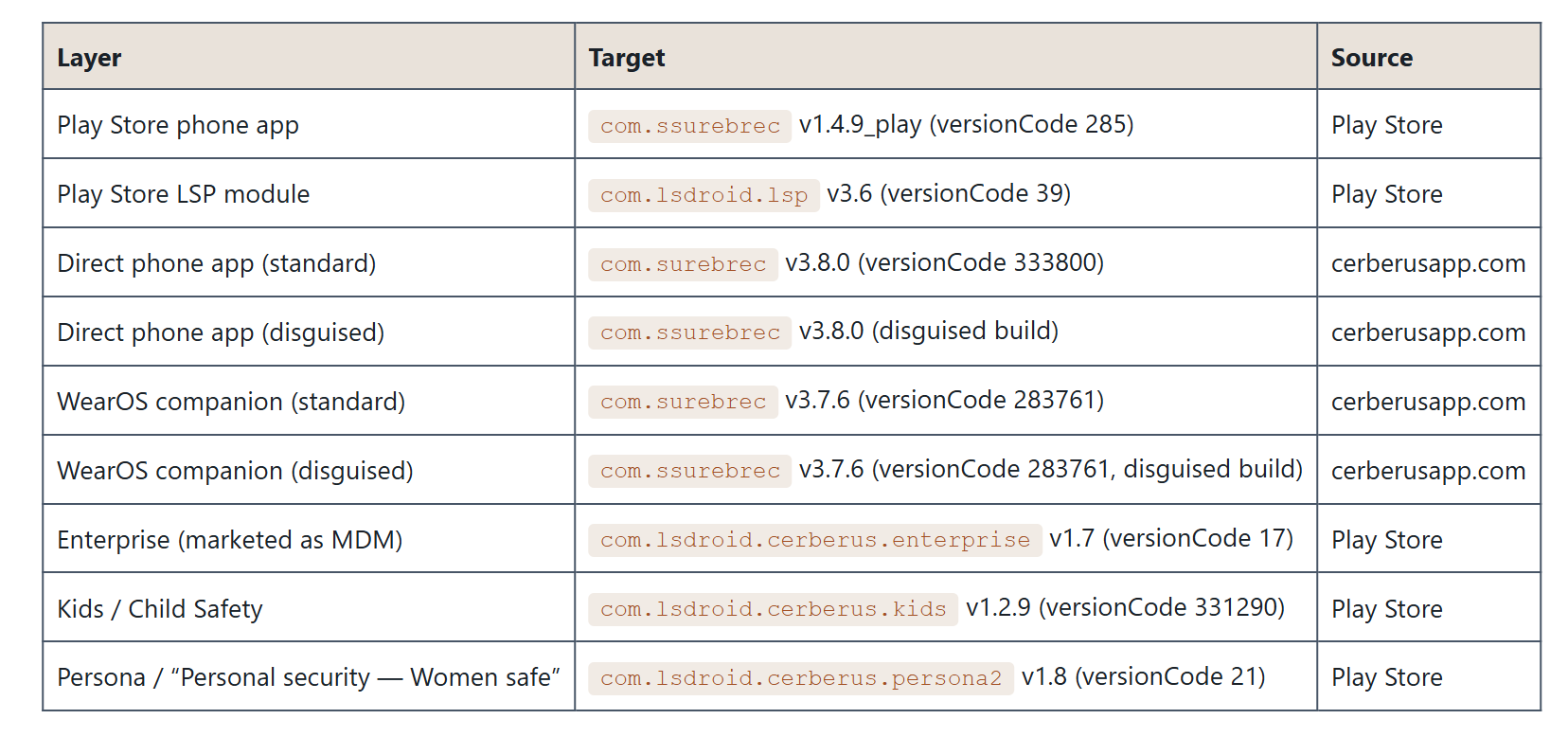
The application in question is Cerberus Anti-theft, developed by the Italian entity LSDroid SRL. Available for a monthly subscription of five euros, the extant version has resided on Google Play since October 4, 2023. Esher asserts that the software can trigger covert imagery from both front and rear cameras, record video and ambient audio, access contacts, call logs, and SMS messages, dispatch texts on behalf of the owner, lock the device, expunge data, and project arbitrary text upon the lock screen.
Particular scrutiny was directed toward the “Fake Shutdown” functionality. Cerberus can simulate an Android power-off interface nearly indistinguishable from the native system, subsequently darkening the display while maintaining the smartphone’s operational state. In this dormant facade, the camera, microphone, and GPS sensors remain active.
The ecosystem includes ancillary components as well. Lock Screen Protector, published by the same developer account, requests access to Android’s Accessibility Services. Once authorized, the program can read on-screen content, simulate gestures, and capture screenshots. Furthermore, it intercepts attempts to power down the device by suppressing the system power menu and transmitting an image of the lock screen to the Cerberus interface.
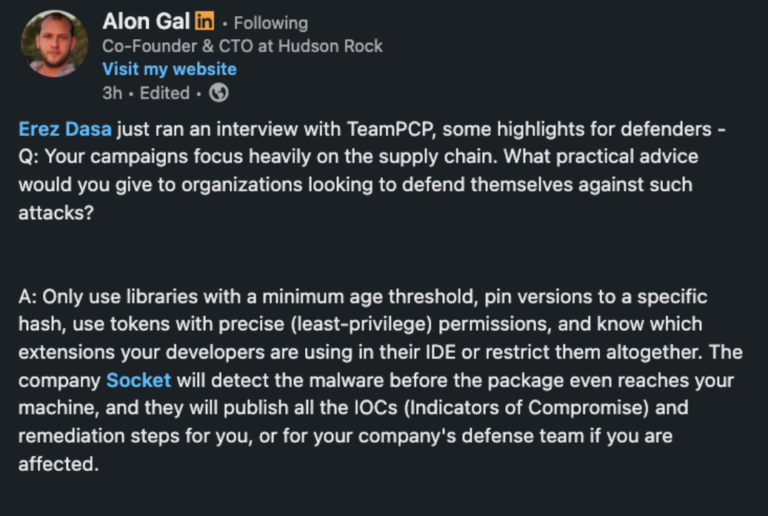
According to Esher, Cerberus has previously been identified in academic research as stalkerware utilized in domestic contexts. In 2018, scholars from Cornell Tech and NYU alerted Google to these risks. Although the application was subsequently purged from Google Play for disparate reasons—specifically pertaining to the installation of third-party software—it resurfaced in 2023 under a novel package name, purportedly retaining the vast majority of its predecessor’s invasive capabilities.
The disclosure also highlights that several LSDroid applications utilize the HiddenApiBypass library, which facilitates access to restricted Android functions. The author contends that such components, coupled with Cerberus’s feature set, contravene Google Play’s policies regarding malicious behavior and stalkerware.
According to the analysis, Google is inextricably linked to the Cerberus infrastructure through multiple services: Google Play facilitates its distribution, AdMob serves its advertisements, and Firebase acts as the conduit for transmitting remote commands to infected devices. The author maintains that Google was apprised of these findings prior to publication; however, the applications remained accessible at the time of the report’s release.
For potential victims, the paramount risk encompasses not only the surveillance itself but also the hazards of attempted self-remediation. Cerberus and its associated modules can notify an operator of changes in permissions or other diagnostic actions on the device. Consequently, specialists in domestic violence advocacy typically recommend that compromised hardware be examined only through a secure device and with the guidance of professional organizations.
Support Our Threat Intelligence
If you find our CVE report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee