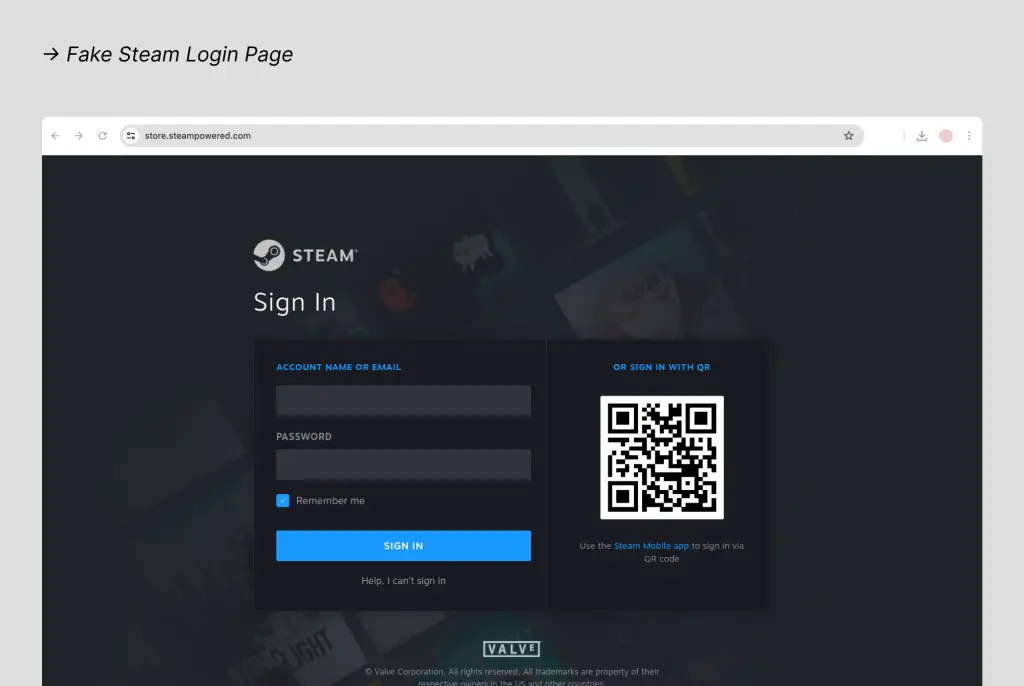
In the first quarter of 2025, the gaming platform Steam unexpectedly topped the list of the most frequently impersonated brands by phishing actors. This revelation comes from Guardio, a cybersecurity firm, following an analysis of millions of messages received by its clients. According to the report, Steam surpassed traditionally impersonated companies such as Microsoft and Meta.
Cybercriminals have been exploiting the Steam brand to distribute deceptive alerts regarding alleged account issues, such as failed payments or suspicious login activity. The objective of these messages is to lure users into clicking on malicious links and entering their credentials on counterfeit websites, where the information is immediately harvested by attackers.
Beyond security threat alerts, scammers also employ alternate narratives. Some emails claim the recipient has won a Steam gift card or gained access to exclusive promotions, compelling them to follow harmful links in pursuit of the promised “reward.” These schemes prey on the public’s trust in well-known brands and their tendency to react swiftly to urgent-sounding notifications.
An unusual trend highlighted by Guardio is the debut of U.S. toll road operators among the top ten most impersonated brands. Companies like EZDrive Massachusetts, E-ZPass, and SunPass—serving various regions—have seen a staggering 604% increase in fraudulent message volume since the beginning of the year, with the sharpest spike occurring in the first week of March.
The tactic is simple: victims receive an SMS claiming an unpaid toll fee, including a link to a fraudulent website mimicking the official payment portal. The aim is to harvest payment details by exploiting the victim’s fear of penalties and the urgency of the message. Analysts note that this manufactured sense of immediacy significantly enhances the effectiveness of the scam.
Other frequently spoofed brands making the top ten include Roblox, the United States Postal Service (USPS), streaming giant Netflix, and file-sharing platform WeTransfer. Their widespread familiarity among U.S. users renders them ideal bait for phishing schemes, as messages appearing under these names are less likely to raise suspicion.
There has also been a surge in phishing messages masquerading as communications from the Internal Revenue Service (IRS), as well as from retail brands Joann and Forever 21. Notably, the latter announced the closure of several stores earlier this year—an event promptly exploited by scammers who circulated bogus “final clearance” deals, redirecting victims to fraudulent websites designed to steal their data.
According to Guardio, cybercriminals are increasingly tailoring their campaigns to align with current events and user behavior. The more topical the event or headline, the greater the likelihood of a successful attack. Consequently, seasonal trends, high-profile store closures, and tax season become fertile ground for waves of deceptive messages.
Security experts reiterate a crucial rule: any sudden message concerning payments, prizes, or account suspensions should immediately raise suspicion. Such claims should only be verified through official websites or applications. Even the most trusted brands are not immune to having their names weaponized by malicious actors.