For six years, General Paul Nakasone held dual command over two of the United States’ most critical agencies: the National Security Agency (NSA) and U.S. Cyber Command. Following his departure, Nakasone adopted a more candid tone—in a recent interview, he openly expressed that his greatest concern lies with China’s intensifying cyber aggression. In his view, China distinctly outpaces all other nations in cyber capabilities.
What was once discussed as a hypothetical threat has now manifested in reality—malicious code is being discovered embedded within critical infrastructure, from telecommunications providers to the power grids of small towns. He cited an example from Massachusetts, where Chinese malware was found within a municipal utility system. According to Nakasone, such instances are likely far more common than reported—many have simply yet to be uncovered.
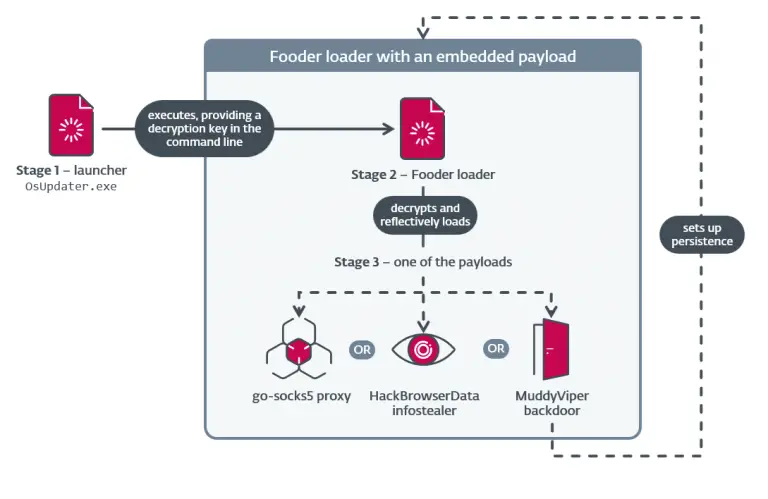
One group in particular, Volt Typhoon, diverges from conventional cyber-espionage operations. Rather than collecting intelligence, the group implants malicious code in systems that offer little strategic data. Their intent is not surveillance, but sabotage—laying the groundwork for large-scale disruption should tensions with China escalate into crisis, such as over Taiwan. It is, in essence, a latent threat, engineered to be activated at a decisive moment.
Another group, Salt Typhoon, has targeted telecommunications networks in efforts to surveil select individuals and institutions, including political figures and entities like the Department of Justice and the FBI. Nakasone points to this as a clear illustration of artificial intelligence being deployed in modern espionage—where adversaries combine data harvesting with analysis powered by large language models to refine targeting and behavioral insights.
He further noted that the methods of cyber operations are increasingly converging with those of physical warfare. In today’s conflicts, lines of code can trigger real-world explosions. As the Internet of Things (IoT) rapidly expands, cyberweapons are growing in their tangible, destructive consequences.
Nakasone voiced particular concern over the reckless integration of AI within government systems. He criticized the deployment of algorithms into federal networks without proper oversight, calling it a direct threat to national security. One case under review involves AI tools implemented by personnel from the Department of Energy (DOGE), highlighting how bypassing security protocols in the name of automation may inadvertently open critical vulnerabilities to hostile exploitation.
On the subject of China’s AI model, DeepSeek, the general was unequivocal—it is cause for serious alarm. These models are capable of responding to dangerous queries, and user data may be misappropriated for malign purposes. He emphasized that the United States must be vocal about these risks and must avoid endorsing technologies that compromise safety.
Crucially, Nakasone underscored that the U.S. has yet to define its strategic posture regarding AI—whether to employ it primarily for offensive or defensive purposes. Though he initially believed that the offensive applications would confer greater advantage, he now acknowledges that AI-enabled defense could prove even more formidable. Still, he warns, adversaries are increasingly willing to remove humans from critical decision-making loops—while the United States continues to insist on human oversight for all pivotal operations.
In closing, Nakasone called for the urgent development of a comprehensive AI strategy—one that encompasses data stewardship, energy efficiency, semiconductor manufacturing, and talent acquisition. Only through such an integrated vision, he believes, can the United States maintain both its leadership and security in the digital age.