Researchers have uncovered a growing threat stemming from the Proton66 network — a hosting platform offering so-called “bulletproof” services increasingly favored by novice cybercriminals for disseminating malware and supporting other illicit ventures. At the heart of this investigation lies a previously unknown actor operating under the alias Coquettte, allegedly affiliated with the hacker group Horrid.
The investigation was triggered by the discovery of the website cybersecureprotect[.]com, which masqueraded as a legitimate antivirus product. In reality, it formed part of a broader infrastructure distributing malicious software. A critical operational security (OPSEC) lapse left the site’s directory structure exposed, granting researchers full access to its internal framework — including droppers and executable malware files.
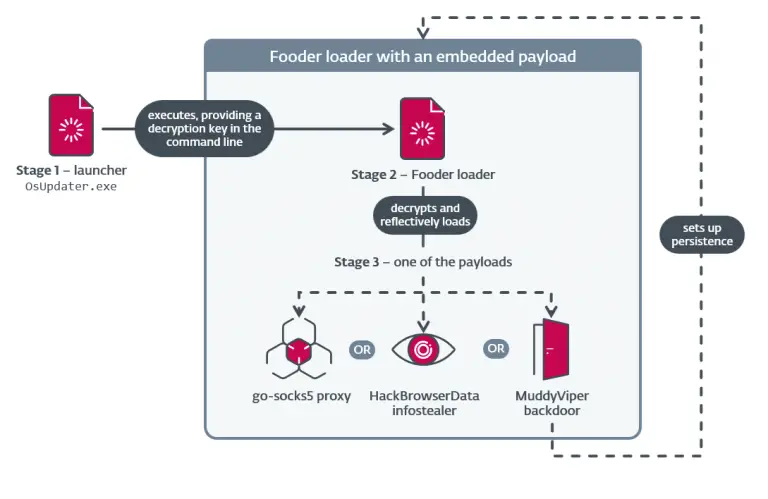
Among the findings was a ZIP archive titled CyberSecure Pro.zip, containing an installer named CyberSecurePro.msi. Upon execution, the installer connected to URLs cia[.]tf and quitarlosi[.], subsequently downloading the second stage of the malware. This payload was identified as Rugmi (also known as Penguish), a modular loader tailored for delivering infostealers, trojans, and other malicious payloads.
Proton66 serves as a nexus for a range of malicious operations, including phishing websites impersonating prominent brands, banking platforms, and cryptocurrency exchanges. Most of these sites are designed to harvest credentials or distribute malware. Notably, their operators exhibit poor technical acumen — from unprotected directories to predictable domain patterns and default configurations.
The figure of Coquettte stood out in particular. According to data from coquettte[.]com, the individual presents as an 18-year-old developer currently studying programming. The site linked to multiple projects and personal profiles, including GitHub, YouTube, and even a Last.fm account under the alias chickenwing_11. This visible digital footprint, coupled with repeated OPSEC failures, underscores the youth and inexperience of the actor.
Investigators confirmed that the domain cia[.]tf — functioning as a command-and-control (C2) server — was registered using the email root[@]coquettte[.]com, conclusively linking it to Coquettte. Further analysis revealed several related assets:
- meth[.]to and meth[.]su — sites offering guides on producing narcotics, explosives, and methods for catalytic converter theft;
- terrorist[.]ovh — another domain utilizing the same infrastructure;
- horrid[.]xyz — a website believed to be affiliated with the Horrid hacking group, of which Coquettte is possibly a member.
Common analytics tags (e.g., Google Analytics ID G-RPK032CCFZ), consistent design elements, and cross-linking among sites suggest a unified origin. This implies the existence not of a lone operator, but rather a small collective or community, each member contributing to a shared illicit enterprise.
Projects listed in the other_projects.txt file on Coquettte’s site include:
- meth[.]to — a dark guide to chemistry and explosive materials;
- cia[.]tf — the aforementioned malware C2 server;
- xn--xuu[.]ws — a terminal-style site based on the mercurywork.shop codebase.
Together, these elements form an onboarding ramp into cybercrime for aspiring threat actors: tools, infrastructure, trojans, and even “training materials” are readily accessible with minimal technical barriers.
Even those with limited skills can now orchestrate fully-fledged malicious campaigns, posing a serious threat to both corporate and personal environments. Vigilant monitoring of such infrastructure and prompt response to indicators of compromise remain critical pillars of modern cybersecurity defense.