Ivanti has released security updates to address a critical remote code execution (RCE) vulnerability affecting its Connect Secure gateways.
The flaw, tracked as CVE-2025-22457 and carrying a CVSS score of 9.0, has already been exploited in cyber-espionage operations as early as mid-March 2025. According to reports from Google and Mandiant, the attacks have been attributed to the Chinese threat group UNC5221, which previously leveraged zero-day vulnerabilities in Ivanti devices.
The vulnerability stems from a buffer overflow in the stack and affects legacy versions of Pulse Connect Secure 9.1x, Ivanti Connect Secure up to version 22.7R2.6 inclusive, Policy Secure, and Neurons for ZTA gateways. Initially classified as a non-critical defect, the bug was later revealed to allow remote code execution via complex, unauthenticated attack vectors requiring no user interaction.
A patch addressing the issue was included in version 22.7R2.6, released on February 11, 2025. At the time, the vulnerability was not considered dangerous due to character limitations in the buffer that were believed to preclude exploitability. It was only after subsequent analysis that Ivanti confirmed the flaw could, under certain conditions, be exploited — a conclusion supported by observed incidents in the wild.
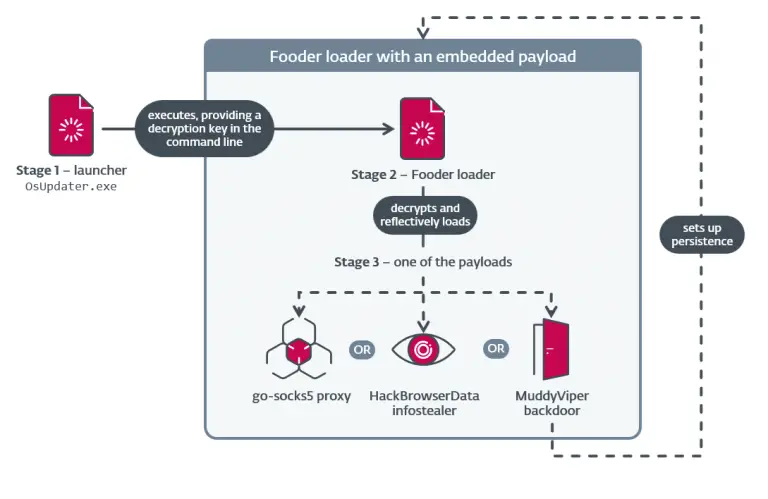
UNC5221 has been actively targeting edge device vulnerabilities since 2023. In this campaign, the threat actors deployed a suite of custom malware, including the memory-resident dropper TRAILBLAZE, the passive backdoor BRUSHFIRE, and an updated iteration of SPAWN — a comprehensive intrusion toolkit.
Experts believe that the attackers reverse-engineered the patch in ICS 22.7R2.6 and, through advanced analysis, discovered that versions 22.7R2.5 and earlier were vulnerable to RCE.
At present, Policy Secure and ZTA gateways have not been targeted, although they remain susceptible to the flaw. Ivanti has scheduled updates for these products on April 19 and April 21, respectively, noting that architectural safeguards mitigate the associated risks in these systems.
Ivanti strongly urges users of affected devices to update to version 22.7R2.6 without delay. It also recommends employing external forensic tools to detect potential indicators of compromise. If evidence of exploitation is found, users should perform a factory reset and redeploy the device with the latest secure firmware.