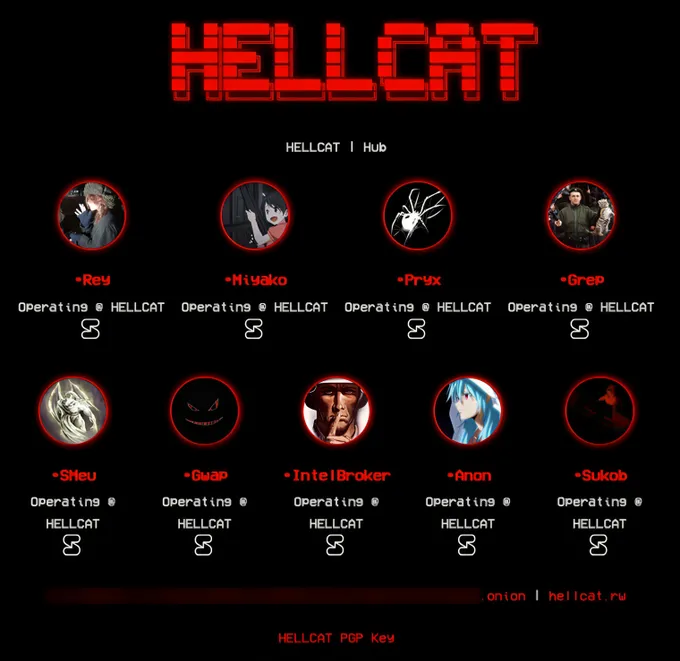
The Hellcat collective has found itself at the heart of a KELA investigation that has unveiled the true identities of two of its central figures—“Rey” and “Pryx.”
Originally known as the ICA Group, the syndicate had rebranded itself as Hellcat by late 2024, showcasing a heightened degree of coordination and hostility. The group drew notoriety following high-profile cyberattacks against Schneider Electric, Telefónica, and Orange Romania.
Rey first surfaced under the alias “Hikki-Chan” on BreachForums, where he disseminated purportedly exclusive data leaks—some of which were later revealed to be recycled from previous breaches. Despite his tarnished credibility, Rey reemerged under a new pseudonym and assumed administrative control of Hellcat.
He maintained an active presence on Telegram and X, where he routinely published data leaks, targeted telecom providers with caustic remarks, and distributed cyberattack tools alongside inflammatory rhetoric. Claiming expertise in cryptography, Rey recounted his hacking origins through website defacements. Of particular note was his method of leveraging Jira data to infiltrate corporate systems.
Using proprietary threat intelligence, KELA discovered that Rey had fallen victim to Redline and Vidar infostealer infections on two occasions in early 2024. One compromised device appeared to be shared with family members, ultimately leading to the identification of a young man named Saif from Amman, Jordan, whose identity is believed to correspond to Rey. Previously, he had used the aliases “ggyaf” and “o5tdev,” had been active on RaidForums and BreachForums, and publicly aligned himself with Anonymous Palestine.
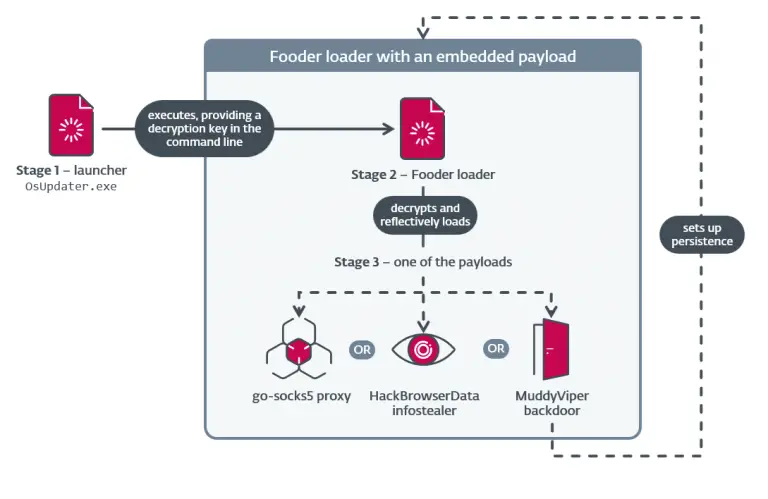
The second prominent member, Pryx, began his digital exploits in mid-2024, swiftly evolving from leaking data from educational institutions to targeting government systems in the Gulf and Caribbean regions, and later expanding his scope to private enterprises. He developed a proprietary cryptor based on AES-256 and authored technical guides for platforms such as XSS. He also managed the websites pryx.pw and pryx.cc.
According to KELA’s findings, Pryx was an Arabic speaker and had been involved in carding since at least 2018. He made inflammatory statements, including a terror threat directed at Harvard University. Among his tools was a server-side stealer that utilized Tor services for covert access to compromised machines, transmitting stolen data without triggering outbound network activity.
A technical analysis of one such tool led researchers to the domain pato.pw, which was originally framed as a resource for cybersecurity enthusiasts. However, code similarities and identical content linked the site directly to Pryx. The same guides published on the domain later appeared on forums under his alias. Further evidence was uncovered via matching GitHub repositories and email addresses, all tracing back to Telegram identities and pointing to an individual named Adem, residing in the UAE.
Deeper analysis revealed connections between Pryx and another hacker known as Weed or WeedSec. Through Telegram, investigators identified linked accounts, correspondence with a BlackForums administrator, and consistent reuse of login credentials. Additional confirmations of the name Adem in alternate contexts further solidified the association between Pryx and his real-world identity.
Despite their technical sophistication and combative tactics, both Rey and Pryx ultimately fell victim to the very infostealers they weaponized in their cybercriminal pursuits. This ironic twist enabled investigators to forge critical links and may mark a decisive step toward the unmasking of one of the most prominent hacker collectives in recent memory.