The HeartlessSoul collective is surreptitiously scavenging for telemetry that typically resides far beneath the surface of mundane documentation. Their pursuit transcends conventional office formats, focusing instead on geospatial intelligence—encompassing maps, infrastructure schematics, and topographical terrain models. Such data holds superlative value for the industrial and aviation sectors, serving as the primary objective for these adversaries.
Experts from Kaspersky have been monitoring HeartlessSoul since February 2026, unearthing nascent details of their operational maneuvers. The group has been active since at least the autumn of 2025, primarily targeting governmental entities and corporations entrenched in industrial manufacturing and aviation systems, alongside select individuals.
The infection vector commences in a deceptively routine fashion. Typically, a victim receives a missive containing an archive, within which resides a malicious shortcut, spreadsheet add-in, or installer. Execution triggers a cascade of commands that covertly deploy the malicious payload. In certain instances, the attackers exploit the ZDI-CAN-25373 vulnerability, which facilitates the concealment of a malicious command within a shortcut, presenting only an innocuous path fragment to the user.
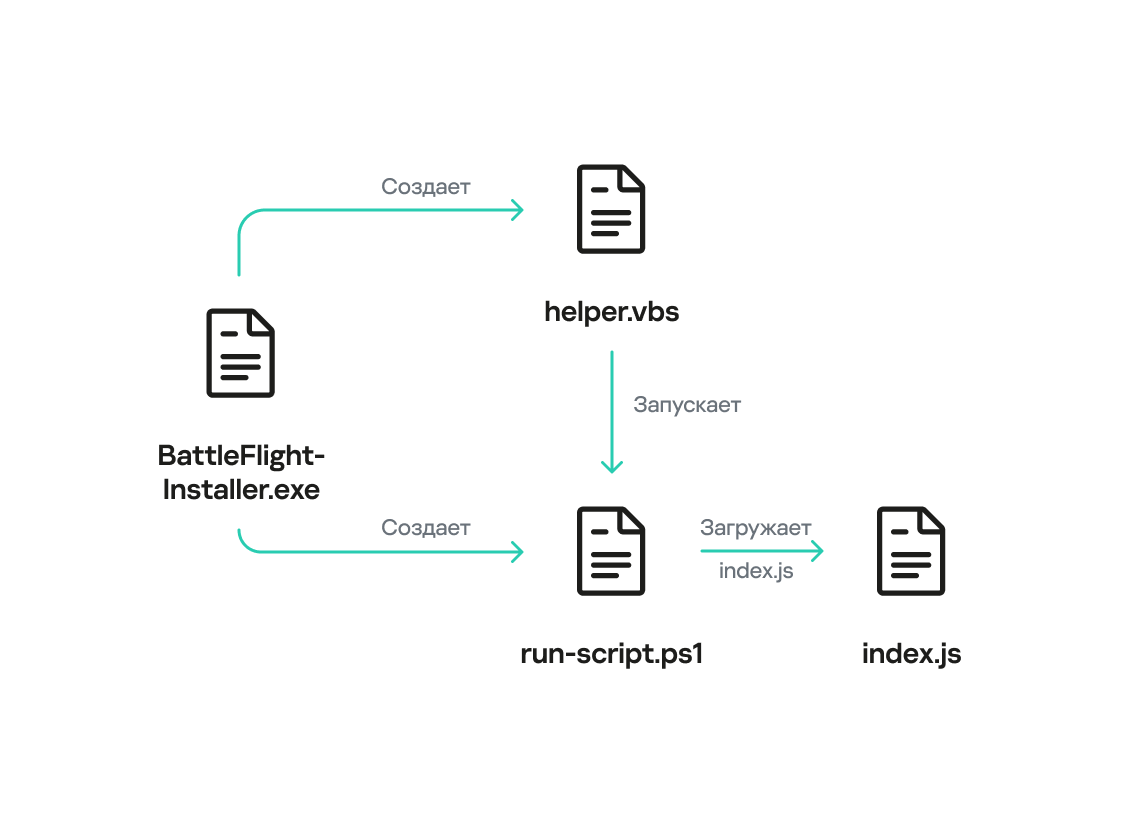
Alternatively, the adversaries architect fraudulent portals masquerading as “aviation software” or ubiquitous services, proliferating them via deceptive advertising. Once a user downloads and executes the installer, the infection takes root. In one notable campaign, the malicious archive was even distributed through the SourceForge platform, disguised as a utility for optimizing gaming connectivity.
Upon execution, a JavaScript runtime environment is established on the device, followed by the deployment of the primary module—a Remote Access Trojan (RAT). To ensure persistence, the malware integrates itself into the system’s startup sequence and creates scheduled tasks to withstand reboots. Subsequently, the data harvesting begins: the code captures screenshots, records keystrokes, exfiltrates clipboard contents, and executes commands via PowerShell. Specialized modules further aggregate system telemetry, user privileges, and the precise geographical coordinates of the device.
Of particular significance is the specific taxonomy of files targeted by the trojan. Beyond standard documents and archives, it purposefully exfiltrates geospatial formats, including map files, GPS tracks, cartographic projects, and digital elevation models. This data provides a meticulous representation of infrastructure—ranging from roadways and engineering networks to strategic facilities. Additionally, the malware scavenges browser telemetry, including cookies and encryption keys, and copies the contents of Telegram directories. All amassed intelligence is archived and dispatched to the adversaries’ command-and-control servers.
The attack infrastructure partially intersects with another collective designated as GOFFEE. The domains and servers utilized in these campaigns frequently overlap, and the lures exhibit striking similarities; both groups rely heavily on PowerShell for the deployment and execution of malicious components. HeartlessSoul remains an active threat, demonstrating a calculated interest in industrial data, specifically pertaining to geography and infrastructure—a focus that signifies the strategic gathering of high-value intelligence.