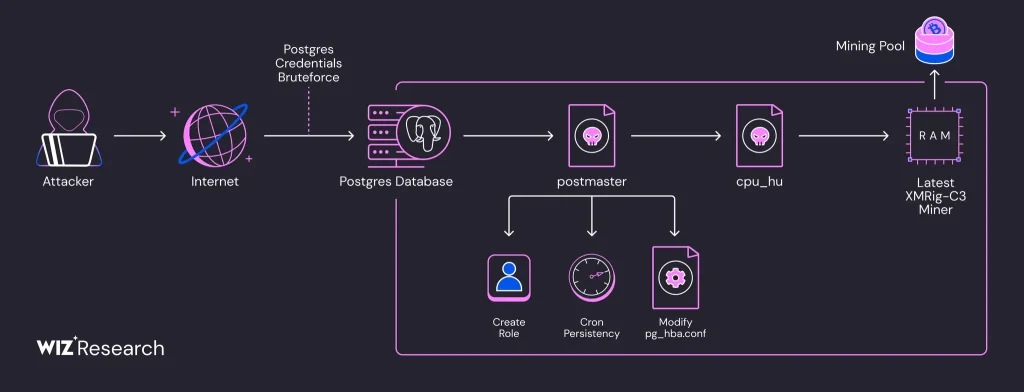
In the course of an ongoing malicious campaign, over 1,500 PostgreSQL servers have been compromised and repurposed for covert cryptocurrency mining. Researchers at Wiz revealed that the attackers operate entirely in-memory, without writing files to disk—a tactic that significantly hampers detection. The campaign is attributed to a threat group dubbed JINX-0126 and builds upon a previously identified malware tool known as PG_MEM, first documented by Aqua Security in August 2024.
Unlike earlier attacks, this wave employs a more sophisticated strategy aimed at evading security mechanisms. Malicious binaries are uniquely hashed per target, and the miner itself is deployed without creating any files on the host system. This fileless methodology effectively bypasses defenses that rely on signature-based detection of known file hashes.
The primary targets are publicly accessible PostgreSQL instances protected by weak or easily guessable passwords. According to Wiz, the prevalence of such poorly secured systems makes them an appealing target for large-scale exploitation. More than 1,500 servers have been confirmed compromised, underscoring the campaign’s breadth.
A hallmark of this operation is the exploitation of the SQL command COPY ... FROM PROGRAM, which enables the execution of arbitrary shell commands directly from within the database server. This access is leveraged for reconnaissance and the injection of malicious code. One of the initial steps involves downloading an encrypted shell script that eliminates competing miners and installs a binary component called PG_CORE.
The attackers also deploy a disguised Go-based binary named postmaster, crafted to mimic the legitimate PostgreSQL service. This component ensures persistence by creating cron jobs, establishing privileged user accounts, and storing an auxiliary file named cpu_hu.
The cpu_hu binary is responsible for retrieving the latest version of XMRig, a well-known cryptocurrency mining tool. Notably, the campaign employs a fileless execution technique on Linux systems using the memfd mechanism, which allows the binary to reside solely in memory—bypassing traditional disk-based detection.
Each infected machine is assigned a unique identifier. Wallet analysis linked to the campaign reveals approximately 550 active miners associated with each of three wallet addresses, confirming the involvement of at least 1,500 machines.
The core pillars of this attack include the exploitation of misconfigured PostgreSQL servers, the adept use of evasion techniques, and the complete avoidance of filesystem footprints. This combination renders the campaign both highly effective and remarkably resilient against conventional detection methods.