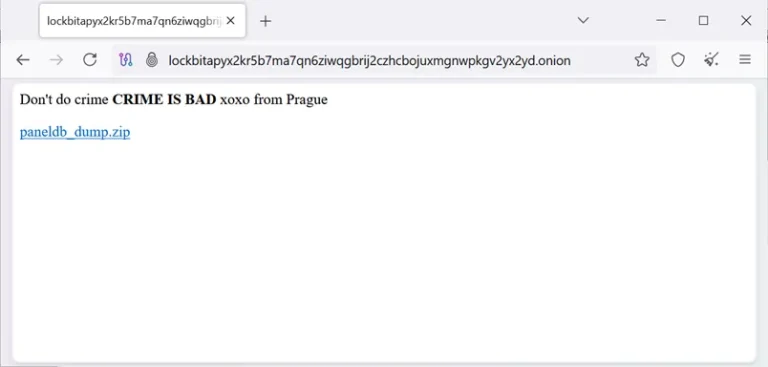
The LockBit ransomware syndicate has found itself at the center of a dramatic incident after its darknet...
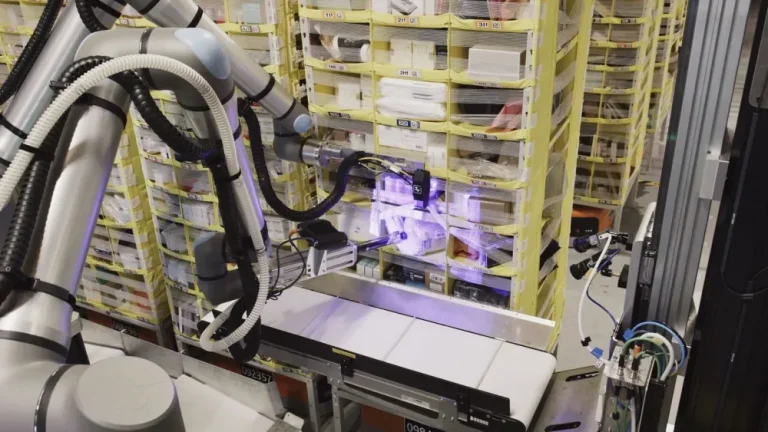
Amazon has announced that it has now deployed over 750,000 robots across its fulfillment centers and has...
Recent FCC certification documents have revealed what appears to be a new handheld gaming device developed by...
AMD has released its financial results for the first quarter of fiscal year 2025, reporting revenue of...
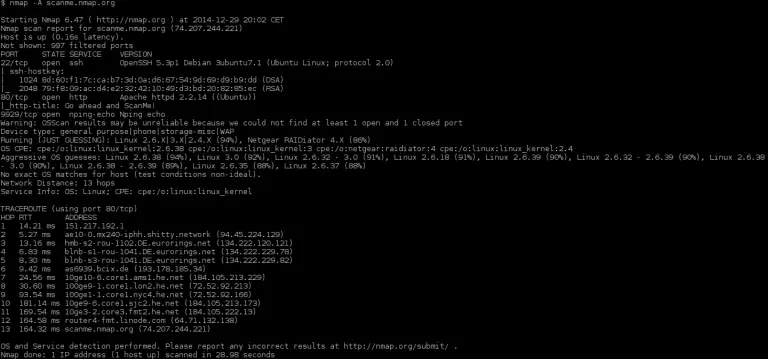
A new release—Nmap 7.96—has been unveiled, marking the latest iteration of one of the most renowned tools...
A recent data breach has unveiled an alarming degree of negligence toward digital security on the part...
A major Chinese cybercriminal syndicate has launched a sweeping SMS phishing campaign targeting millions of users worldwide....
Following the April 2025 security updates, administrators of Windows Server Update Services (WSUS) began encountering widespread issues...
Recently introduced alongside the GeForce RTX 5060 Ti, the GeForce RTX 5060 has now been officially announced...
Earlier this year, alongside the unveiling of the Galaxy S25 series, Samsung introduced a preview of its...
According to an inadvertently released update on Google’s official blog, the company is poised to unveil a...
Harman International, a wholly owned subsidiary of Samsung, has recently announced its acquisition of Sound United—Masimo’s consumer...
The legal battle between Meta and the Israeli firm NSO Group has culminated in a devastating verdict...
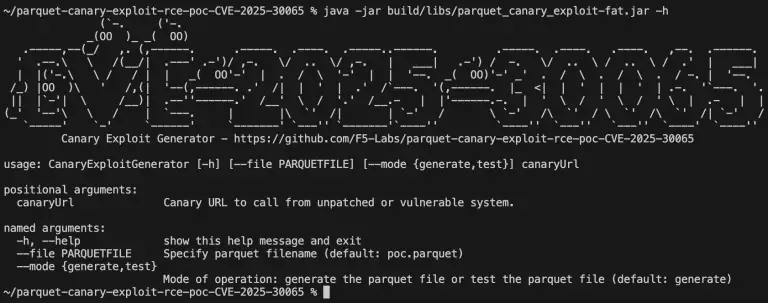
A vulnerability in Apache Parquet, designated as CVE-2025-30065 and carrying the maximum CVSS score of 10.0, has...