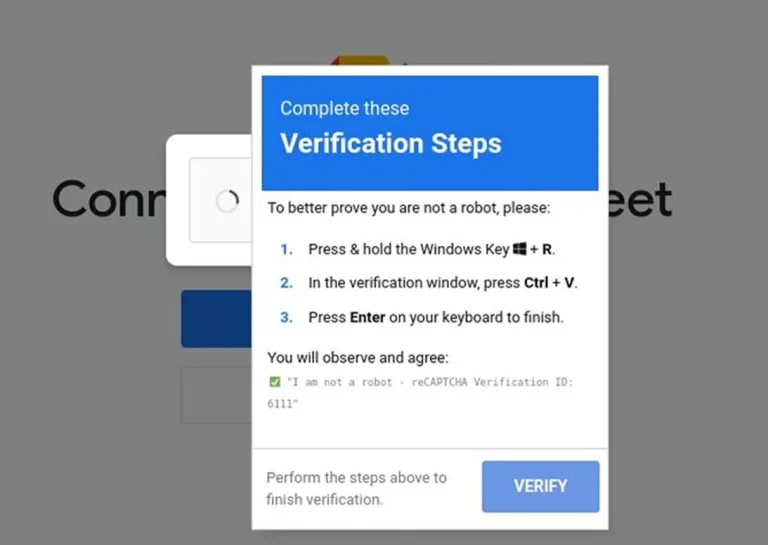
An unusual social engineering attack was recently discovered on the website of iClicker, a widely used educational...
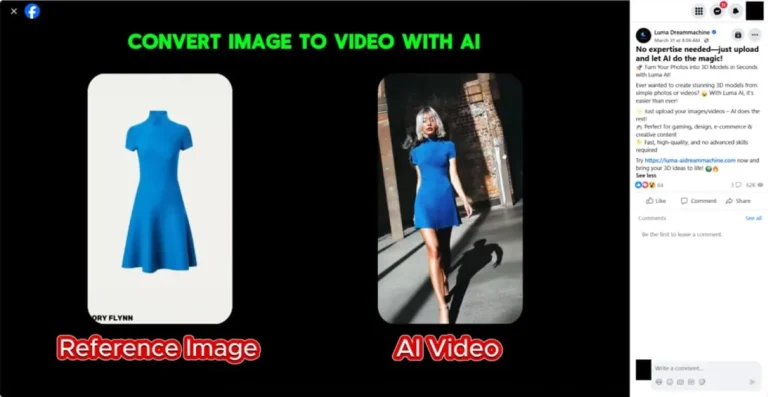
Fake AI-powered video generation platforms have emerged as a new front for disseminating a dangerous malware strain...
Law enforcement authorities have dismantled a botnet that, for over two decades, had infected thousands of routers...
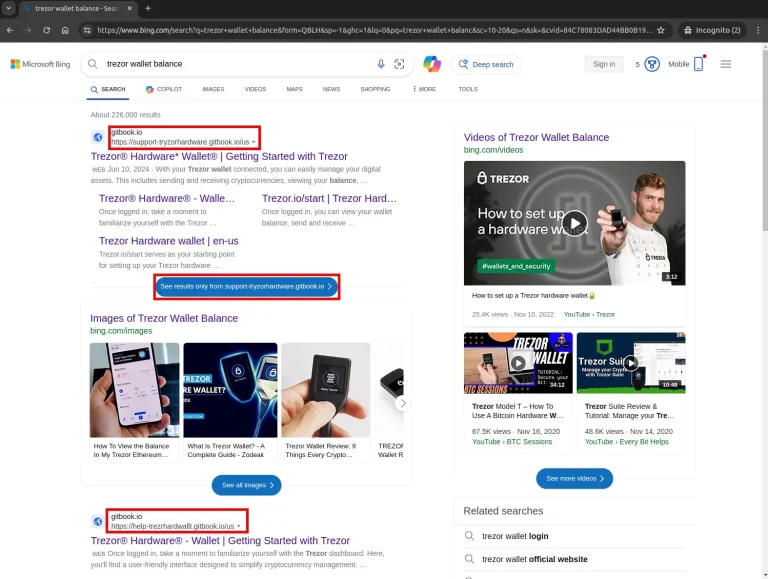
Cybersecurity researchers have uncovered a large-scale, meticulously orchestrated phishing campaign aimed at cryptocurrency theft. Over the span...
SonicWall has addressed three critical vulnerabilities in its Secure Mobile Access (SMA) 100 series devices, flaws that...
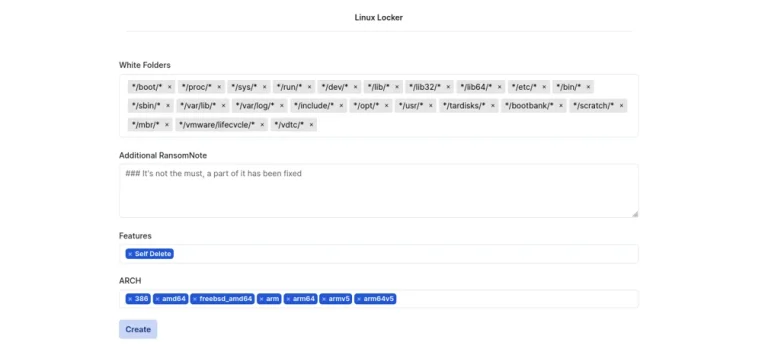
The Qilin group, also known by the alias Agenda, emerged as the most active ransomware operator in...
Since late April 2025, there has been a surge in attacks targeting SAP NetWeaver Visual Composer, exploiting...
According to a report by Bloomberg journalist Mark Gurman, Apple is developing a new processor specifically designed...
Insight Partners, one of the world’s largest venture capital firms with over $90 billion in assets under...
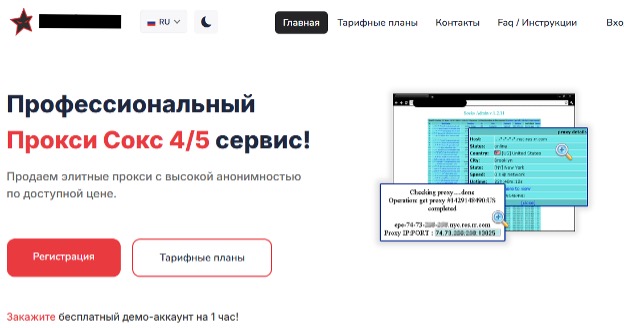
Obsolete routers are once again under siege — cybercriminals are transforming outdated devices into covert proxy nodes,...
Ubuntu 25.10, scheduled for release on October 9, 2025, will mark a historic milestone as the first...
Somewhere deep within the recesses of Windows, a relic of the early 1990s still endures — a...
Cisco has issued an urgent security update to address a critical vulnerability in wireless controllers running IOS...
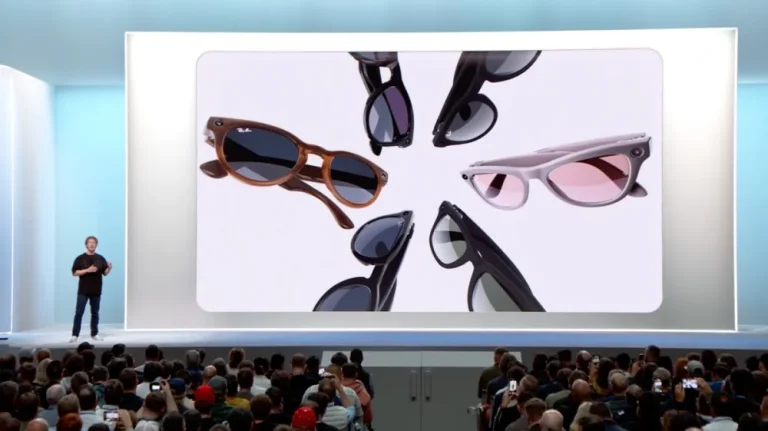
According to a report by The Information, Meta initially intended to equip its smart glasses with facial...
The U.S. Federal Trade Commission (FTC) previously filed multiple appeals against Microsoft’s acquisition of Activision Blizzard, citing...