Cybercriminals have devised a cunning method to transform outdated Discord server links into digital traps: a newly...
Malware
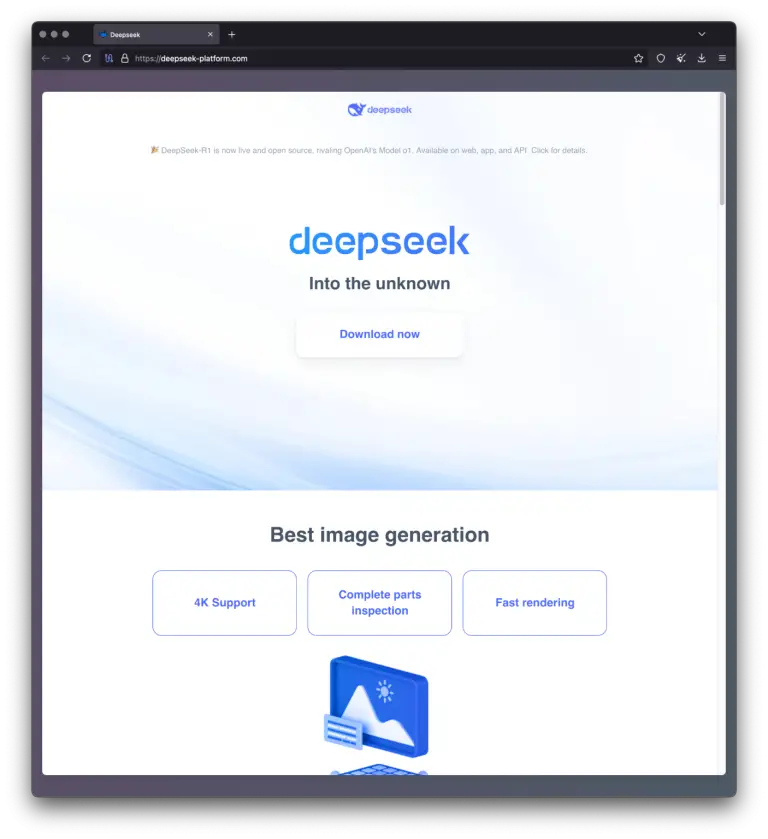
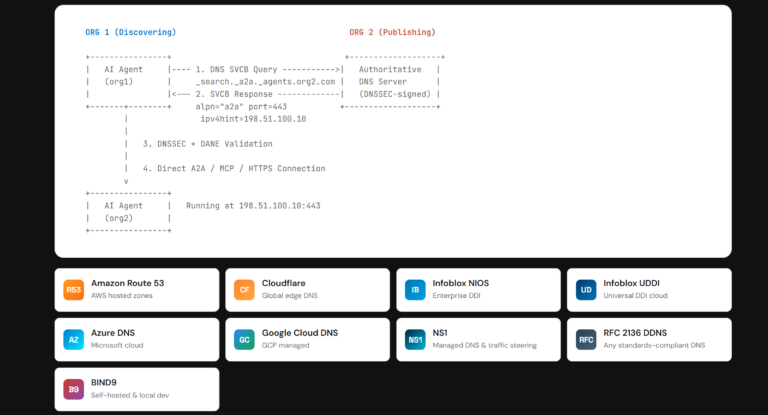
As the popularity of language models continues to surge, cybercriminals are increasingly exploiting this momentum to orchestrate...
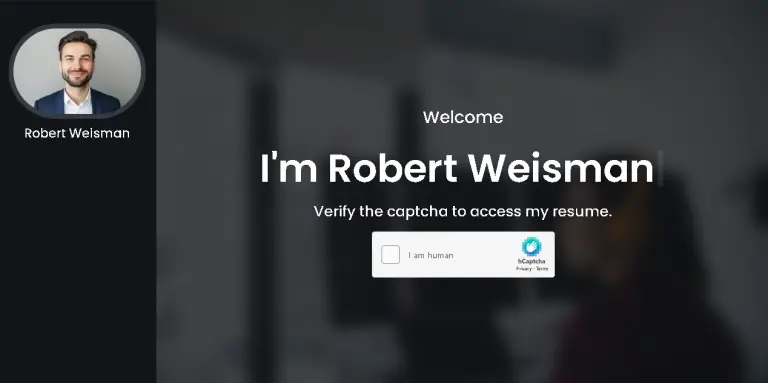
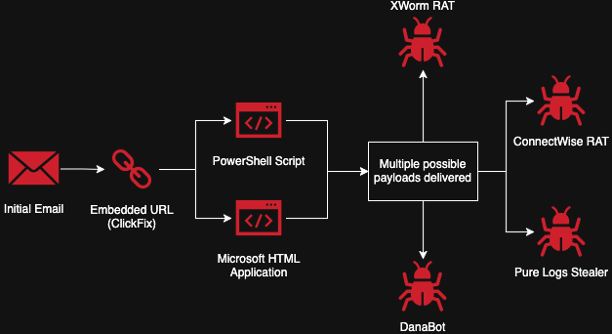
The financially motivated hacking collective FIN6 has resurfaced with a sophisticated phishing campaign that leverages counterfeit resumes...
Cybersecurity specialists at Trellix have uncovered a previously undocumented malware strain written in Rust, dubbed Myth Stealer,...
Beginning in July 2025, Microsoft will automatically block email attachments with the extensions .library-ms and .search-ms in...
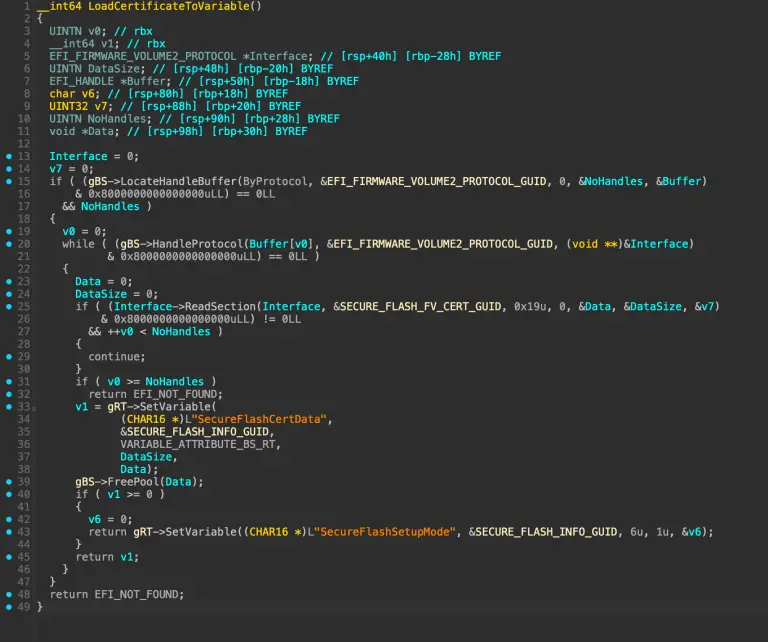
Nearly all modern computers with Secure Boot enabled have been exposed to critical risk due to a...
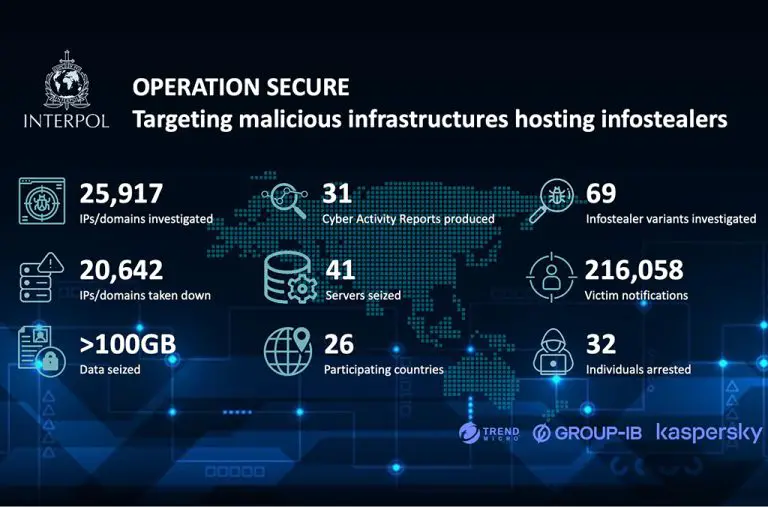
An international law enforcement operation, codenamed Operation Secure, has culminated in the large-scale dismantling of cybercriminal infrastructure...
In the spring of 2024, an obscure tool known as Skitnet—also appearing under the alias “Bossnet”—surfaced on...
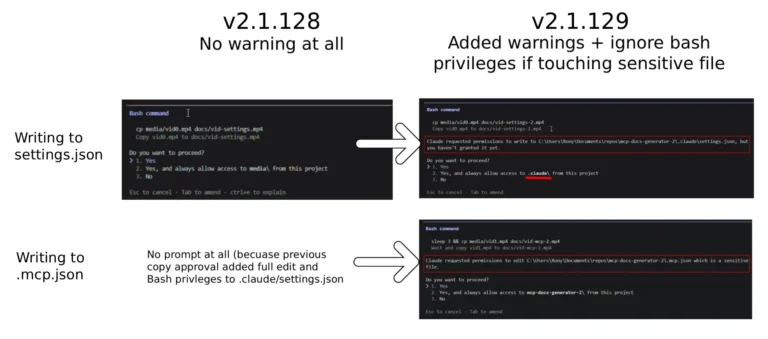
Two malicious packages were recently discovered within the widely used JavaScript package registry, npm. Beneath their seemingly...
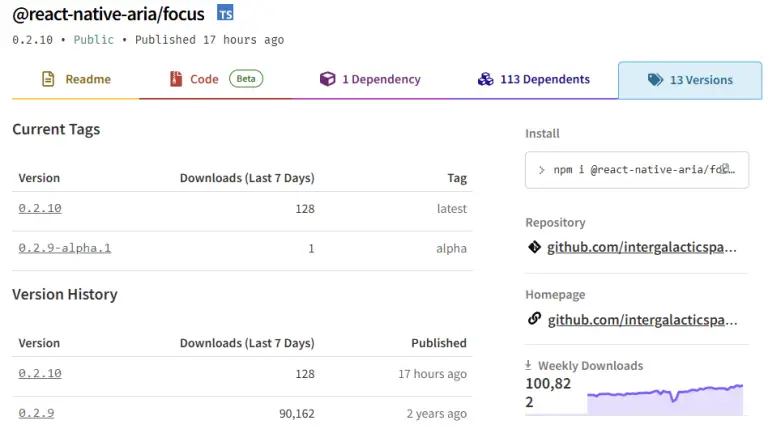
A large-scale supply chain attack has been identified on the NPM platform: threat actors compromised 17 widely...
A new wave of cyberattacks has been recorded in Ukraine, targeting the destruction of critical infrastructure. At...
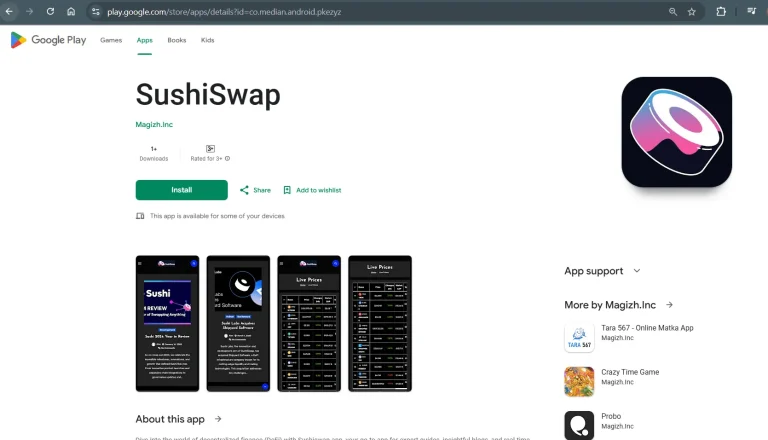
Even if you download applications exclusively from Google Play, this does not always guarantee safety—particularly when it...
At first glance, it appears to be nothing more than a routine security check. In reality, it...
The U.S. Department of State has announced a reward of up to $10 million for information leading...
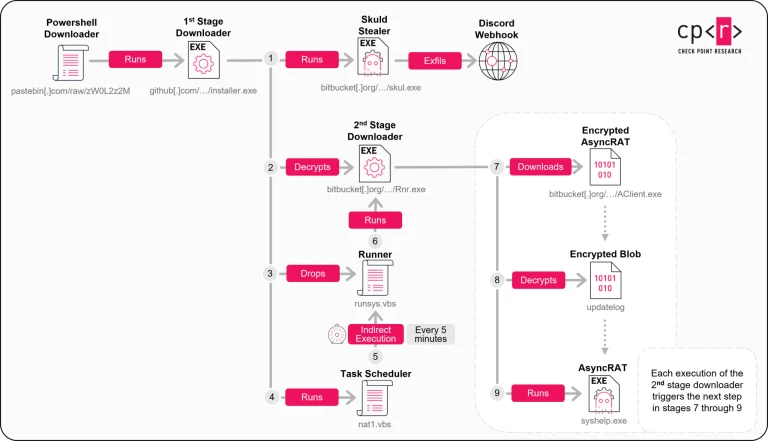
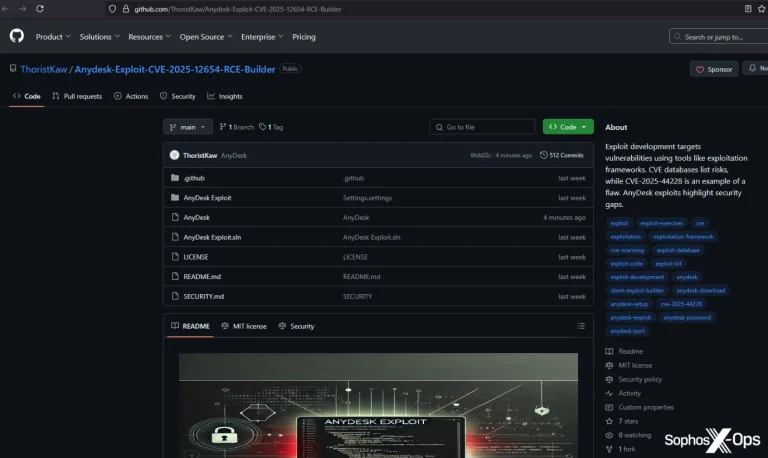
A recently uncovered malicious campaign is leveraging GitHub as a trap for security professionals, gamers, and even...