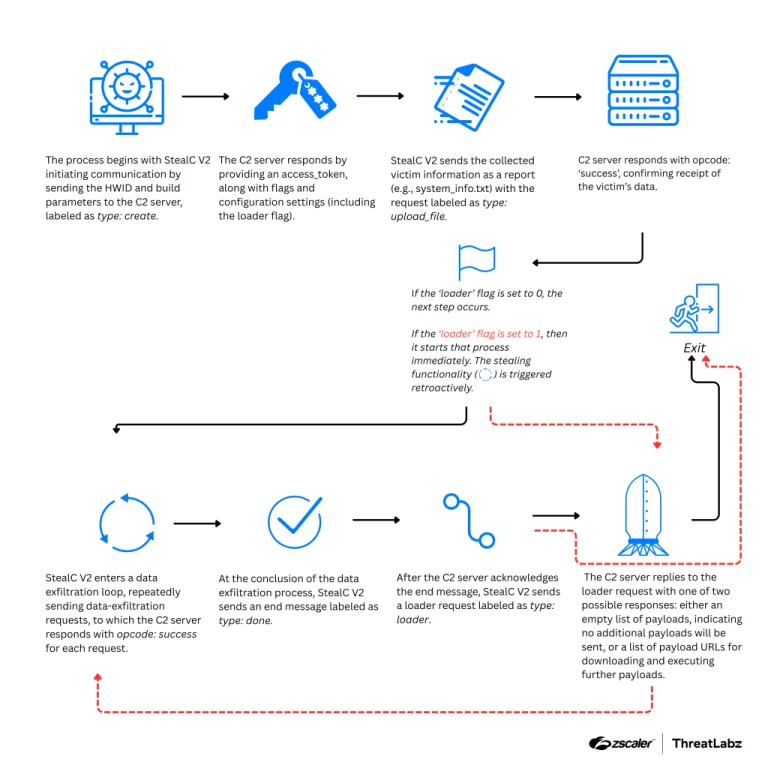
The widely used StealC malware, actively deployed in cyberattacks for data theft and the delivery of secondary...
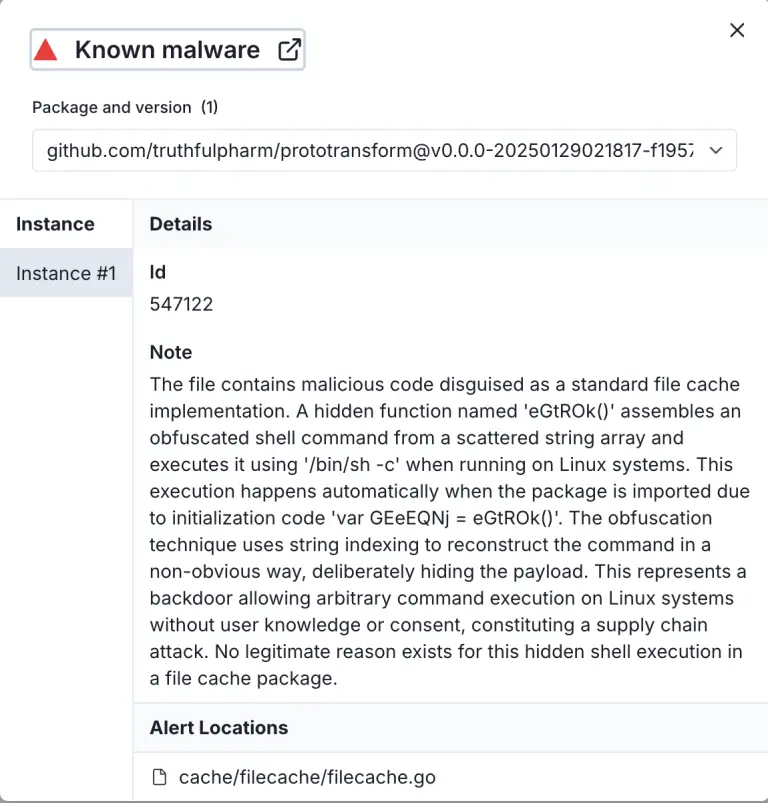
Three malicious components have been discovered within the Go programming module ecosystem, capable of triggering complete data...
The Open Source Lab at Oregon State University (OSU OSL), a vital technical cornerstone for open-source projects...
An AMD engineer continues to advance processor security within Linux by proposing a novel protection management system...
The United States Department of Justice is demanding that Google divest key components of its advertising business...
Apple has begun testing a new programming platform that harnesses artificial intelligence to write, edit, and review...
Engineers at ByteDance have introduced an innovative approach to accelerating inter-process communication (IPC) in Linux, dubbed RPAL—Run...
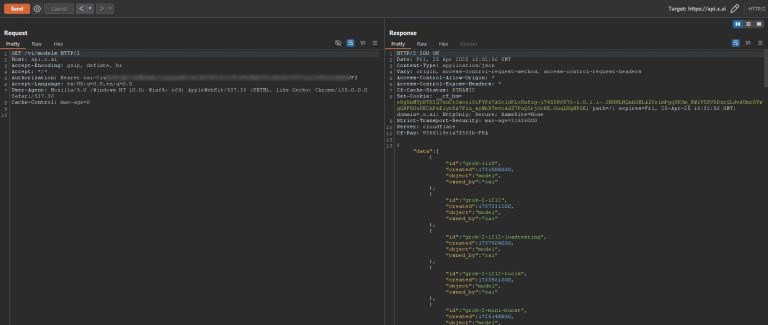
An employee of xAI inadvertently published a private API key on GitHub, which, for two months, granted...
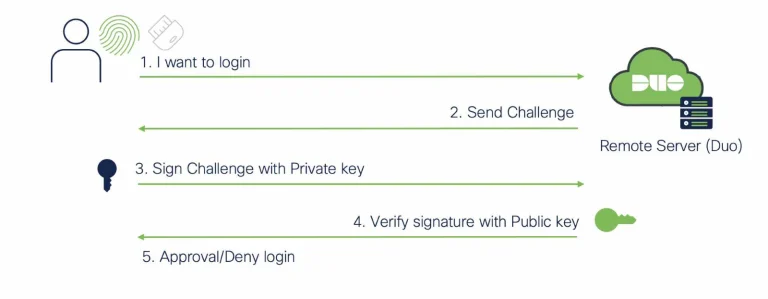
Despite the widespread adoption of multi-factor authentication (MFA), cybercriminals have developed increasingly sophisticated techniques to circumvent it....
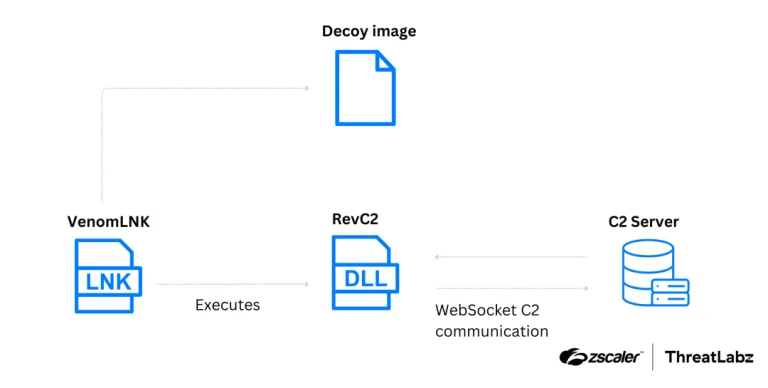
Researchers at Insikt Group have uncovered two new digital tools circulating online, both designed to steal passwords...
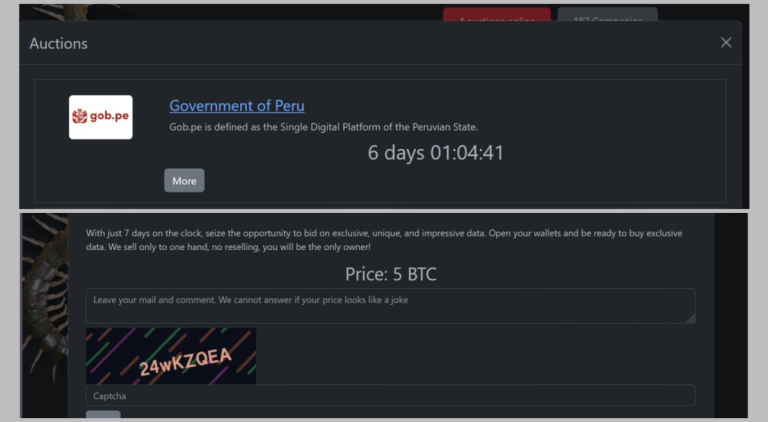
Government systems in Peru have been paralyzed following a large-scale cyberattack claimed by the hacker collective Rhysida,...
Rockstar Games has officially announced that the highly anticipated Grand Theft Auto VI, originally slated for release...
Qualcomm has released its financial results for the second quarter of fiscal year 2025, reporting revenue of...
Redis, the company behind the eponymous and widely acclaimed database, has announced its return to an open-source...
Apple has begun issuing alerts regarding targeted attacks involving spyware allegedly procured by state-affiliated entities. According to...