Cybercriminals have begun exploiting Microsoft’s Trusted Signing service to digitally sign malicious software, making it appear secure and issued by reputable companies. This tactic allows them to bypass antivirus solutions and other security systems that inherently place greater trust in signed files.
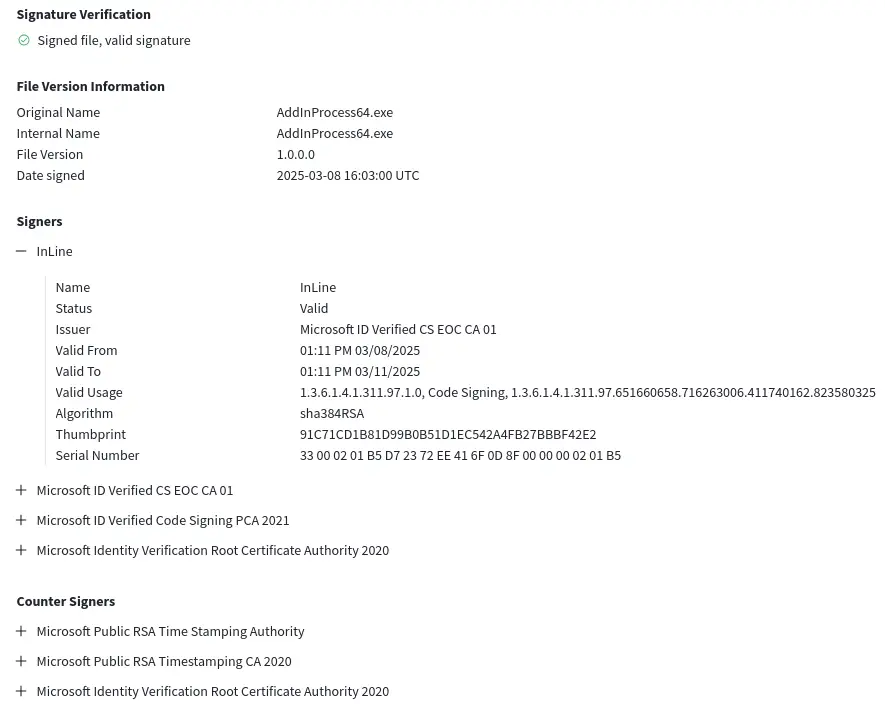
Trusted Signing is a cloud-based service launched by Microsoft in 2024. It enables developers to quickly sign their applications using short-lived certificates valid for only three days. Files signed through this mechanism are granted baseline trust by Windows and SmartScreen, helping them evade warning prompts during execution.
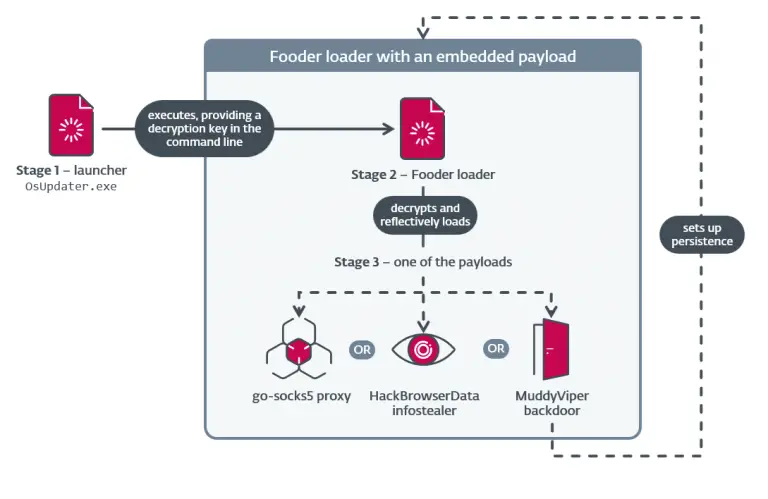
Threat actors are leveraging this service to sign malware and distribute it as though it were legitimate software. Researchers have uncovered several such instances, including malware linked to campaigns like Crazy Evil Traffers and Lumma Stealer. The malicious files bore certificates issued by Microsoft’s certificate authority.
Although these certificates are valid for just three days, the files they sign remain trusted by the system unless the certificate is explicitly revoked. This window provides ample time for attackers to disseminate malicious payloads and compromise systems.
Trusted Signing offers developers a convenient and cost-effective means to sign their products—a subscription costs $9.99 per month. Notably, certificates are not issued directly to users but are generated and managed through Microsoft’s infrastructure, theoretically reducing the risk of key compromise. However, this very architecture enables rapid signing of malicious files, particularly when an account is registered under an individual’s name—a process significantly easier than establishing a corporate identity.
Traditionally, attackers have sought Extended Validation (EV) certificates, which offer a higher level of trust and more easily circumvent security mechanisms. However, acquiring EV certificates is far more complex—it often requires stealing one from a legitimate company or investing substantial time and money into setting up a fraudulent corporate entity. The Trusted Signing pathway, by contrast, is markedly more accessible and economical.
Microsoft maintains that it actively monitors activity within the service and revokes certificates promptly upon detecting abuse. The company has stated that malicious files have already been identified and that the associated attacker accounts have been disabled.
Security experts warn that a standard Microsoft-issued certificate now suffices for malware to gain trusted status within the Windows ecosystem. Acquiring one is significantly easier than passing the rigorous scrutiny required for EV certification—especially when registering as an individual, which bypasses the need for a corporate track record of at least three years.
This development offers threat actors a low-friction, cost-effective vector for distributing malware with minimal resistance. While Microsoft currently addresses each violation manually, the risk of continued abuse remains a pressing concern.