The cybercriminal group FIN7—also known by aliases such as Carbon Spider, ELBRUS, and Gold Niagara—has once again surfaced, this time deploying a tool named Anubis. Contrary to the well-known Android trojan of the same name, this Anubis is a newly developed Python-based malware designed for remote control over compromised Windows systems.
According to researchers at the Swiss cybersecurity firm PRODAFT, this malware grants threat actors access to the command line and critical system operations, effectively placing the infected machine under their full control.
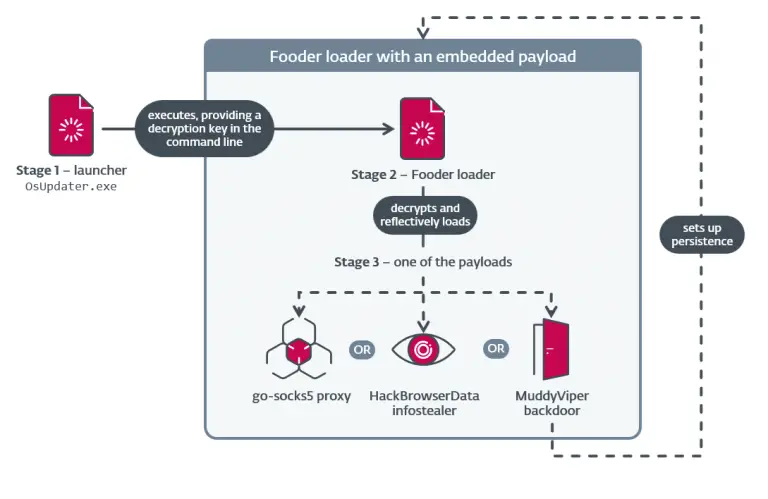
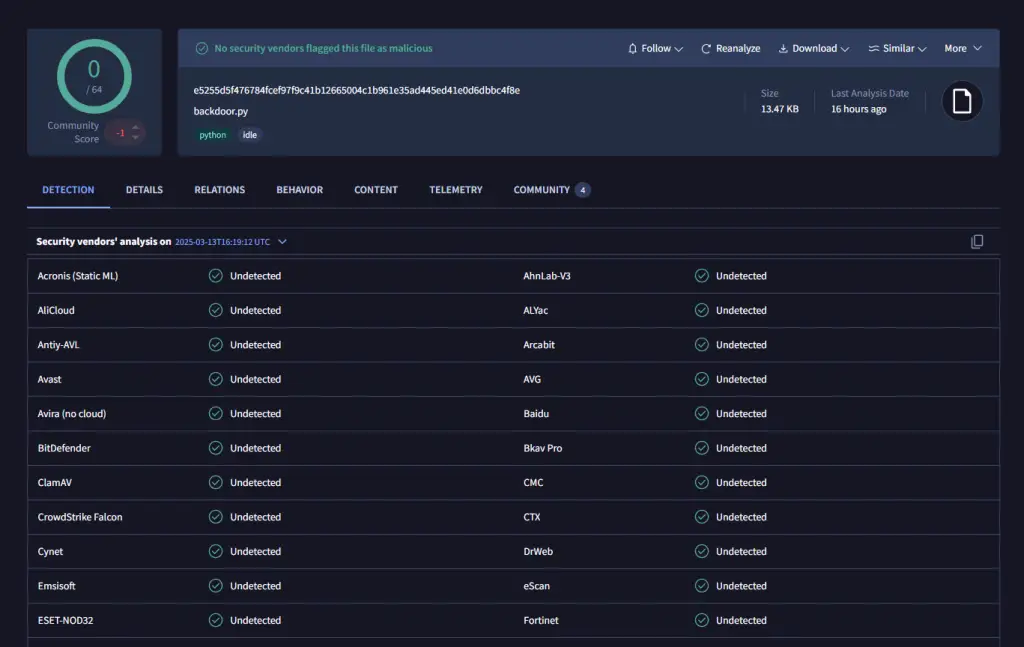
Anubis is propagated via malicious email campaigns leveraging compromised SharePoint sites. Victims are enticed into downloading a ZIP archive containing a Python script. Upon execution, the script decrypts and instantly runs an obfuscated core payload directly in memory. This in-memory execution technique avoids writing executable components to disk, thereby reducing the risk of detection.
Once activated, Anubis establishes a TCP socket connection with a remote command-and-control server, exchanging data encoded in Base64. The server’s responses are similarly encoded, complicating interception. The backdoor is capable of determining the device’s IP address, uploading and downloading files, altering the working directory, retrieving environment variables, modifying the Windows registry, injecting DLLs into memory, and terminating its own processes if necessary.
Further analysis by the German cybersecurity firm G DATA reveals that Anubis can execute arbitrary commands sent by the attacker. This capability enables real-time deployment of keyloggers, screen capture tools, and password theft utilities—none of which are stored persistently on the device, thereby enhancing operational stealth and maintaining modularity.
Over recent years, FIN7 has undergone a significant metamorphosis—from a traditional cybercriminal group into a highly adaptive entity aligned with ransomware operators. A notable milestone in its evolution was the promotion of AuKill in the summer of 2024, a tool designed to disable antivirus software and endpoint protection solutions, thereby clearing the path for follow-on attacks.
The current campaign involving Anubis further illustrates FIN7’s ongoing investment in expanding its offensive toolkit through increasingly sophisticated methods. Particularly concerning is their use of trusted platforms such as SharePoint for malware distribution, exploiting the inherent trust users place in legitimate services. This tactic is becoming alarmingly common in modern cybercrime.
Anubis functions as a versatile access tool, suitable for reconnaissance missions or as a launchpad for additional payloads. Its lightweight design and modular architecture allow seamless integration into a variety of attack scenarios, from targeted intrusions to widespread phishing operations.
Experts caution that these techniques may be employed in both broad campaigns and precision strikes against specific organizations. As a preventive measure, organizations are advised to remain vigilant when handling corporate files—especially those received via third-party platforms—and to monitor network activity for signs of anomalies.
This campaign serves as yet another stark reminder of the critical importance of timely security updates, thorough internal audits, and continuous staff education in threat recognition. FIN7 continues to exhibit a high degree of coordination and technical sophistication, cementing its position as one of the most formidable cyber threats active today.