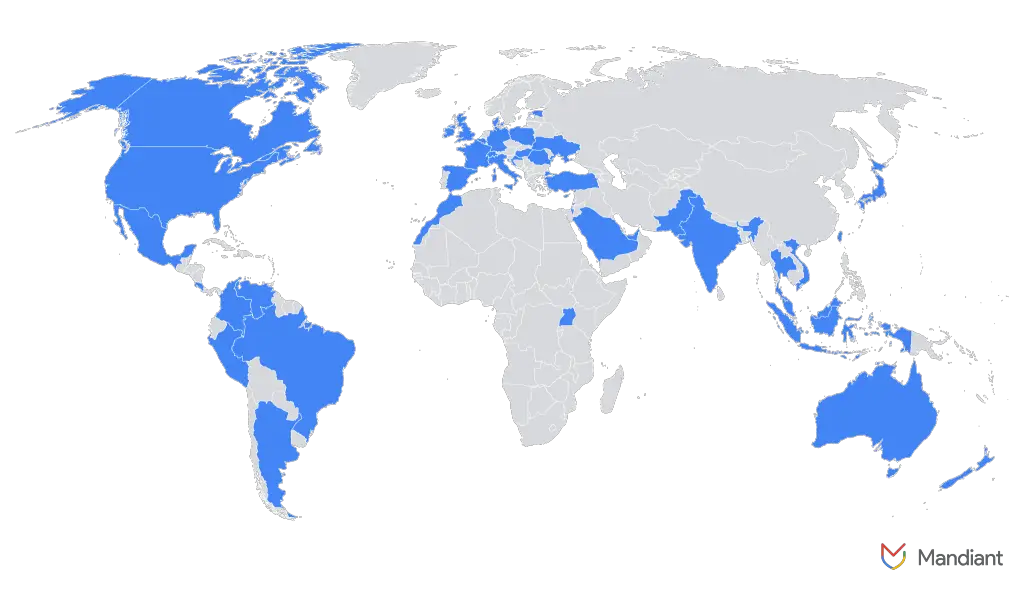
North Korean IT operatives have increasingly infiltrated European companies under the guise of remote employees. According to Google’s Threat Intelligence Group, actors from the DPRK have ramped up activity in countries such as Germany, Portugal, Serbia, Slovakia, and others, relying on forged résumés, counterfeit passports, and AI-generated photographs to pass job interviews undetected.
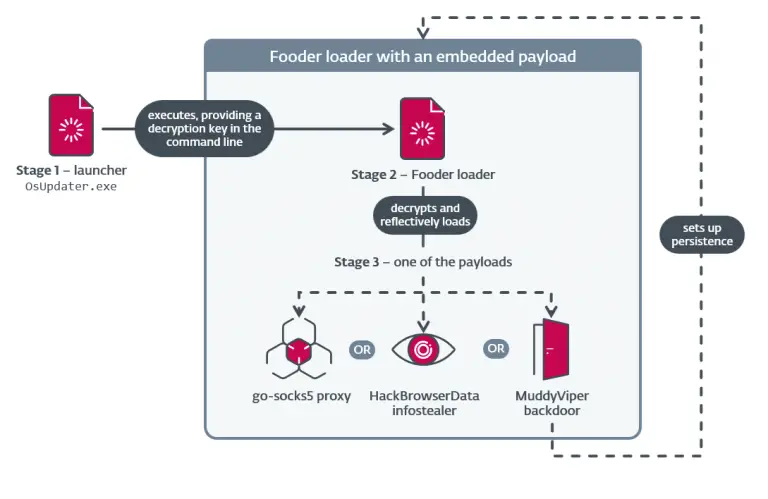
Their primary objective is to secure employment in the tech sector and funnel earnings directly into Pyongyang’s coffers. However, their operations often extend beyond payroll diversion. Some embed malware into corporate systems, exfiltrate sensitive data, or extort organizations for financial gain. Investigations have also revealed cases where such operatives simultaneously work for multiple companies, drawing several salaries at once—while underperforming in their duties.
To conceal their true origins, these individuals frequently employ tactics such as the “broken webcam” excuse, VPN obfuscation, and the assistance of local intermediaries. These collaborators receive company-issued laptops, keep them connected to the internet, and help launder the proceeds through cryptocurrency or services like Payoneer and TransferWise. This setup is known as a “laptop farm.” In one instance, a device designated for use in the U.S. was found active in London, pointing to a sophisticated logistical infrastructure.
The investigation uncovered detailed guides for infiltrating European job markets, including instructions on altering time zones and acquiring fictitious national identities. Fabricated biographies featured degrees from the purported University of Belgrade and residential addresses in Slovakia. Access credentials for recruitment sites and HR platforms were also discovered.
Google researchers note an uptick in targeting of companies that follow BYOD (Bring Your Own Device) policies. These environments, which allow employees to use personal devices not governed by corporate security controls, eliminate the need to ship hardware—thus reducing the chance of exposure through address verification.
As international scrutiny and enforcement actions intensify in the United States, North Korean IT operatives are shifting their operations toward Europe, where awareness of such tactics remains comparatively low. Some have resorted to blackmail following termination, threatening to leak proprietary information or sell it to competitors. Breach reports reference source code and confidential internal projects.
Federal agencies advise heightened vigilance for red flags, such as refusal to appear on video calls, frequent changes to payment information, absent profile photos, and discrepancies in listed addresses. Detecting these abuses is becoming increasingly challenging, as the sophistication of threat actors grows—and their targets more frequently include major technology firms.