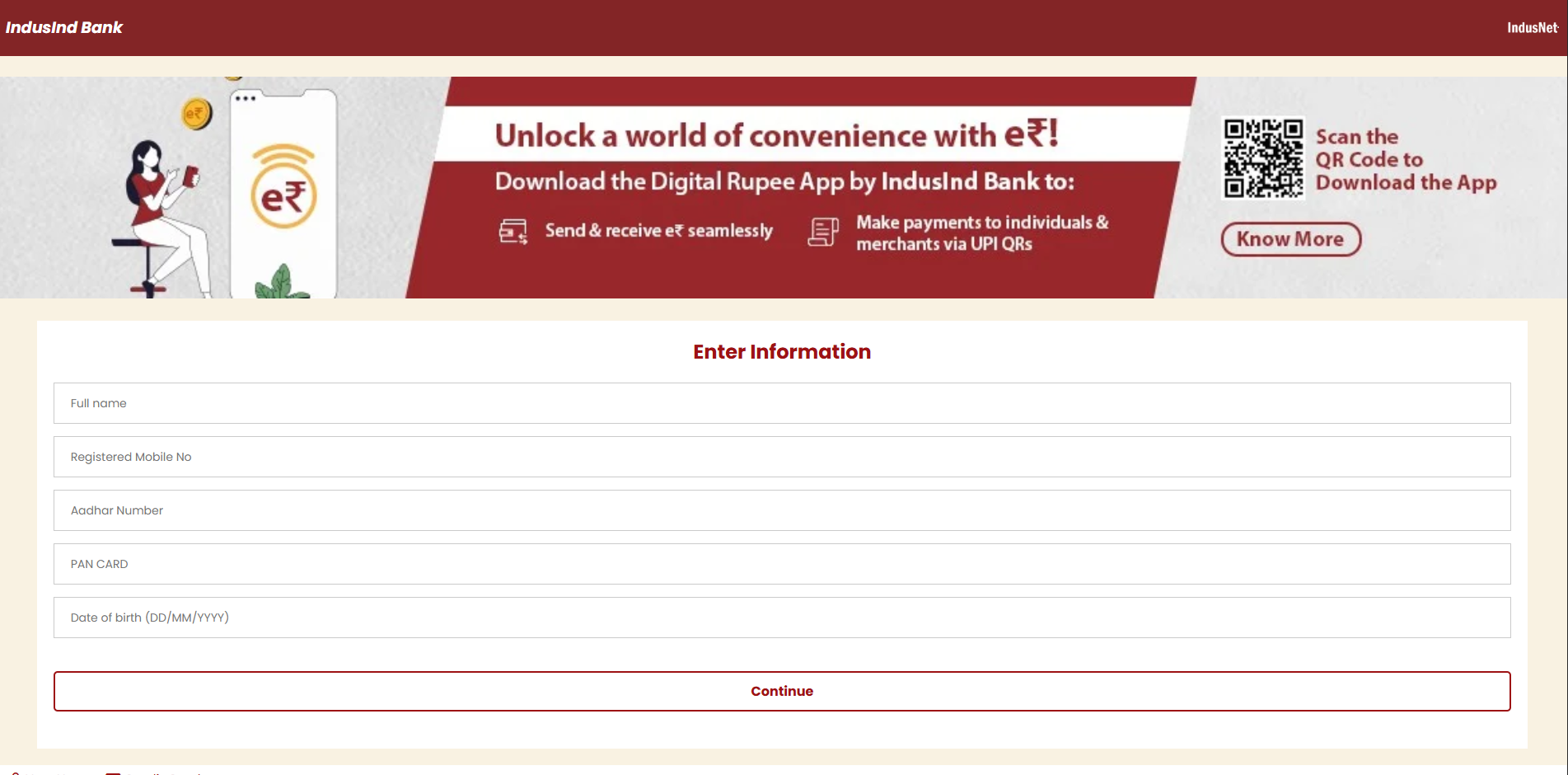
Phishing page that encourages victims to share their personal data
Analysts at ANY.RUN have uncovered a new strain of Android malware named Salvador Stealer, designed primarily for harvesting banking credentials and one-time passcodes (OTPs). The infection process begins with a dropper disguised as a legitimate banking application. Upon installation, it silently downloads and executes the main payload without the user’s awareness.
Salvador Stealer predominantly targets users in India, aiming to exfiltrate sensitive personal information such as mobile numbers, Aadhaar IDs, PAN card details, dates of birth, and internet banking credentials. All captured data is simultaneously transmitted to a spoofed phishing site and via Telegram through a bot. The embedded phishing page is crafted to precisely mimic the official banking interface, deceiving users into entering their confidential data.
A distinguishing feature of this malware is its ability to intercept incoming SMS messages, enabling attackers to acquire OTPs essential for bypassing two-factor authentication. Once intercepted, the sensitive information is transmitted either through SMS to a predefined number or via HTTP requests to a remote server—ensuring data exfiltration even under unstable network conditions.
The malware employs multiple persistence mechanisms. It automatically restarts if force-closed and reactivates upon device reboot, leveraging system broadcast receivers and high-priority services. Malicious code is embedded within various components, including concealed classes responsible for maintaining the malware’s presence in device memory.
Analysis of the malicious APK revealed that embedded data is encrypted using XOR with a static key, “npmanager.” Decryption uncovered a command structure responsible for message interception and data transmission. The malware utilizes WebView with active JavaScript to load the malicious page, which further monitors all AJAX requests, capturing and relaying user input to Telegram.
The infrastructure supporting Salvador Stealer was found to be partially exposed. The administrative panel and phishing pages were accessible without authentication. A WhatsApp number, registered in India, was also discovered on the server, potentially revealing the geographical origin of the malware’s operators.
Salvador Stealer poses a grave threat not only to individual users—through financial theft and privacy violations—but also to financial institutions, which face increased fraud incidents and erosion of consumer trust. Such threats continue to evolve in sophistication, blending phishing tactics, traffic interception, and resilient persistence mechanisms.
Experts emphasize that detecting these threats demands more than static analysis. Real-time behavioral observation using interactive sandboxes is crucial to monitor malware activity, uncover supporting infrastructure, and respond swiftly to emerging threats.