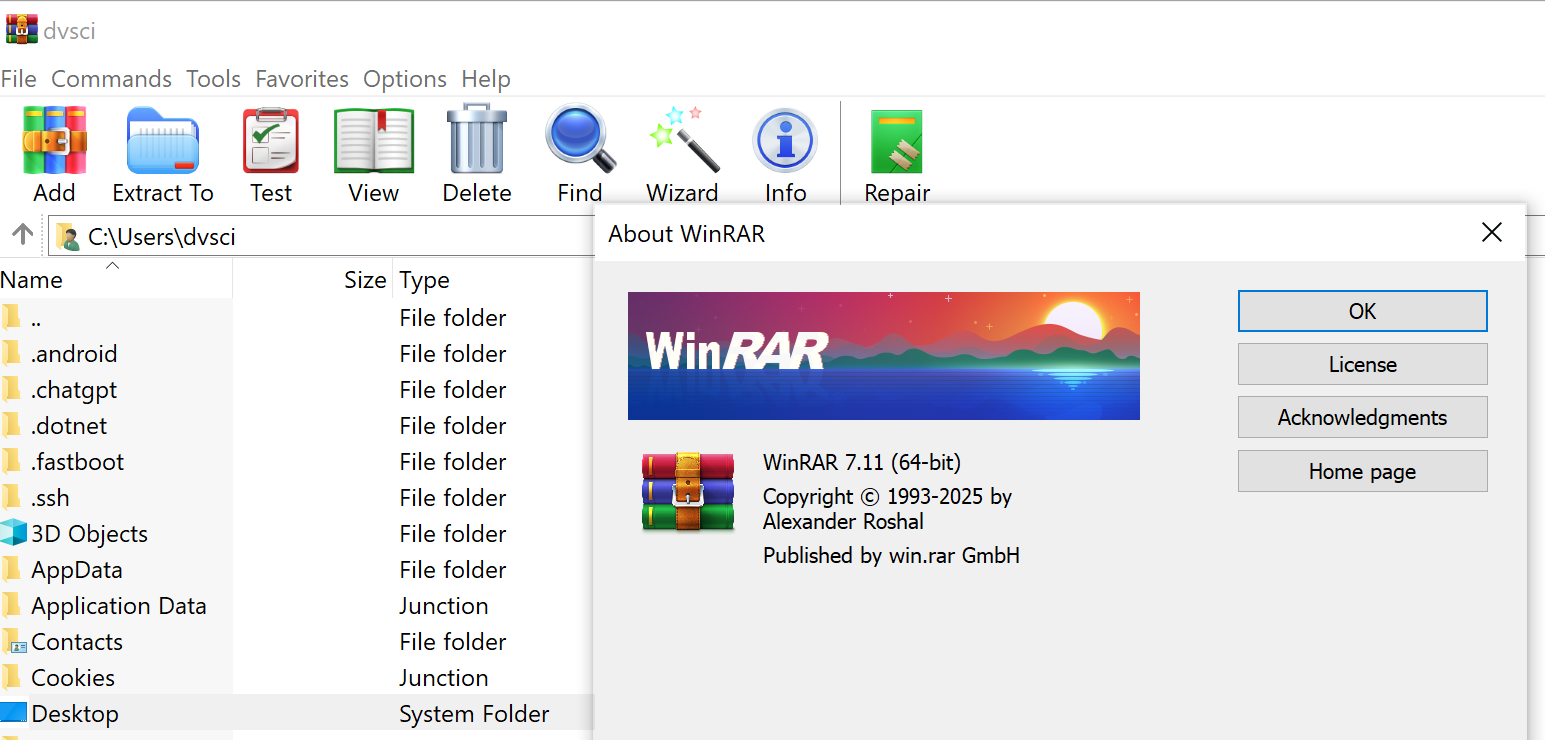
A vulnerability has been discovered in the WinRAR archiving utility that allows the circumvention of Windows’ “Mark of the Web” (MotW) security mechanism, potentially leading to the execution of malicious code. The issue was disclosed by the JPCERT/CC Coordination Center following an analysis conducted by Mitsui Bussan Secure Directions.
The flaw affects all versions of WinRAR prior to 7.11. At the core of the vulnerability lies a loophole wherein the opening of a symbolic link to an executable file would bypass Windows’ standard warning about launching files downloaded from the internet. Under normal circumstances, Windows flags such files with metadata indicating their untrusted origin, triggering a user-facing security prompt. However, when accessed via a symbolic link, this safeguard was effectively nullified, allowing malware to run silently.
Although creating symbolic links generally requires administrative privileges, the vulnerability poses a real risk in scenarios where an attacker has already obtained limited system access or can manipulate the archive contents before extraction. For instance, a specially crafted archive could be leveraged in a social engineering attack, enticing the user to open what appears to be a harmless file.
According to JPCERT/CC, the flaw has been assigned the identifier CVE-2025-31334 and received a CVSS score of 6.8. This rating reflects the need for specific preconditions—namely, user interaction in opening the archive—but also acknowledges the potentially severe consequences: full system compromise, data tampering, or denial of service (DoS).
The vulnerability has been patched by RARLAB, the developer of WinRAR, which urges all users to update to version 7.11 or later. In addition, users are advised to scan archives with antivirus software prior to opening and to exercise caution with files received via email or downloaded from the web.
Notably, version 7.10 of WinRAR, released in February, introduced various enhancements in performance, interface design, and security. Among the most significant updates was the ability to limit the retention of Mark-of-the-Web metadata. Now, the archiver can preserve only the zone identifier, omitting more sensitive details such as the originating URL or IP address. This change reduces the risk of information leakage during file transfer while maintaining Windows’ protective measures.