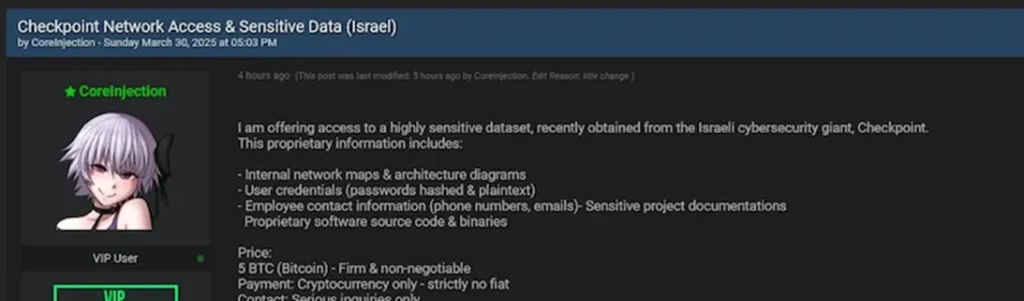
A storm is brewing around the Israeli cybersecurity firm Check Point, as a hacker operating under the alias CoreInjection has claimed to possess sensitive internal data and is offering it for sale at a price of five bitcoins—approximately $420,000 at the time of writing. While Check Point maintains that the breach stems from an old incident that did not compromise client infrastructure, posts circulating on the dark web and expert commentary cast doubt on this narrative.
According to the attacker, the trove includes internal network maps, architectural blueprints, passwords (both hashed and plaintext), employee contact details, technical documentation, and even source code. Also purportedly included are binary files and client-related materials, some referencing contracts valid through 2031.
The alleged breach was first brought to light on LinkedIn by Hudson Rock co-founder Alon Gal, who asserted with high confidence that an administrative-level account had been compromised. To support this claim, Gal shared screenshots from the Check Point Infinity management console showing admin-level API keys, options to edit user accounts and reset two-factor authentication, as well as client data.
Check Point responded by characterizing the incident as “known, old, and limited in scope,” emphasizing that it had no impact on production environments or clients’ security architecture. According to the company, the breach affected only three customers and was thoroughly investigated back in December 2024. At the time, the compromised credentials allegedly belonged to a portal account with limited access.
Nevertheless, Gal questioned the company’s assertions, highlighting discrepancies between the official statements and the contents of the leaked screenshots. Of particular concern were records of 121,120 user accounts and nearly 19,000 paying clients, complete with service details and contract durations.
Gal also raised a pointed question: why, if the breach involved such a volume of potentially sensitive data, was there no public disclosure or filing with the U.S. Securities and Exchange Commission (SEC)? Given that Check Point is a publicly traded company, he argued, transparency in such matters is not only warranted but essential.
Subsequently, Check Point issued a more detailed statement, reaffirming that the incident occurred in December and was confined to a small number of accounts. The company insisted that the hacker’s claims were exaggerated and misleading. They further stated that the portal in question is equipped with internal safeguards designed to contain any potential fallout from compromised credentials.
Yet critical questions remain unanswered—chief among them: the specific method of compromise and the technical pathway that allegedly enabled access to administrative privileges. While the company attributed the breach to “limited-access credentials,” it has not clarified how such credentials could yield full admin rights.
Skepticism over the company’s explanation is deepened by the hacker’s screenshots, which clearly show privileged access, fully functional API keys, and data unlikely to be exposed through a restricted account. The inconsistencies between the visual evidence and the company’s official line continue to fuel distrust.
While Check Point maintains there is no threat to customer security, the cybersecurity community remains divided—uncertain whether this is merely a “recycling of old data” or a sign of a deeper, as-yet-unrevealed vulnerability.