China remains the most persistent and sophisticated cyber threat to the United States, according to the intelligence...
Security
The legacy domain of Microsoft Stream has been compromised and is now displaying a counterfeit Amazon webpage...
The personal contact information of key national security advisors to former U.S. President Donald Trump has surfaced...
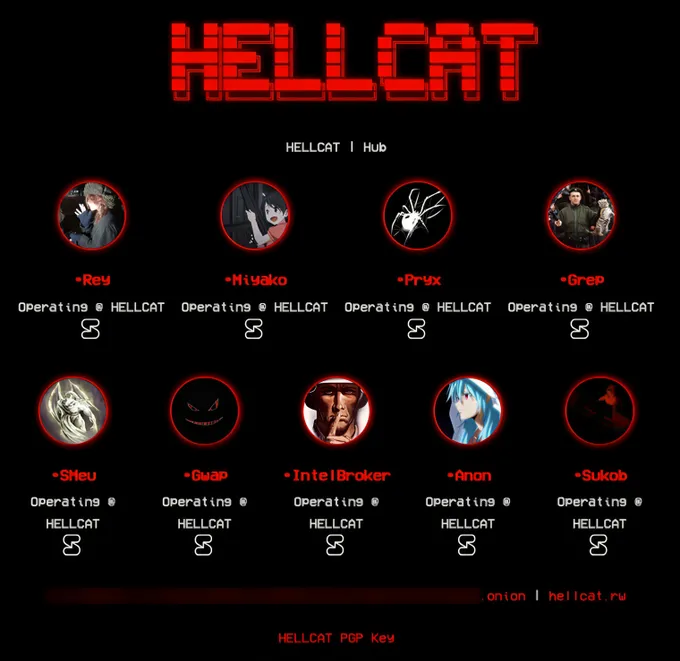
The Hellcat collective has found itself at the heart of a KELA investigation that has unveiled the...
The California-based law firm Greenberg Glusker has secured a $33 million arbitration award against T-Mobile, following a...
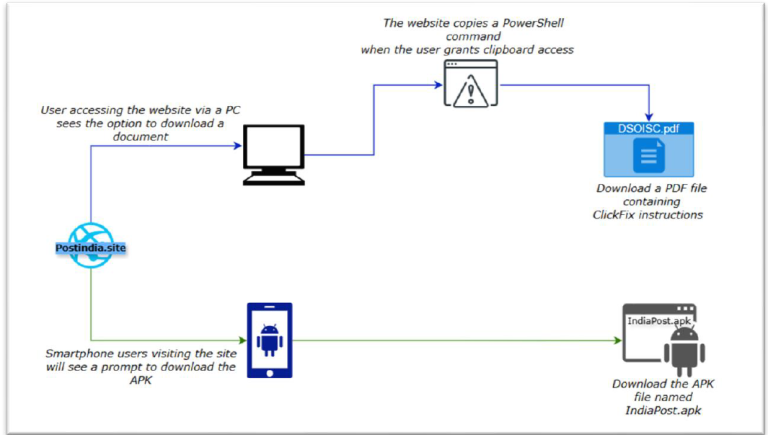
The Pakistan-linked threat actor APT36 has launched a sophisticated malware campaign by masquerading as the official website...
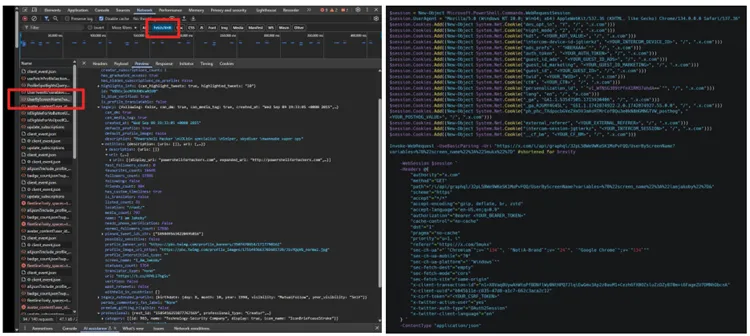
Despite the limitations imposed by Twitter’s official API, users continue to discover alternative methods for extracting internal...
The United Kingdom’s Information Commissioner’s Office (ICO) has imposed a £3.07 million fine on Advanced Computer Software...
In response to the growing wave of cyberattacks targeting digital education platforms, the French authorities have launched...
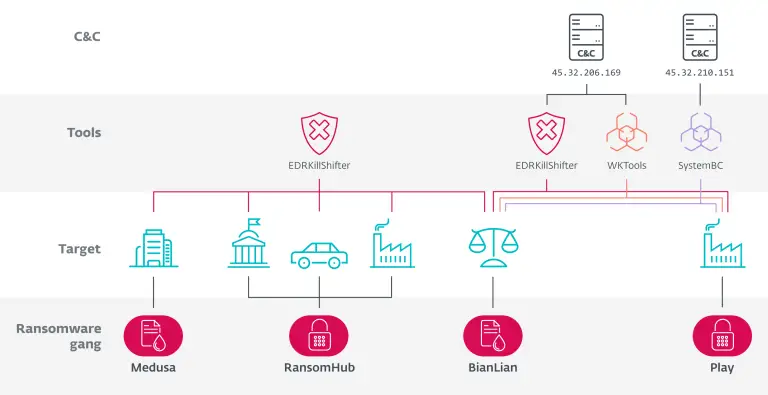
A recent investigation conducted by ESET has uncovered intricate ties between several ransomware groups — RansomHub, Medusa,...
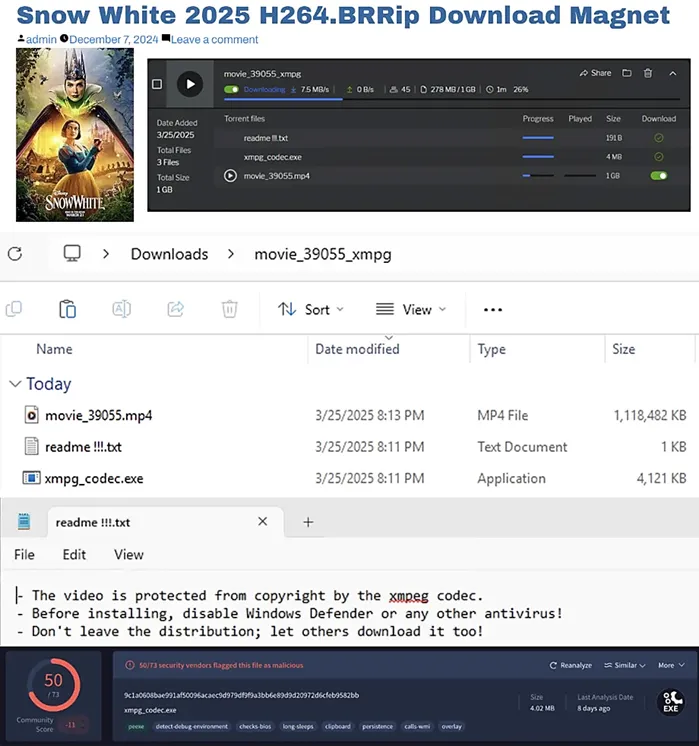
Disney’s latest adaptation of Snow White, which garnered a dismal rating of 1.5 out of 10 on...
At first glance, the seemingly innocuous name CoffeeLoader might lull one into a false sense of security....
Mozilla has released an emergency security update for Firefox, addressing a critical vulnerability reminiscent of one previously...
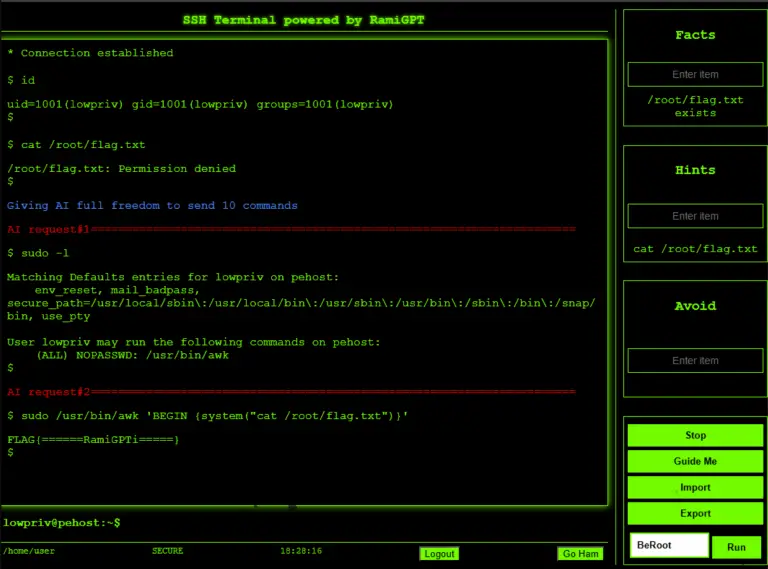
A developer operating under the pseudonym M507 has unveiled a new open-source initiative—RamiGPT, an AI-powered tool designed...
Malicious actors have adopted a new tactic in their attacks on the npm ecosystem—two nefarious packages clandestinely...