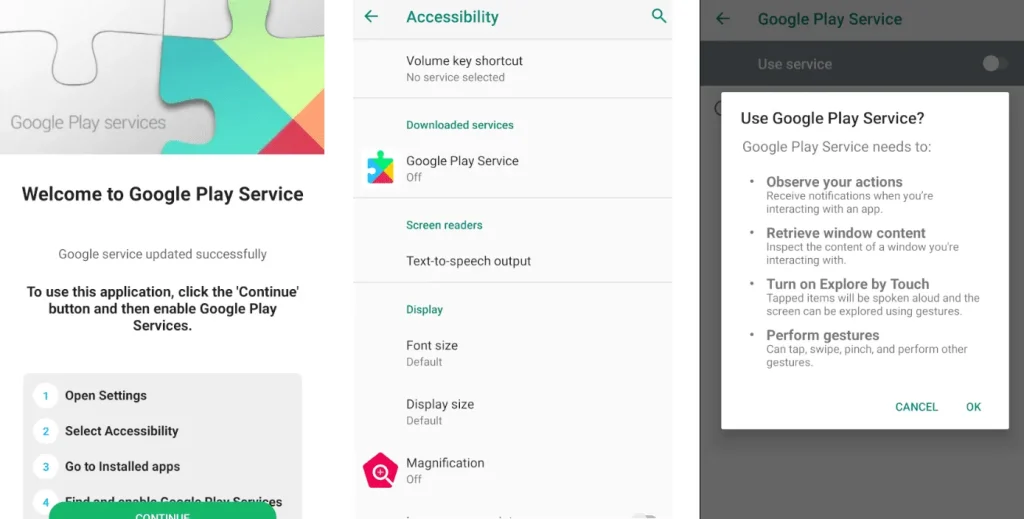
Malware prompting victims to enable Accessibility services
Mobile threats continue to evolve, and a formidable new banking trojan named TsarBot has emerged, targeting Android devices. Researchers at Cyble uncovered its deployment in a sophisticated attack chain affecting more than 750 mobile applications across sectors such as online banking, finance, cryptocurrency, and e-commerce.
The core technique employed by TsarBot is the overlay of counterfeit login screens atop legitimate applications. This enables the seamless theft of usernames, passwords, payment card credentials, and other sensitive information. Disguised as Google Play Services, the trojan is installed via a malicious dropper downloaded from phishing websites designed to mimic trusted financial platforms.
Its distribution spans North America, Europe, Asia, and the Middle East, underscoring the global scope of the campaign. Once activated, the malware displays fraudulent login interfaces, tricking users into believing they are interacting with genuine apps while their data is instantly exfiltrated to a remote command-and-control (C2) server.
TsarBot’s capabilities extend well beyond traditional phishing. It can remotely control infected devices, record the screen, simulate user actions such as swipes and taps, and mask its operations with a black screen. The trojan also employs lock screen overlays to harvest PINs and passwords.
Communication with the C2 server occurs via WebSocket connections over multiple ports, enabling not only real-time data transmission but also live command execution. The server can instruct the trojan to manipulate the user interface, perform gesture-based inputs, and interact with installed apps.
The list of targeted applications is dynamically updated: TsarBot fetches package names from its server, targeting banking apps from countries such as India, France, Poland, and Australia, as well as cryptocurrency wallets and social media platforms. Upon detecting a launch, it overlays a visually indistinguishable fake login screen to capture the user’s credentials.
A particularly alarming aspect of TsarBot is its abuse of Android’s Accessibility Services to gain elevated privileges. This allows it to operate stealthily, executing fraudulent actions while bypassing standard security measures.
The emergence of TsarBot mirrors the tactics of Crocodilus, another banking trojan reported earlier today. While primarily affecting users in Spain and Turkey, Crocodilus also utilizes fake overlays to capture login credentials and further possesses the ability to record screens and take screenshots—even within protected apps.
In light of these threats, cybersecurity experts strongly advise downloading apps only from official sources, avoiding suspicious links, enabling Google Play Protect, and regularly applying security updates. These measures can significantly reduce the risk of infection by such sophisticated mobile malware.
The appearance of TsarBot and Crocodilus reflects the increasing technical sophistication of mobile threats and underscores the urgent need for heightened vigilance in safeguarding personal data in the mobile ecosystem.