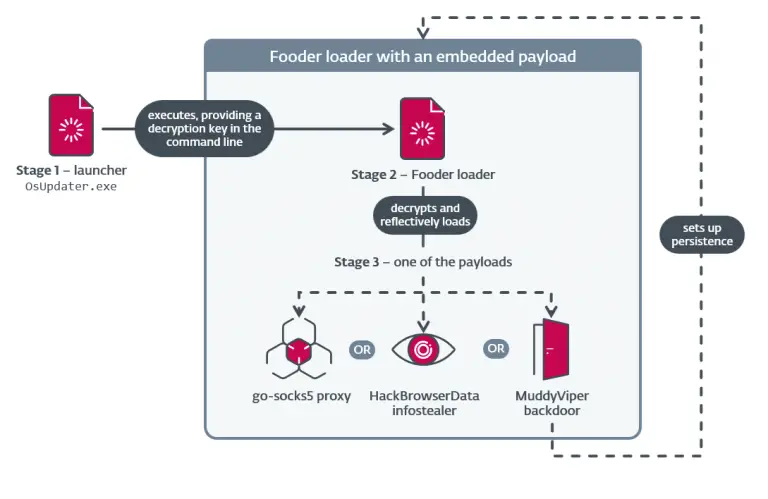
Researchers at SafeBreach have uncovered critical vulnerabilities in Google Quick Share’s file transfer feature, which could allow threat actors to remotely execute malicious code on Windows systems — entirely without user interaction. Although Google addressed the flaws following their presentation at DEFCON in August, two key elements of the attack chain had to be re-patched after researchers demonstrated that the original fixes could be bypassed within mere days.
Quick Share, Google’s counterpart to Apple’s AirDrop, enables file sharing via Bluetooth, Wi-Fi, NFC, and other channels across Android, Windows, and Chrome OS. The system appears well-designed on the surface: users specify who may send them files, and each incoming request requires manual approval. However, the researchers were able to circumvent both of these security mechanisms, constructing a full-fledged exploit dubbed QuickShell.
Using a custom-built tool called QuickSniffer, the team dissected the underlying file transfer protocol of Quick Share. It turned out to be relatively straightforward, based on the Nearby Connections API. They discovered it was possible to transmit files directly, bypassing the usual handshake process and approval prompt. Even the “contacts only” setting failed to block such transmissions — files could still be delivered regardless of user preferences.
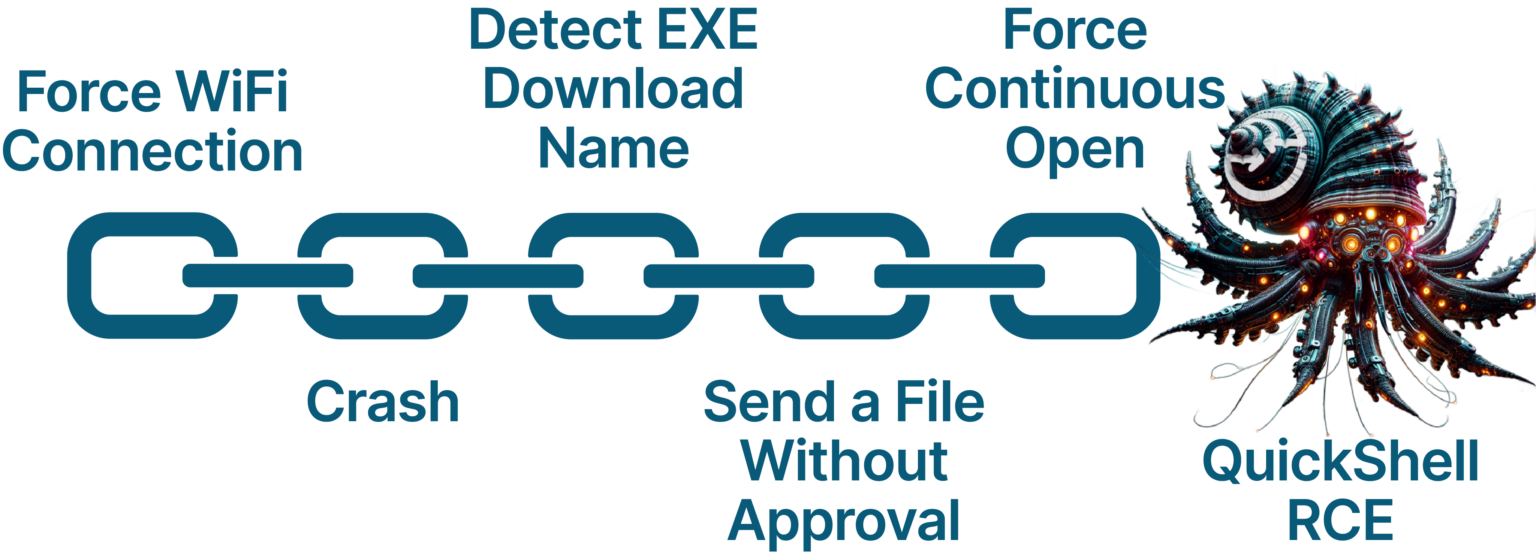
The most severe vulnerability (CVE-2024-38272), which enabled bypassing the file transfer confirmation prompt, received a CVSS score of 7.1. Another flaw (CVE-2024-38271) involved forcibly connecting the victim’s device to a rogue Wi-Fi network using an API feature intended to boost transfer speeds. This enabled the interception of the user’s network traffic for approximately 30 seconds.
Yet the true threat emerged when these vulnerabilities were chained together. The attacker, through the rogue network, would monitor when the victim downloaded an executable file, then seamlessly replace it with a malicious version delivered silently via Quick Share. Once the user launched the file, remote code execution was achieved.
To ensure reliability, the researchers leveraged additional, lesser-known bugs — including denial-of-service flaws to crash and restart Quick Share, keeping the victim tethered to the rogue Wi-Fi. They also exploited a quirk that forced files in the Downloads folder to open automatically, preventing Chrome from detecting the substitution.
Experts emphasize that seemingly minor bugs can become catastrophic when combined. It is their interplay — not their individual severity — that often elevates them to critical threats. Security assessments, therefore, must account for contextual risk, not just isolated technical scores.
As researcher Or Yair noted, the entire attack chain would have collapsed without the DoS vulnerability. He urged developers not to dismiss “the small stuff” — it is often these overlooked details that form the linchpins of sophisticated and dangerous exploit chains.