Security experts at Sucuri have uncovered a novel attack method in which cybercriminals exploit a special WordPress directory—“mu-plugins”—to conceal malicious code. This folder is designed for so-called must-use plugins that are activated automatically, without administrative input, and do not appear in the standard plugin interface. Such behavior makes it an ideal location for surreptitious deployment of harmful components.
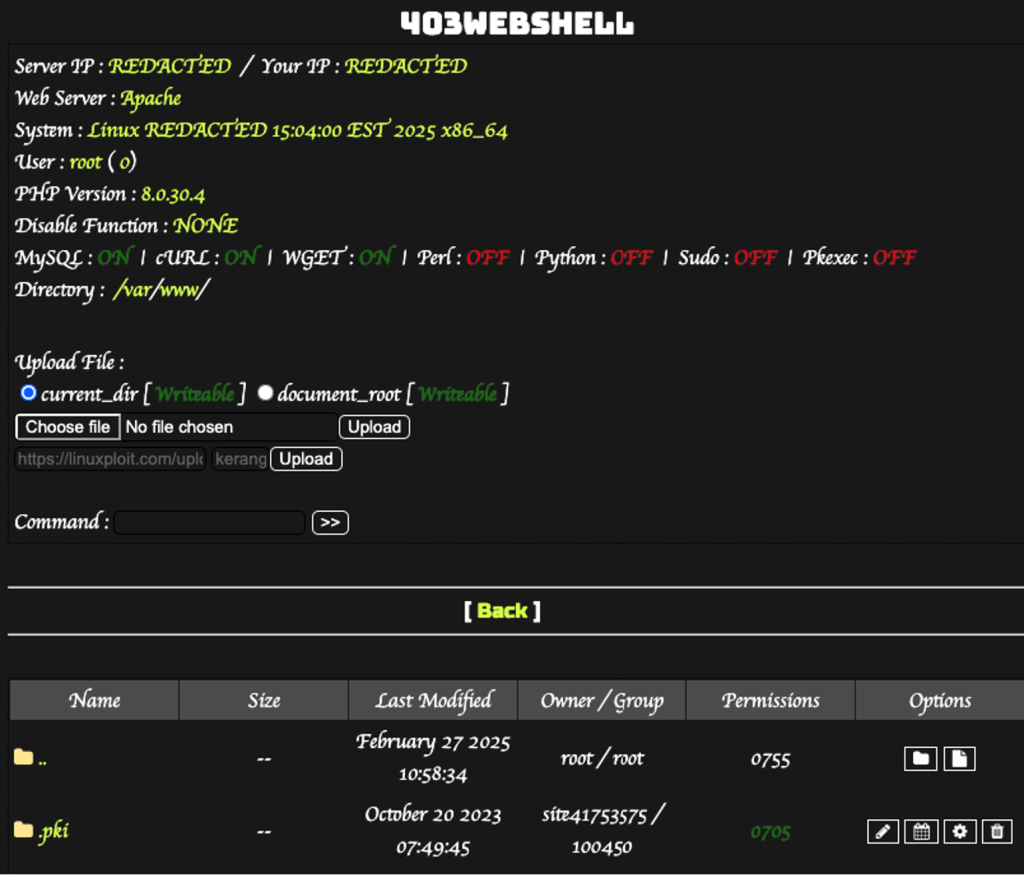
According to the researchers, several incidents revealed three distinct variants of malicious PHP files residing within this directory. One such file, redirect.php, executed covert redirections to external websites disguised as browser updates. Another, index.php, enabled remote code execution by loading scripts from GitHub. A third, custom-js-loader.php, injected unsolicited spam, replaced legitimate images with explicit content, and rerouted outbound links to fraudulent sites.
The method’s insidiousness lies in its capacity to detect whether a site visitor is a search engine bot. If so, the redirection is suppressed, thereby evading detection during indexing. This evasion technique enhances the attack’s stealth and makes it especially dangerous for unsuspecting users.
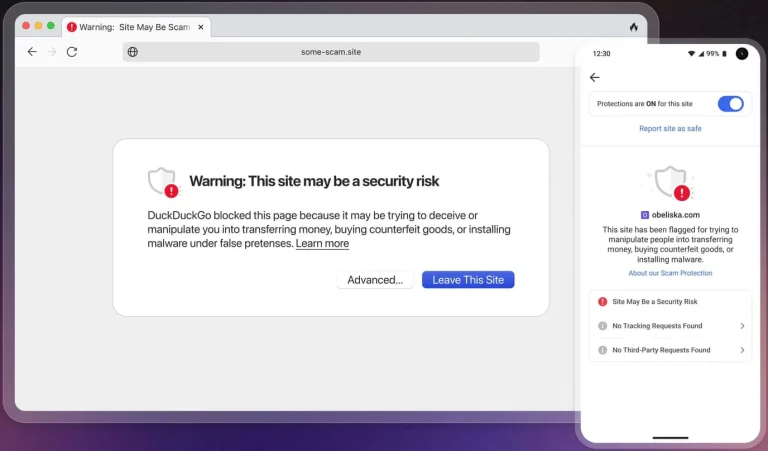
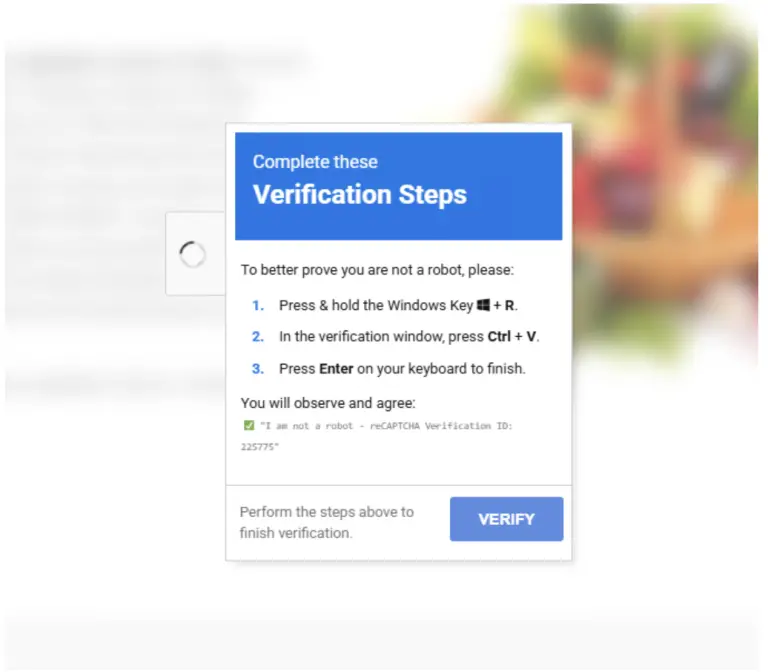
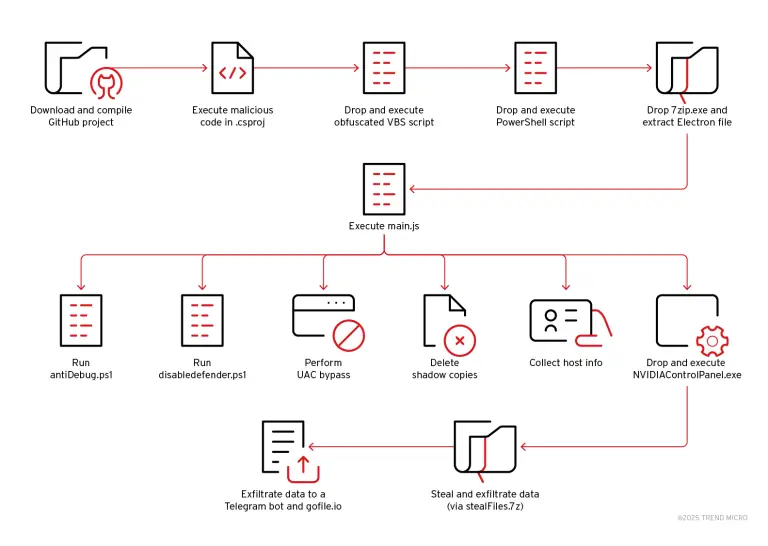
Experts note that this tactic is part of a broader campaign wherein compromised WordPress sites serve as launchpads for further malicious operations. In some cases, users are prompted to complete fake reCAPTCHA or Cloudflare CAPTCHA checks, which, when interacted with, trigger the delivery of malicious PowerShell commands and the installation of the Lumma Stealer trojan.
Simultaneously, infected sites may host malicious JavaScript designed to harvest payment data entered on checkout pages. Simpler variations involve redirecting user traffic to fraudulent websites.
Although the precise techniques used to compromise these sites remain uncertain, it is suspected that attackers exploit vulnerabilities in plugins and themes, or gain access through stolen credentials and misconfigured servers.
According to a recent Patchstack report, four critical vulnerabilities in WordPress plugins have already been actively exploited since the beginning of the year. These include a flaw in the WordPress Automatic Plugin (CVE-2024-27956) allowing arbitrary SQL queries, as well as severe issues in the Bricks theme and the GiveWP and Startklar Elementor Addons plugins, which permit unauthenticated code execution and malicious file uploads.
To mitigate these risks, experts strongly advise timely updates of plugins and themes, regular scans for suspicious file changes, the use of complex passwords, and the implementation of web application firewalls. These precautions can help filter out malicious requests and prevent the injection of harmful code.