In the first half of May 2025, an international operation aimed at dismantling the infrastructure of Lumma...
Marks & Spencer (M&S), one of the United Kingdom’s largest retail giants, has announced an anticipated decline...
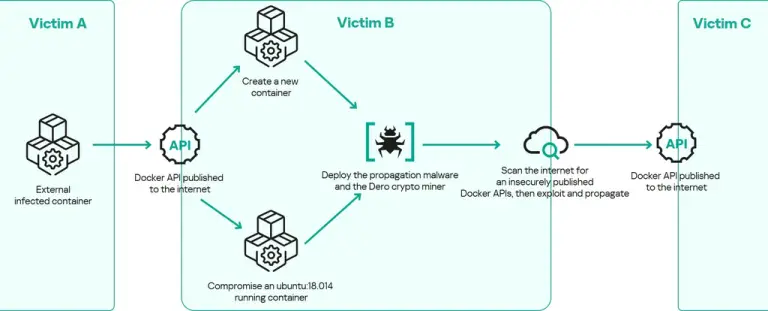
A new malicious campaign targeting containerized infrastructures is spreading rapidly across the globe, transforming compromised containers into...
The legendary Japanese film studio Toho, recently honored with an Academy Award for visual effects in Godzilla...
Subscribers of Cellcom—a telecommunications provider serving users across Wisconsin and Michigan’s Upper Peninsula—were left without service for...
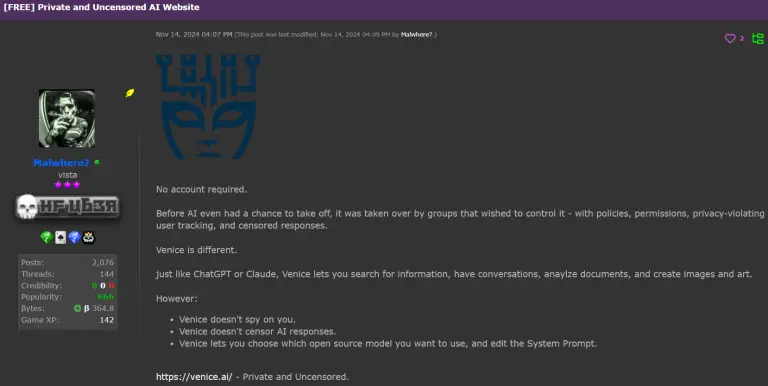
An unusual chatbot named Venice.ai is rapidly gaining traction within hacking communities, operating without any ethical constraints....
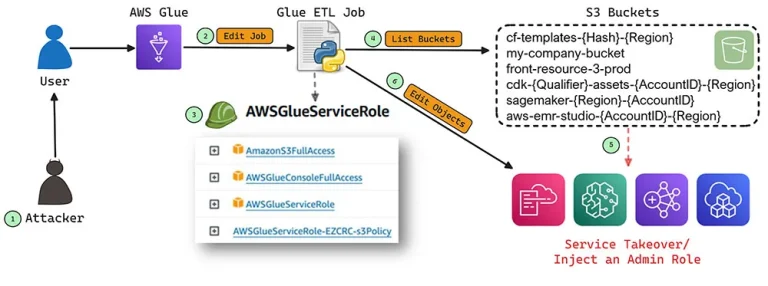
Experts have uncovered significant risks linked to default access policies within Amazon Web Services’ cloud infrastructure. These...
A critical vulnerability has been discovered in Samlify, a library designed to integrate SAML authentication into Node.js...
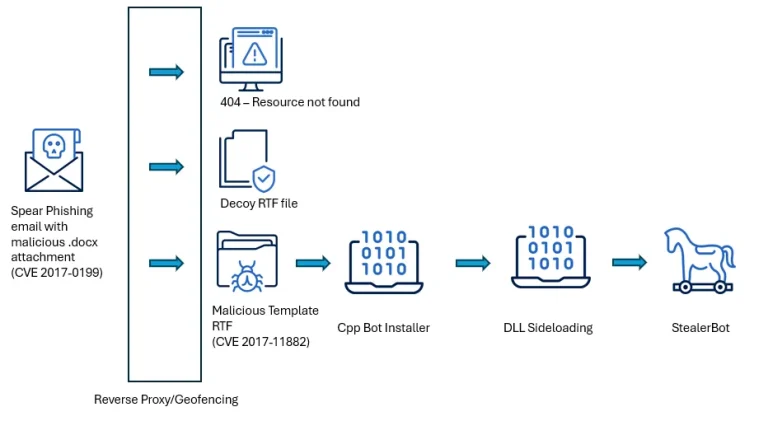
The SideWinder group has launched a new cyber-espionage campaign targeting government institutions across South Asia, striking agencies...
On May 19, 2025, version 3.1.0 of the APT toolkit—a core component of the package management system...
Several ransomware groups have begun actively deploying a strain of malware known as Skitnet during the post-exploitation...
At the BUILD 2025 conference, Microsoft announced the integration of post-quantum cryptography (PQC) into Windows Insider preview...
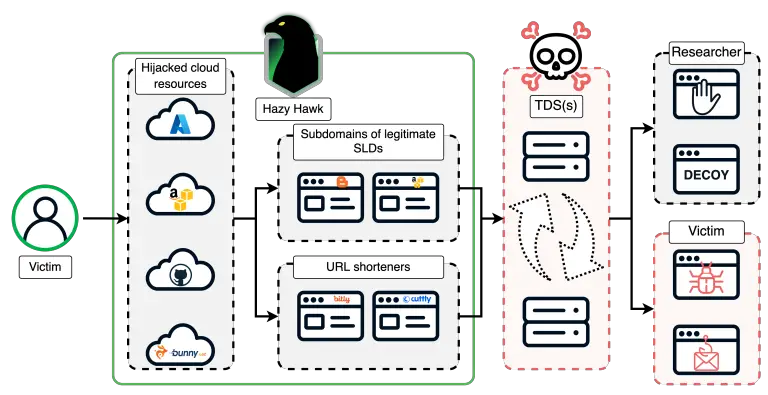
A threat actor known as Hazy Hawk has launched a widespread campaign to seize abandoned cloud assets...
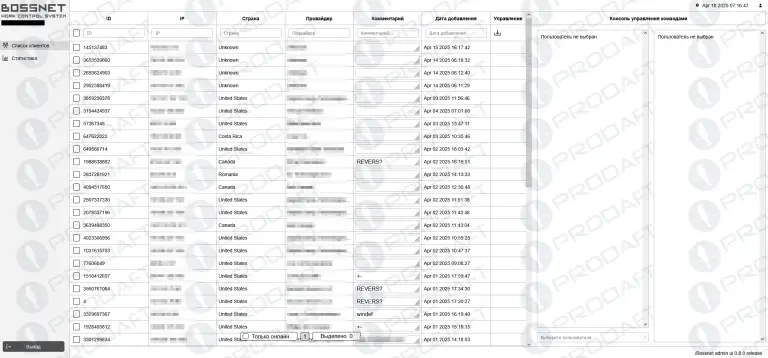
Amid a surge in attacks targeting exposed internet-facing services, cybersecurity experts have identified a new malicious campaign...
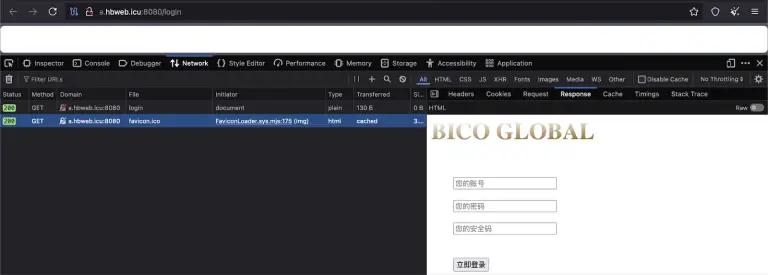
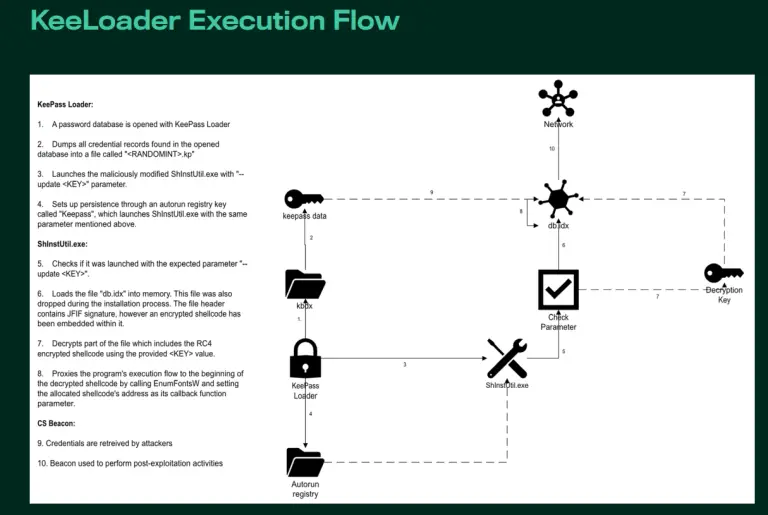
For over eight months, a cybercriminal group has been distributing trojanized versions of the KeePass password manager,...