Several weeks ago, Argentine users began reporting unusual incidents of Telegram account compromises to cybersecurity experts. What made the situation particularly alarming was that the takeovers occurred without any action on the part of the victims. The attacks succeeded even against individuals who meticulously adhered to fundamental principles of digital security.
The investigation revealed that these were not isolated cases. Threat actors were deliberately targeting members of specific Telegram groups, predominantly linked to Argentina’s cryptocurrency communities. In every instance, the attackers initiated the dispatch of SMS messages containing two-factor authentication (2FA) codes. Subsequent login records exhibited identical entries:
A meticulous analysis of the compiled data traced the earliest attacks to February 7 of this year. The threat group was assigned the codename SLOVENLY COMET. Experts are urging anyone with relevant information about these attackers to contact: tips-slovenly-comet@securityalliance.org.
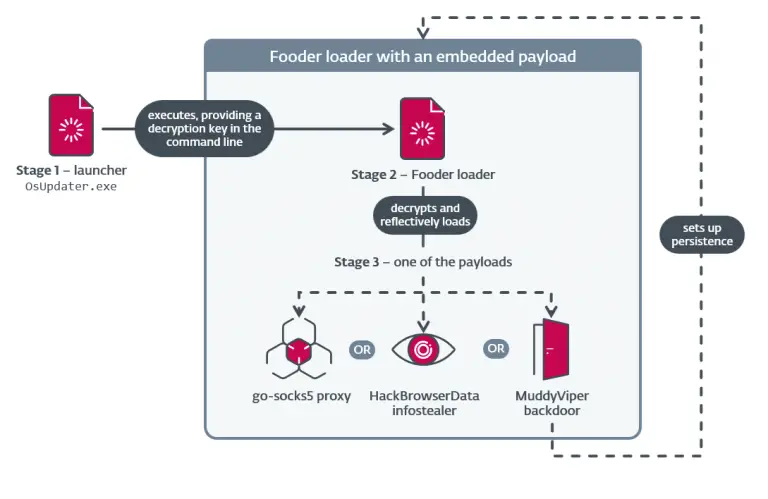
After vetting several hypotheses, an international team of researchers, working alongside local specialists, proposed a theory involving the compromise of SMS gateways. Further analysis of screenshots, system logs, and leaked data substantiated the theory. Investigators uncovered a Telegram bot that had been systematically intercepting messages containing authentication codes. Its archive held tens of thousands of entries in this format:
The authenticity of these records has been confirmed—indicating that the breach persisted for weeks without detection.
The scale of the threat turned out to be far greater than initially presumed. Given that most companies rely on a handful of major SMS providers, the attackers gained access to 2FA messages from a broad range of services, including Google, Microsoft, Apple, Telegram, Facebook, Mercadolibre, Amazon, Binance, Betfun, Instagram, TikTok, Temu, and Signal. Regional platforms were also affected—Mercado Pago, Mi Argentina (Argentina), Banco Formosa (Uruguay), and TRANSVIP (Chile). In total, at least 50 different platforms are believed to have been compromised.
The vulnerability was traced to a core component of SMS infrastructure. All relevant organizations, telecom operators, and government agencies have been notified. An investigation is currently underway, alongside the development of protective countermeasures.
Further details are expected in the coming days, as the affected companies prepare to release findings from their own internal inquiries. In the meantime, service developers are strongly encouraged to move away from SMS-based 2FA—a method long known to be susceptible to interception—and instead offer users secure alternatives, such as authenticator apps or hardware security keys.
Users are advised to review the security settings on their devices and report any suspicious activity to law enforcement authorities.