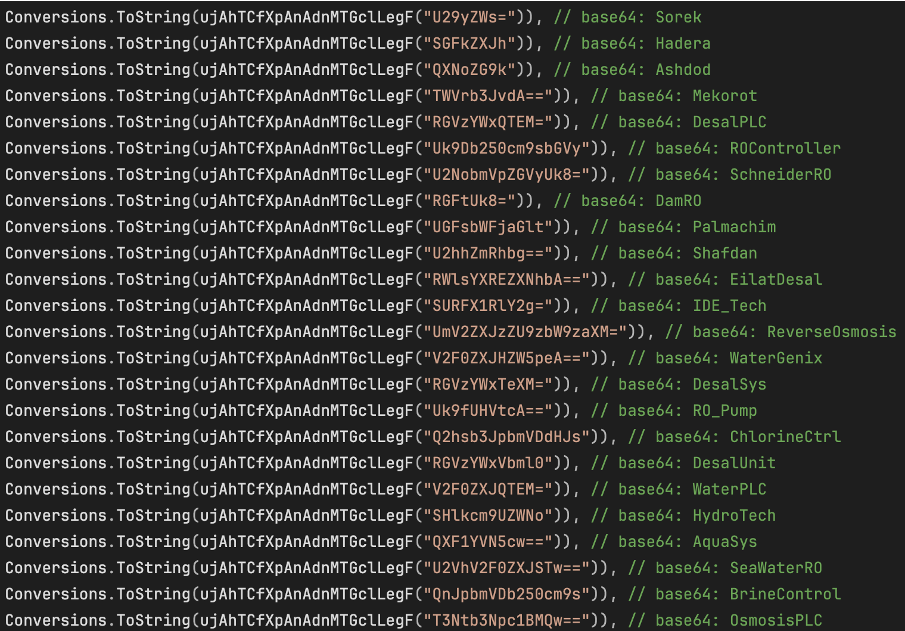
Strings in the target list, all related to Israel and water treatment
Malicious software, identifying itself as ZionSiphon, has emerged with a singular, physical objective: the subversion of water infrastructure. Darktrace recently dissected an attempt to orchestrate an incursion into Israel’s water purification and desalination facilities, specifically targeting systems that regulate chlorine concentrations and hydraulic pressure.
Within the architecture of ZionSiphon lies a conventional suite of maneuvers—privilege escalation, system persistence, and lateral movement via removable media. However, its subsequent behavior is markedly atypical. The code meticulously verifies its environment, endeavoring to operate exclusively within specific IP address ranges associated with Israel. Encoded within its binaries are Base64 strings containing geopolitical declarations in support of Iran, Palestine, and Yemen, accompanied by overt threats of poisoning directed at the denizens of Tel Aviv and Haifa.
The program discriminates its targets not merely by geography, but through specific markers of water utility infrastructure. Embedded within the source code are the names of entities inextricably linked to the national water network, such as Mekorot and various desalination plants. The malware scrutinizes processes, directories, and configuration files characteristic of reverse osmosis systems, industrial pumps, and chlorination units. Should these criteria be met, the device is deemed a viable target.
Upon execution, ZionSiphon attempts to secure administrative hegemony via PowerShell, subsequently cloaking itself as a legitimate Windows process named svchost.exe. To maintain its veil of secrecy, the file is designated as hidden and integrated into the system’s startup routine under an innocuous alias. If the environment fails to meet its exacting conditions, the program self-terminates, leaving behind a transient file noting that the target was non-compliant.
In the event of a “successful” deployment, ZionSiphon initiates its interference. It seeks out configuration files to append parameters designed to augment chlorine levels and elevate systemic pressure—setting maximum flow rates and activating pumps. In the absence of such files, the malware transitions to an active network reconnaissance phase.
During this phase, the code probes the local area network for industrial devices by scanning ports associated with operational technology protocols, such as Modbus. Upon discovering a susceptible controller, it issues commands to read and manipulate registers, specifically targeting values that govern chemical concentrations.
Nevertheless, the implementation remains technically suspect. The geographical verification logic is fundamentally flawed, rendering the program incapable of accurately identifying even a valid system. Furthermore, modules intended for other industrial protocols, such as DNP3 and S7, appear incomplete and fail to generate functional commands, suggesting prototypes that were never brought to fruition.
A dedicated module facilitates propagation via USB drives, wherein ZionSiphon replicates itself onto removable media and creates deceptive shortcuts, masquerading its execution as the opening of mundane documents. While currently appearing underdeveloped or in a nascent testing phase, the structural intent of the malware signifies a calculated interest in Industrial Control System (ICS) sabotage. This represents a shift away from traditional data exfiltration or extortion toward a direct attempt to manipulate physical processes—in this instance, the very lifeblood of a nation’s water supply.
Support Our Threat Intelligence
If you find our technology report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee