CrowdStrike has issued a formal warning regarding a perceptible metamorphosis in the strategies employed by extortionist collectives: adversaries are increasingly circumventing traditional security perimeters not through the compromise of workstations, but via the exploitation of trusted cloud environments. In such incursions, a breach may masquerade as a routine employee login to a corporate account, with the exfiltration of data commencing within mere minutes of ingress.
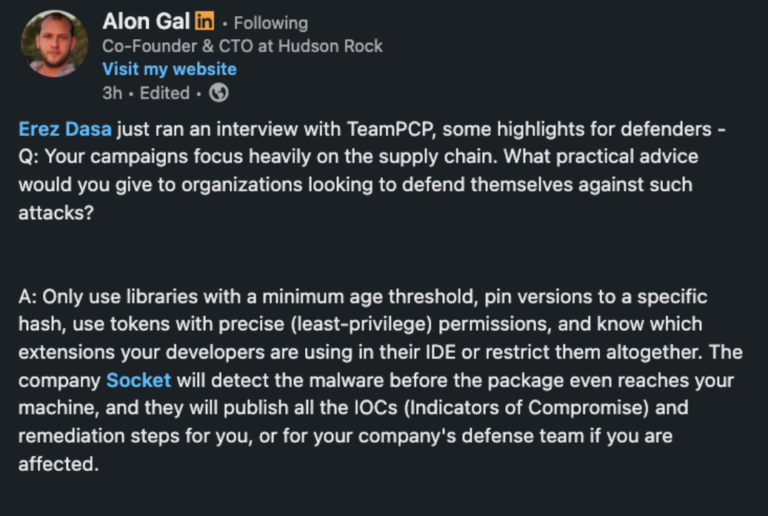
According to CrowdStrike’s telemetry, the groups designated as CORDIAL SPIDER and SNARKY SPIDER have, since October 2025, been orchestrating rapid assaults on SaaS (Software-as-a-Service) ecosystems utilizing sophisticated voice phishing (vishing). Masquerading as IT support personnel, the assailants manipulate employees into navigating to fraudulent Single Sign-On (SSO) portals. These deceptive domains meticulously mimic legitimate corporate interfaces, causing victims to overlook the artifice.
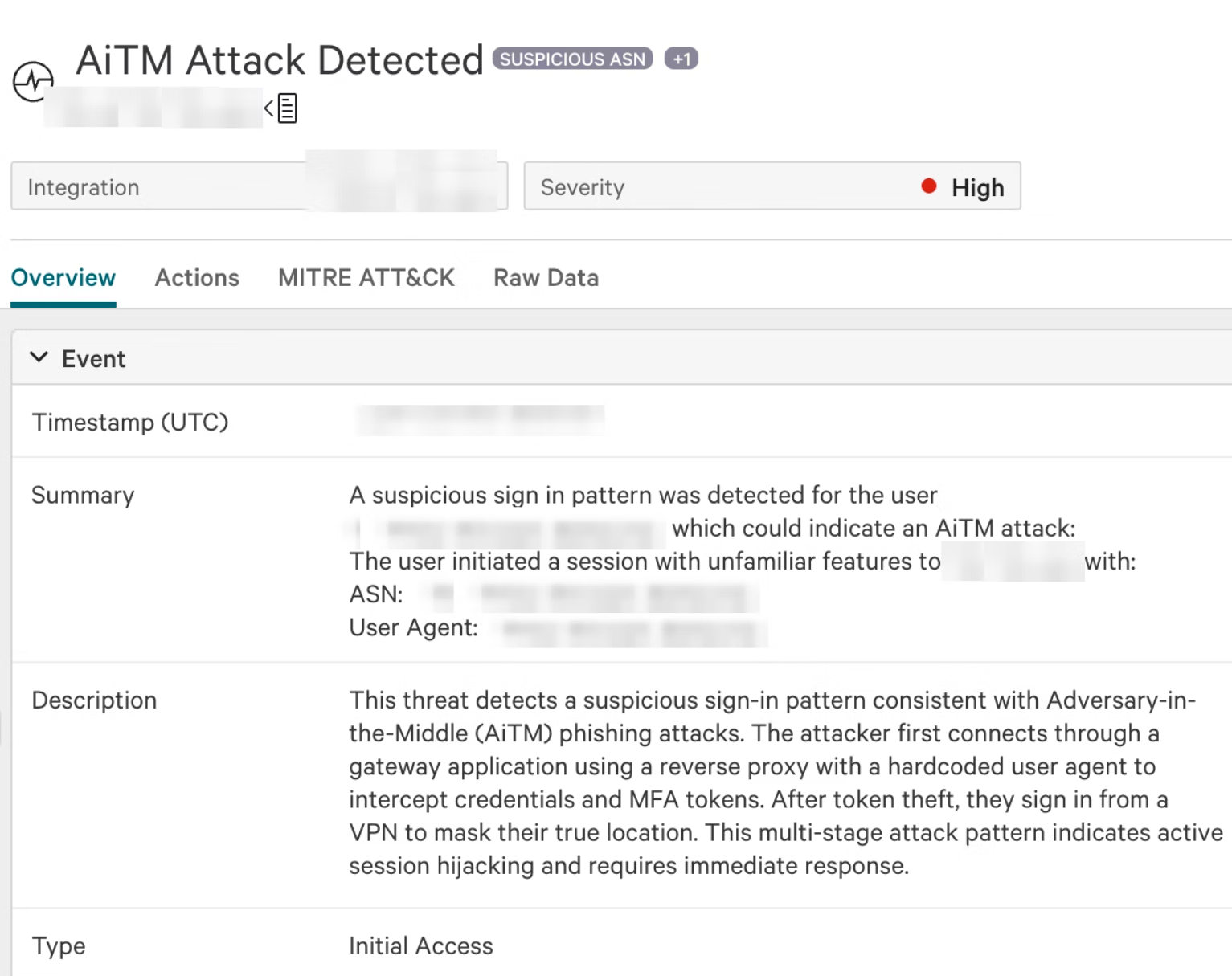
Upon the submission of credentials, the attackers intercept not only usernames and passwords but also active session tokens. This methodology facilitates seamless access to the overarching SSO infrastructure and its integrated SaaS applications without necessitating the independent compromise of each service.
To ensure persistence within the hijacked accounts, CORDIAL SPIDER and SNARKY SPIDER register their own Multi-Factor Authentication (MFA) devices. In several instances, pre-existing MFA configurations were purged prior to the enrollment of the new hardware. CrowdStrike observes that SNARKY SPIDER favored the Genymobile Android emulator, whereas CORDIAL SPIDER utilized a more diverse array of mobile devices and QEMU.
Subsequently, the perpetrators endeavor to obscure their digital footprints. SNARKY SPIDER, as noted by CrowdStrike, habitually deletes automated notifications regarding suspicious activity and establishes inbox rules to surreptitiously intercept and remove messages containing keywords such as “alert,” “incident,” or “MFA.” Consequently, the victim remains oblivious to warnings regarding unauthorized logins or the registration of unfamiliar devices.
Once established, these collectives scour SaaS platforms for sensitive documents and communications using highly targeted keywords, including “confidential,” “SSN,” “contracts,” and “VPN.” This reconnaissance enables the swift acquisition of internal agreements, employee records, and infrastructure telemetry.
The primary objective for both entities remains the bulk exfiltration of data from repositories such as SharePoint, HubSpot, and Google Workspace. CrowdStrike emphasizes that these incursions do not stem from inherent vulnerabilities within the SaaS platforms themselves; rather, they arise from suboptimal client configurations, the absence of phishing-resistant MFA, and excessively permissive access rights.
To camouflage their maneuvers, CORDIAL SPIDER and SNARKY SPIDER employ commercial VPNs and residential proxies, including Mullvad, NetNut, 9Proxy, Infatica, and NSOCKS. The utilization of residential proxies particularly complicates detection, as the resulting traffic appears synonymous with domestic IP addresses assigned to ordinary users.
CrowdStrike attributes these campaigns to the widening chasm between endpoint protection and visibility within SaaS environments. Even a robustly secured workstation provides little recourse once an adversary has assumed the identity of a legitimate user through a purloined session within the cloud.