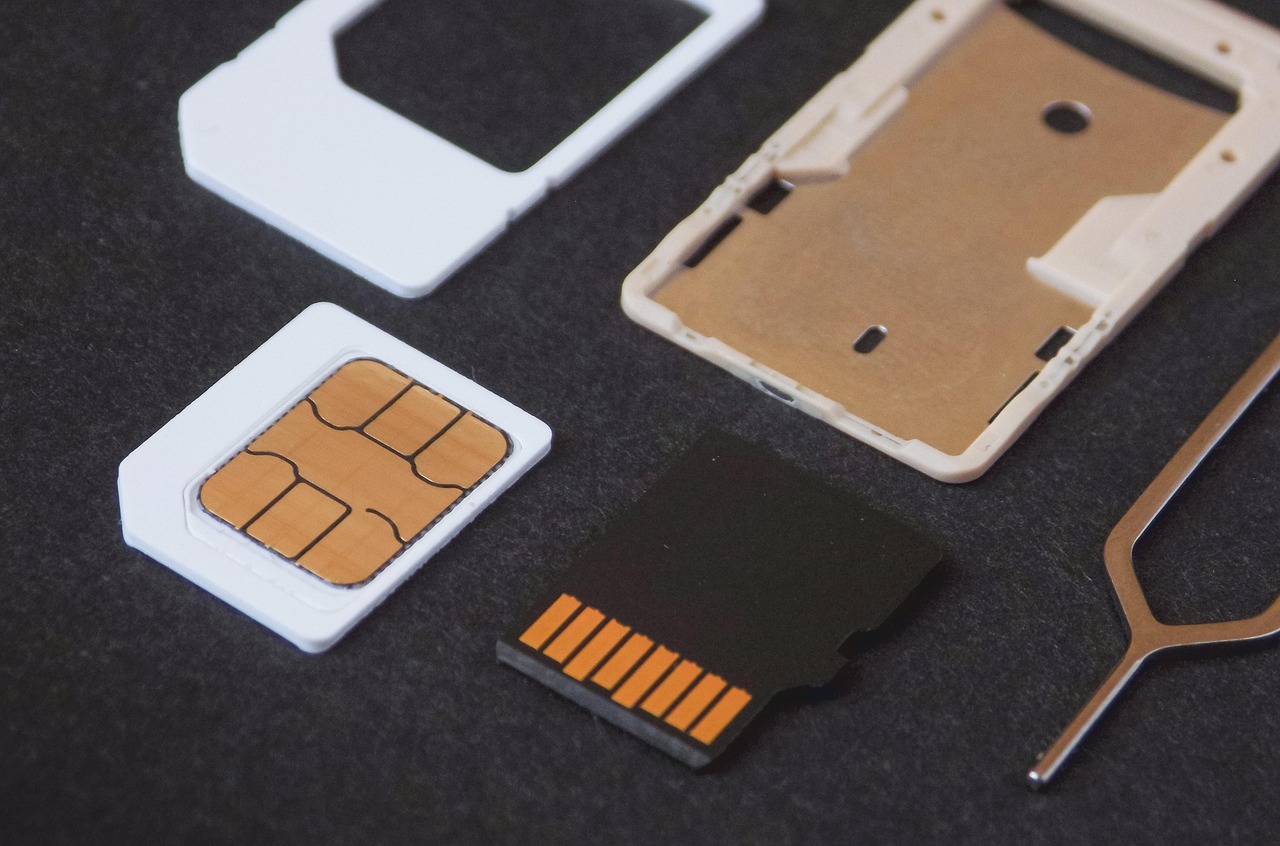
The California-based law firm Greenberg Glusker has secured a $33 million arbitration award against T-Mobile, following a grave security lapse that enabled a successful SIM-swapping attack.
The incident occurred on February 21, 2020, when a T-Mobile employee transferred the phone number of client Joseph “Josh” Jones to a SIM card under the control of a malicious actor. As a result of the breach, more than 1,500 Bitcoins and approximately 60,000 Bitcoin Cash were stolen—assets valued at $38 million at the time.
Jones’s T-Mobile account was protected by enhanced security measures, including an eight-digit PIN code designed to prevent unauthorized changes. This led the victim to suspect that the attackers had exploited a vulnerability within the mobile carrier’s systems to gain control over his account.
Greenberg Glusker’s petition to confirm the arbitration award—filed in Los Angeles court and obtained by SecurityWeek—reveals that law enforcement investigations identified a 17-year-old with ADHD as being involved in the hack. The teenager was reportedly connected to cybercriminals Nima Fazeli and Joseph O’Connor, both implicated in the 2020 breach of dozens of Twitter accounts.
The arbitration ruling had remained confidential since the fall of 2023. According to the law firm, T-Mobile had sought to keep the details regarding its security deficiencies out of public view.
Paul Blecher of Greenberg Glusker emphasized that SIM-swapping has long persisted as a glaring security vulnerability. He noted that telecommunications providers, including T-Mobile, were well aware of the threat, yet failed to implement adequate safeguards to protect their customers.
SIM-swapping poses a severe risk, particularly because phone numbers are frequently used for two-factor authentication across a wide range of online services. Once in control of a victim’s number, attackers can hijack login credentials and gain unauthorized access to sensitive accounts.
One of the most high-profile instances of this attack vector was the infamous 2020 Twitter breach, in which hackers targeted 130 accounts and successfully commandeered 45 of them, including profiles belonging to high-profile individuals such as Bill Gates, Jeff Bezos, Joe Biden, Elon Musk, and Michael Bloomberg.
Support Our Threat Intelligence
If you find our technology report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee