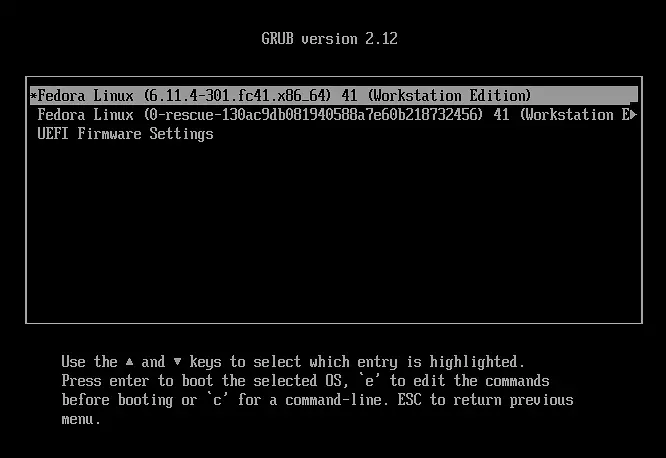
Microsoft has announced the discovery of 20 new vulnerabilities within the GRUB2, U-Boot, and Barebox bootloaders. The investigation focused on the earliest stages of the boot process—a critical window in which the system has yet to activate its core security defenses.
GRUB2, the default bootloader in many Linux distributions including Ubuntu, was found to contain 11 flaws. These include issues in filesystem handling, improper processing of symbolic links, and weaknesses in cryptographic comparison logic. U-Boot and Barebox—commonly deployed in IoT and embedded systems—were also affected, with nine vulnerabilities linked to buffer overflows when parsing various filesystem formats.
Although exploitation requires physical access to a device, such prerequisites do not eliminate the possibility of serious attack scenarios. History has shown that boot-time compromise is feasible, as demonstrated in the infamous BlackLotus malware campaign.
What makes these flaws particularly dangerous is their potential impact on the UEFI Secure Boot mechanism. Under specific conditions, the vulnerabilities could allow attackers to bypass this protection and execute malicious code before the operating system has even begun to load. This opens the door to bootkits and full system compromise.
Microsoft emphasized that such attacks can persist even after disk formatting or operating system reinstallation. Once an attacker seizes control of the boot process, they can embed backdoors and use the device as a launch point for further infiltration within a network.
The most severe of the newly identified flaws, CVE-2025-0678, carries a CVSS score of 7.8 and involves a buffer overflow when reading Squash4 files. The remaining ten GRUB2 vulnerabilities are considered medium severity and include faults in the handling of HFS, UFS, ReiserFS, JFS, RomFS, UDF, and other components.
Notably, Microsoft credited its Security Copilot tool with accelerating the code analysis by at least a week compared to manual auditing. Beyond detection, the AI-driven assistant also offered remediation strategies, proving particularly beneficial to smaller open-source projects.
Due to shared code among GRUB2, U-Boot, and Barebox, several of the discovered bugs were replicated across projects. All three bootloaders issued security updates in February 2025, and applying the latest versions mitigates the vulnerabilities identified.