Cybercriminals continue to refine their malware delivery mechanisms, and the latest iteration of Hijack Loader stands as a vivid testament to this trend. Researchers at Zscaler have uncovered a newly enhanced version of the loader—already popular among cyber threat actors for its adeptness at evading security defenses and discreetly deploying additional malicious payloads. The tool has now acquired capabilities for obfuscating the origin of system calls, detecting virtualized environments, and ensuring persistent foothold within infected systems.
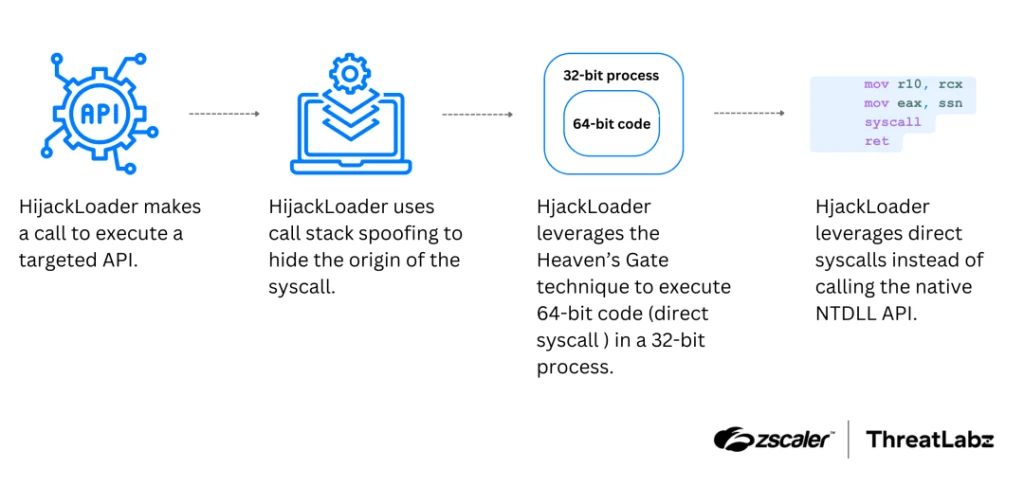
Foremost among the enhancements is the implementation of call stack spoofing, a technique that conceals the true source of API function invocations. This significantly complicates reverse engineering efforts, particularly within debugging frameworks and sandbox environments. By forging stack frames using manipulated EBP pointer chains, Hijack Loader substitutes genuine entries with fabricated ones, thereby obscuring traces of its malicious operations. A similar approach has recently been adopted by developers of another loader known as CoffeeLoader.
First identified in 2023, Hijack Loader has gone by multiple aliases—including DOILoader, GHOSTPULSE, IDAT Loader, and SHADOWLADDER. It serves as a conduit for delivering second-stage payloads, such as infostealers, and comes equipped with an extensive toolkit for antivirus evasion and code injection into legitimate processes.
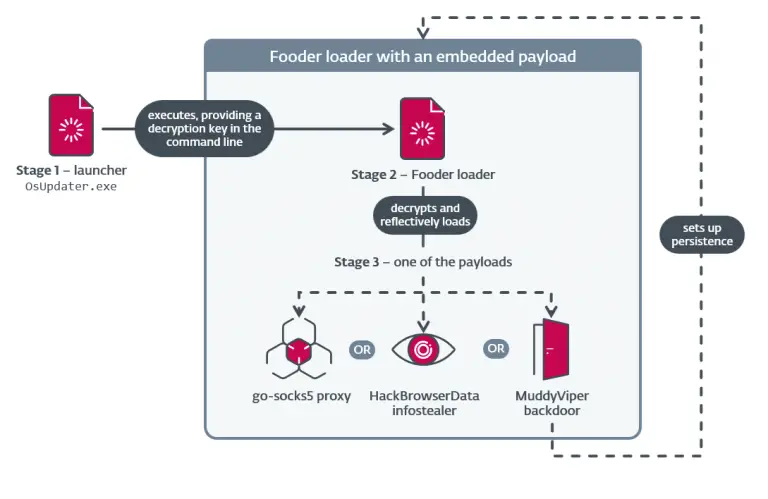
In the autumn of 2024, researchers from HarfangLab and Elastic Security Labs documented a campaign leveraging Hijack Loader, during which actors employed genuine code-signing certificates alongside the ClickFix technique—a widely-used ruse that disguises malware downloads as legitimate software updates.
Among the latest enhancements is an updated blacklist of processes, now including Avast’s antivirus component “avastsvc.exe.” Its detection triggers a five-second execution delay, likely designed to sidestep behavioral monitoring. The loader also employs the Heaven’s Gate technique, allowing direct system calls in 64-bit environments—an advanced method used to inject code into other processes without raising suspicion.
Two new modules have been added to the loader’s arsenal. The first, ANTIVM, is tailored to detect virtual machines and is presumed to be used for identifying analysis environments. The second, modTask, facilitates persistence by adding malicious tasks to the Windows Task Scheduler, enabling the malware to execute upon system startup without user interaction.
According to researchers, Hijack Loader remains under active development. Its creators are not only adapting to the evolving security landscape but are also deliberately integrating sophisticated evasion techniques to hinder cybersecurity professionals and prolong the viability of their malicious campaigns.